Vulnerability Intelligence
Improve your security vigilance with Vulnerability Intelligence, offering advanced alerts for critical vulnerabilities.
Protect your digital assets with SOCRadar’s Vulnerability Intelligence. Get instant alerts and actionable insights to safeguard against potential threats.
Proactive Defense Against Emerging Vulnerabilities
In a digital ecosystem where threat actors constantly seek to exploit vulnerabilities, staying informed is key to protection. SOCRadar’s Vulnerability Intelligence provides an advanced alert system, notifying you of new critical vulnerabilities or exploits in your public-facing services and technologies. This proactive approach is essential to secure your business against disruptive breaches.
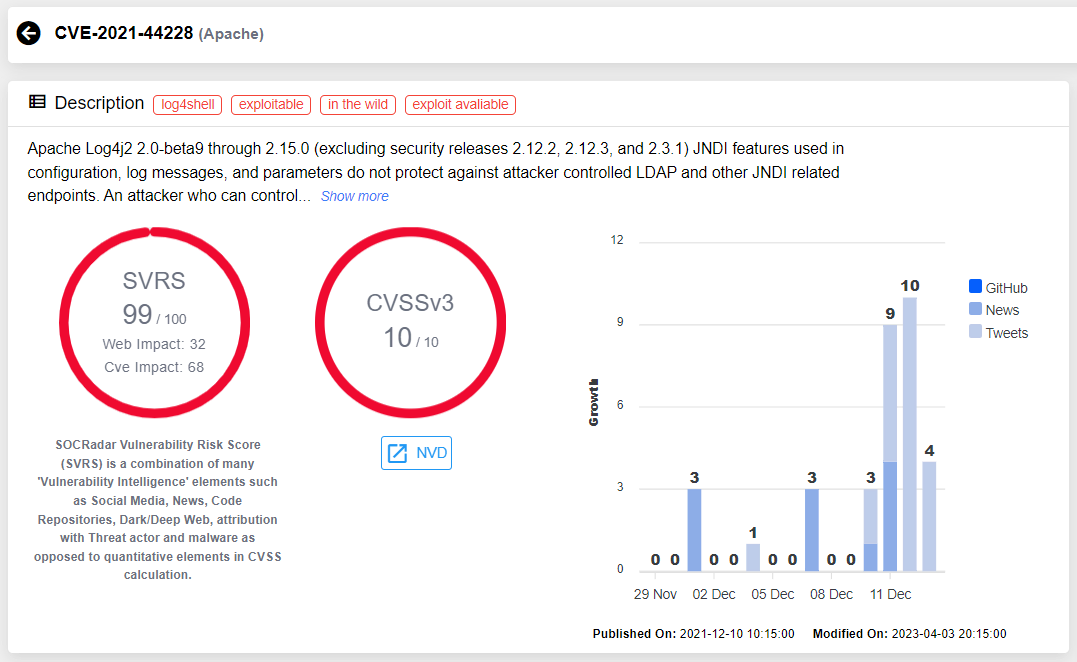
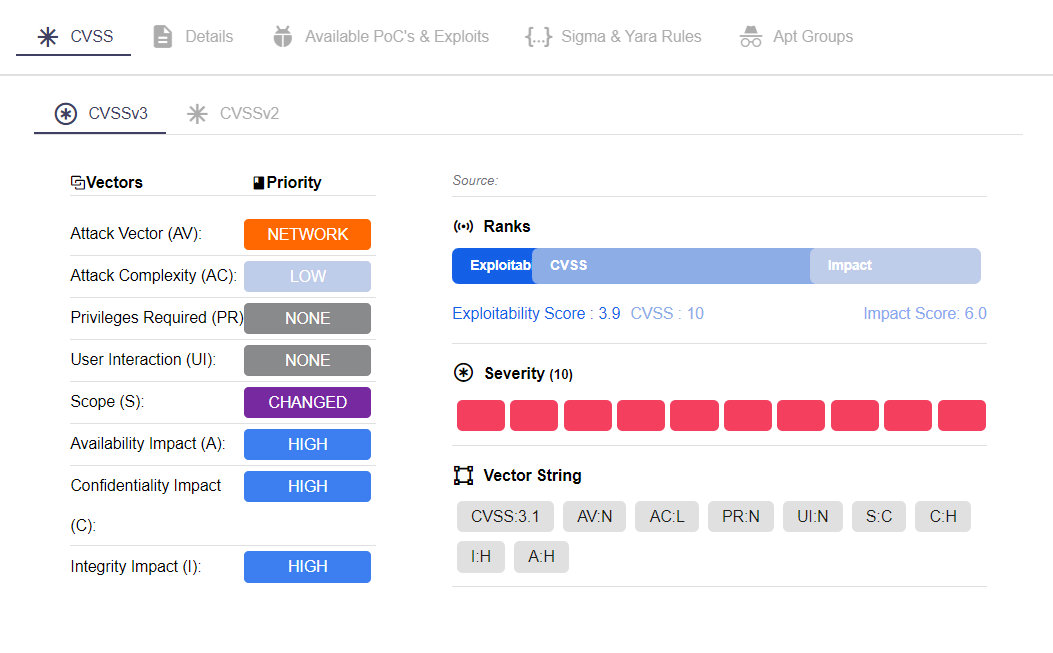
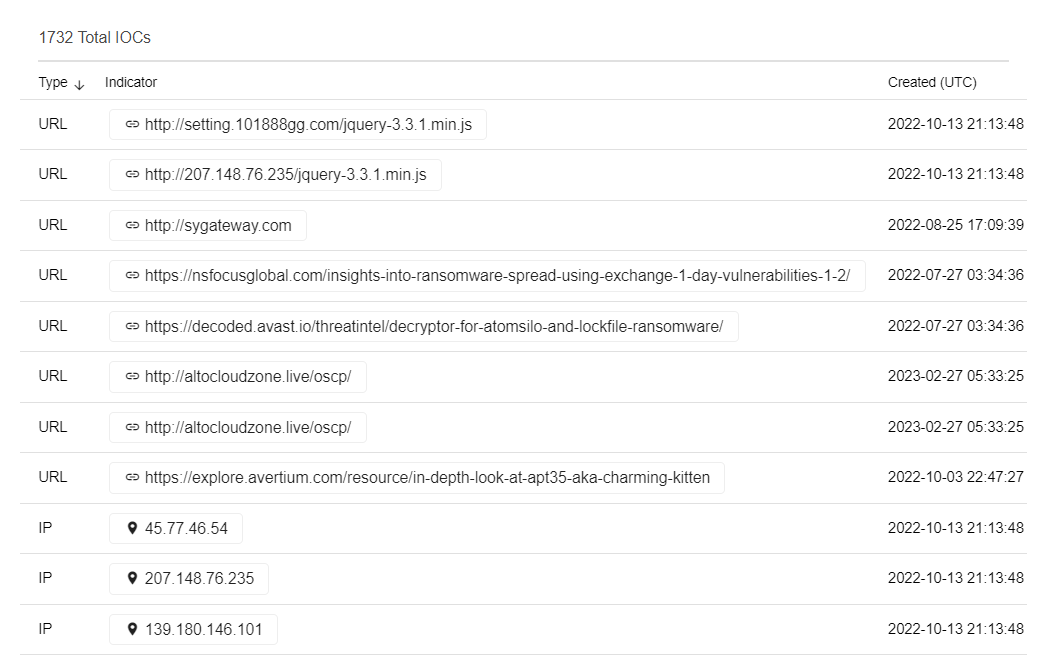
Insights into Exploited Vulnerabilities
Understanding the current cyber landscape is key to strengthening your defenses. With SOCRadar’s Vulnerability Intelligence, gain valuable insights into which vulnerabilities are being actively exploited. This intelligence delivers actionable information on potentially vulnerable technologies, allowing you to make informed decisions. By staying informed about the latest threats, you can adapt your security measures to address these vulnerabilities effectively.
Accelerated Assessment and Swift Response
The speed and efficiency of your response to cyber threats can significantly impact your organization’s security. SOCRadar’s Vulnerability Intelligence enhances your response capabilities, enabling you to accelerate the assessment and verification process. Respond swiftly and decisively to vulnerabilities, thereby fortifying your security against potential breaches.
