
Top 10 Identity Attack Techniques Used by Hackers
Top 10 Identity Attack Techniques Used by Hackers Most cyberattacks today start with a compromised identity. Stolen passwords, hijacked sessions, forged authentication tokens, and bypassed MFA are now...

WhatsApp 3B Dump, OnlyFans 340M Records Sale, BlockFi Email Leak, Rame...
WhatsApp 3B Dump, OnlyFans 340M Records Sale, BlockFi Email Leak, Ramen Kuroda Data Leak, and VSP Security Wholesale Breach SOCRadar Dark Web Team detected several new underground posts this week, inc...

TrapDoor: Malicious npm, PyPI, Crates.io Packages Target Developer Sec...
TrapDoor: Malicious npm, PyPI, Crates.io Packages Target Developer Secrets & AI Tooling Researchers identified a coordinated supply chain malware campaign named TrapDoor, involving waves of malici...
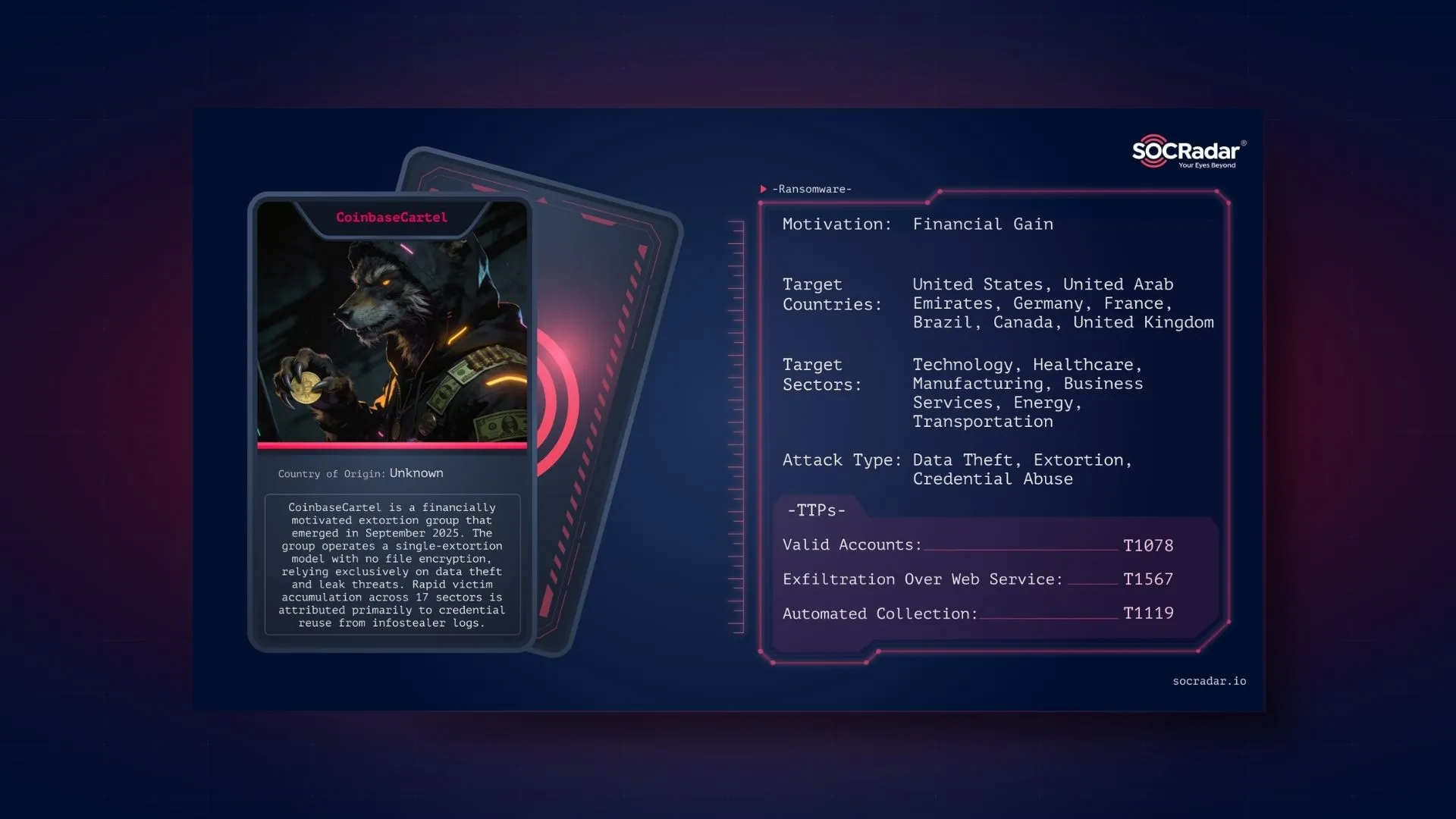
Dark Web Profile: CoinbaseCartel
Dark Web Profile: CoinbaseCartel CoinbaseCartel is a financially motivated threat actor that emerged on the Dark Web in September 2025. Unlike traditional ransomware groups, the group does not encrypt...

