1,200 Redis Servers Infected by New HeadCrab Malware for Cryptomining Operations
A new malware has appeared on the frontlines, targeting online Redis servers. The malware, named HeadCrab by researchers, has been active since September 2021. The malware’s primary goal is to create a botnet for Monero (XMR) cryptocurrency mining operations.
So far, the malware has infected at least 1,200 online Redis servers. Threat actors could use these infected servers to seek new targets and spread further.

How Does the HeadCrab Malware Infect?
According to researchers, the HeadCrab malware is undetectable by traditional agentless anti-virus solutions, allowing it to stealthily compromise many Redis servers.
Most malware is built on Redis processes, which are not likely to be reported as malicious. Kernel modules are loaded directly from memory, avoiding disk writes, and payloads are loaded via memfd, memory-only files.
Redis servers are intended for use within a company’s network. If administrators configure Redis servers to be accessible via an external network, it could allow attackers to compromise and eventually hijack these servers, adding them to the botnet.
When using HeadCrab malware on these Redis servers, threat actors rely on them not enabling authentication by default. Once threat actors gain access to Redis servers, they issue a “slaveof” command to connect to an attacker-controlled master server and install the HeadCrab malware on the infected system.
HeadCrab Malware Evades Detection
The attackers have all the capabilities to acquire complete control of the targeted server and add it to their cryptomining botnet after HeadCrab has been installed and launched.
Additionally, it will operate in memory on infected devices to avoid anti-malware scans. Examined samples have returned no results on VirusTotal.
To avoid detection, the attacker communicates with legitimate IP addresses. It also deletes all logs and only communicates with other servers under the control of its masters.
To make attribution and detection more difficult, researchers discovered that the attackers primarily use mining pools hosted on previously compromised servers.
The Monero wallet associated with this botnet also revealed that the attackers are earning an estimated $4,500 per worker annually, significantly higher than the typical $200 per worker in comparable attacks.
Recommendations
Admins are recommended to secure their Redis servers by limiting access to only clients within their network, turning off the slaveof function if it is not necessary. It is also recommended to enable protected mode, which sets the instance to only accept connections from the loopback address and reject connections from other IPs.
Get Ahead of Potential Threats with SOCRadar
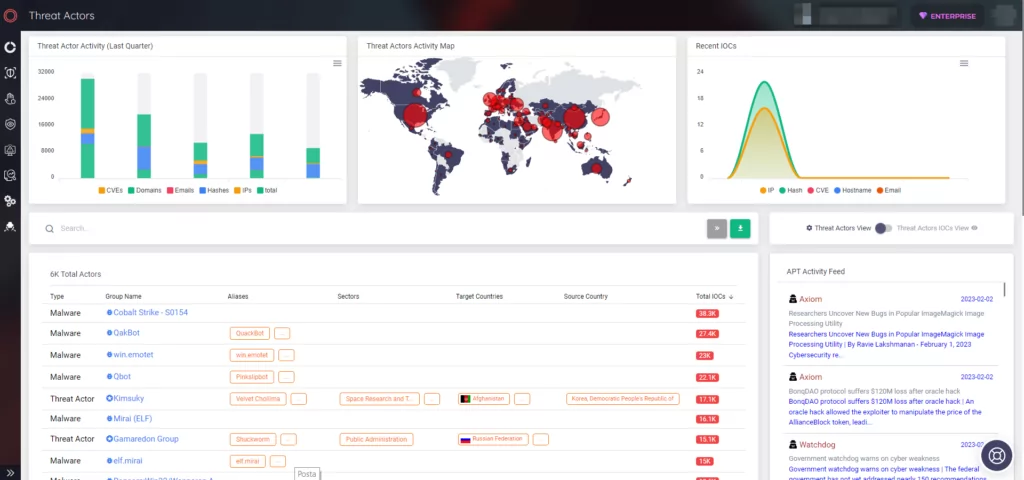
Learn more about threat actors’ activities on the platform. SOCRadar provides insights into threat actors’ past and current activities to protect your organization.
Using the Threat Actor panel on SOCRadar, you can see TTPs, related indicators of compromise, and threat actors’ targets.
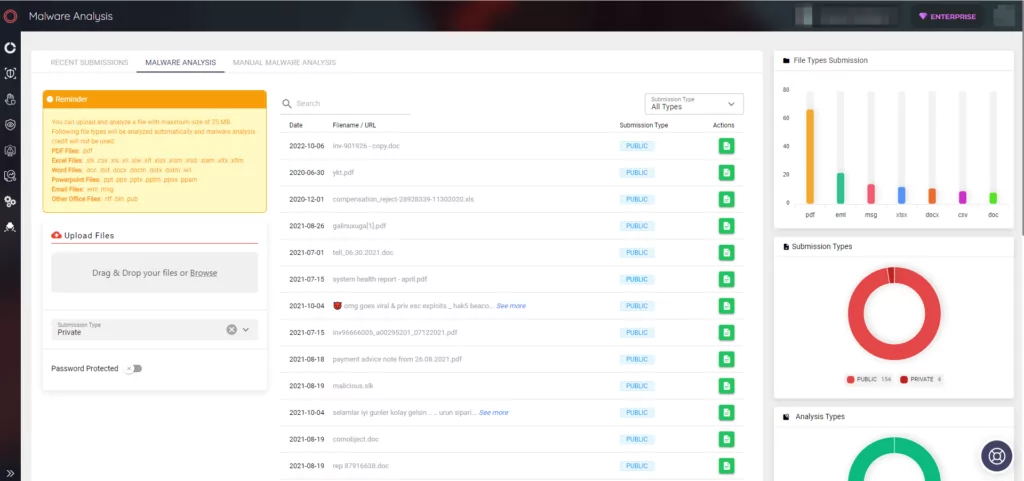
You can also use SOCRadar’s Malware Analysis panel to determine if a suspicious file involves any malware and see the analysis results as a report. The report includes information about the identified malware’s name, type, ID, hashes, and related security rules.