Tailored Monitoring for Your Needs
Every organization has unique security needs and challenges. SOCRadar’s Vulnerability Intelligence service is highly customizable, allowing you to select specific products and technologies for monitoring. This tailored approach ensures that the alerts and insights you receive are precisely aligned with your organization’s digital footprint and security requirements.
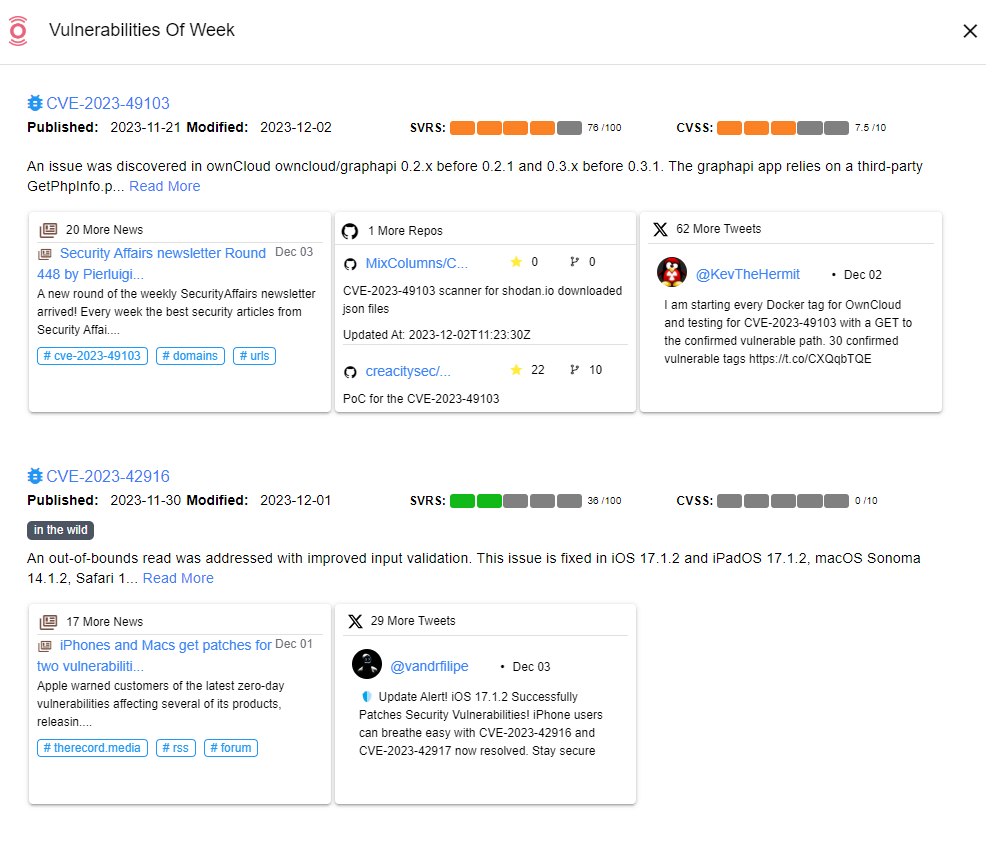
Global Vulnerability Trends at Your Fingertips
A broad perspective on emerging vulnerabilities is essential in a globally connected digital world. SOCRadar’s Twitter CVE Trends feature provides a unique window into worldwide vulnerability trends by monitoring millions of tweets. This feature offers insights into global cyber threat dynamics, helping you understand how emerging vulnerabilities might impact your organization.
Instant Alerting for Timely Action
Timeliness is critical in cybersecurity. SOCRadar’s instant alerting feature ensures that you receive rapid notifications about new vulnerabilities as they are discovered. This quick data collection, structuring, and analysis enable on-time responses, crucial for securing your systems against imminent threats.
Efficient Filter and Search Capabilities
Navigating the vast amount of vulnerability information available can be daunting. SOCRadar’s efficient filter and search functionality allows you to quickly find specific information on vulnerabilities. Filter data based on keywords, CVSS scores, or report times to streamline your vulnerability management process, saving time and resources.