CVE-2026-20223: Cisco Secure Workload Auth Bypass Grants Site Admin Ac...
CVE-2026-20223: Cisco Secure Workload Auth Bypass Grants Site Admin Access Cisco has patched a maximum-severity vulnerability in Cisco Secure Workload (CSW) Cluster Software tracked as CVE-2026-20223....

How Dark Data Leaves Security Teams One Step Behind
How Dark Data Leaves Security Teams One Step Behind Cyber Threat Intelligence has come a long way. In the past, real-time threat feeds, dark web monitoring, and indicator-sharing platforms were reserv...

CVE-2024-12802: SonicWall SSL-VPN MFA Bypass Persists on Gen6
CVE-2024-12802: SonicWall SSL-VPN MFA Bypass Persists on Gen6 CVE-2024-12802 is an authentication bypass that can result in an SSL-VPN MFA bypass affecting SonicWall SonicOS / SonicWall SSL-VPN when t...
Verizon 2026 DBIR: 10 Takeaways You Should Know
Verizon 2026 DBIR: 10 Takeaways You Should Know Verizon’s 2026 Data Breach Investigations Report (DBIR) analyzes more than 31,000 security incidents and 22,000 confirmed breaches across organizations ...

TeamPCP GitHub Breach: Internal GitHub Repositories Allegedly Accessed
TeamPCP GitHub Breach: Internal GitHub Repositories Allegedly Accessed TeamPCP is back in the headlines, and this time the target is not a plugin, a CI/CD pipeline, or an open-source package. The grou...

B1ack's Stash Releases 4.6 Million Stolen Credit Cards for Free
B1ack’s Stash Releases 4.6 Million Stolen Credit Cards for Free A notorious Dark Web carding marketplace is making headlines again. B1ack’s Stash, one of the most active illicit card shops on the Dark...

EDR Terminator Sale, Alleged Adobe Business Leak, Serbia MUP Data Offe...
EDR Terminator Sale, Alleged Adobe Business Leak, Serbia MUP Data Offer, and Argentina BCRA IOMA GDEBA Claims SOCRadar Dark Web Team identified several new underground posts, including a listing adver...
Inside The Gentlemen Ransomware Leak: When the Hunter Becomes the Hunt...
Inside The Gentlemen Ransomware Leak: When the Hunter Becomes the Hunted Ransomware groups spend their days breaking into networks, stealing data, and pressuring victims into paying. They rarely find ...

CVE-2026-20182: Cisco Catalyst SD-WAN Auth Bypass Added to CISA KEV
CVE-2026-20182: Cisco Catalyst SD-WAN Auth Bypass Added to CISA KEV Cisco has disclosed CVE-2026-20182, a critical authentication bypass affecting Cisco Catalyst SD-WAN Controller (formerly vSmart) an...
CVE-2026-42945: NGINX Rewrite Heap Overflow Enables Remote DoS & Poten...
CVE-2026-42945: NGINX Rewrite Heap Overflow Enables Remote DoS & Potential RCE CVE-2026-42945 is a heap-based buffer overflow in NGINX that occurs in ngx_http_rewrite_module (the rewrite module). ...

Top 5 Surface Web Hacker Forums in 2026
Top 5 Hacker Forums on the Surface Web Security teams often associate cybercrime forums exclusively with the Dark Web and Tor. However, several of the most active underground communities now operate o...

BreachForums & TeamPCP Promote Supply Chain Competition as Cybercrime ...
BreachForums & TeamPCP Promote Supply Chain Competition as Cybercrime Gets Gamified Underground cybercrime communities are increasingly borrowing ideas from legitimate tech ecosystems: branding, p...

SOCRadar’s Free Ransomware Intelligence Dashboard: Track Live Ransomwa...
SOCRadar’s Free Ransomware Intelligence Dashboard: Track Live Ransomware Activity The ransomware threat intelligence community has been doing incredible work making data more accessible from projects ...

Dark Web Profile: Keymous+
Dark Web Profile: Keymous+ Keymous Plus, also known as Keymous+ threat group, markets itself as a hacktivist collective fighting for humanity. What intelligence investigations have documented is struc...
May 2026 Patch Tuesday: 137 Vulnerabilities, No Zero-Days
May 2026 Patch Tuesday: 137 Vulnerabilities, No Zero-Days Microsoft released its May 2026 Patch Tuesday security updates, resolving a total of 137 vulnerabilities across Windows and a broad range of M...

Top 10 Deep & Dark Web Forums in 2026
Top 10 Deep Web and Dark Web Forums in 2026 The top Deep Web and Dark Web Forums actively monitored in 2026 are XSS, Exploit.in, BHF, Dread, DarkForums, Altenen, CryptBB, Cracked, and DamageLib, based...






