
Top 10 Phishing Simulation Tools
Top 10 Phishing Simulation Tools Phishing attacks continue to pose a significant threat, affecting both individuals and organizations. To combat these threats, a variety of phishing simulation tools h...

Global DDoS Attack Landscape: Insights from Q1 2024
Global DDoS Attack Landscape: Insights from Q1 2024 Distributed Denial of Service (DDoS) attacks continue to escalate in frequency and complexity, posing significant threats across various sectors, pa...

Phishing in 2024: 4,151% Increase Since Launch of ChatGPT; AI Mitigati...
Phishing in 2024: 4,151% Increase Since Launch of ChatGPT; AI Mitigation Methods Phishing remains a major threat in cybersecurity, with attacks growing more frequent and sophisticated each year. In 20...

Cyber Threats Targeting the Hajj Season
Cyber Threats Targeting the Hajj Season Hajj is a religious obligation for Muslims, which must be completed at least once in their lifetime by all adults who are physically and financially able to mak...

Exploring the Most Common Passwords in Singapore: Trends, Implications...
Exploring the Most Common Passwords in Singapore: Trends, Implications, and Security Tips Passwords are essential for protecting your online accounts, yet many people still use weak, easy-to-guess pas...

Top 5 Phishing Domain Takedown Service
Top 5 Phishing Domain Takedown Service Phishing attacks continue to pose a significant threat to both individuals and organizations. As cyber criminals continue to improve their strategies for exploit...

Third-Party Vendor Breaches: Causes, Key Statistics, Recent Incidents,...
Third-Party Vendor Breaches: Causes, Key Statistics, Recent Incidents, and Effective Mitigation Strategies In modern business operations, most organizations extend their activities beyond their immedi...

Analysis of UK Password Dictionary: The Ultimate Wordlist
Analysis of UK Password Dictionary: The Ultimate Wordlist Passwords should be strong and unique. They act as the first line of defense in safeguarding our personal and business digital assets. As we e...

Password Dictionary Analysis: Ultimate Wordlist of USA Passwords
Password Dictionary Analysis: Ultimate Wordlist of USA Passwords In the digital age, where our lives are increasingly connected with technology, the importance of securing our online accounts cannot b...

Inevitable Tool in Pentesters’ Arsenal: Password Dictionary Lists
Inevitable Tool in Pentesters’ Arsenal: Password Dictionary Lists Newbie penetration testers often struggle to grasp the significance of the initial findings reported by most Dynamic Application Scann...

DarkGate Malware: Exploring Threats and Countermeasures
DarkGate Malware: Exploring Threats and Countermeasures As we get increasingly digitized, the threat posed by malware has reached unprecedented levels in parallel. From individual users to large corpo...
Using Jupyter Notebook for CTI using PyMISP
Using Jupyter Notebook for CTI using PyMISP In Cyber Threat Intelligence (CTI), Jupyter Notebook and PyMISP are transformative tools. Just as Bash commands empower defenders, these platforms offer dyn...
‘Classified’ Intel on the ‘Public’ Telegram Channel: Pentagon US Leak...
‘Classified’ Intel on the ‘Public’ Telegram Channel: Pentagon US Leak In the rapidly evolving landscape of digital communication, Telegram has emerged as a prominent platform for various user groups f...
QakBot, One of The Most Observed Malware
QakBot, One of The Most Observed Malware [Update] February 16, 2024: “New Qbot Malware Variant Uses Evasion Techniques” [Update] November 22, 2023: See the subheading “Possible Successors of QakBot: D...

Raccoon Stealer Resurfaces with New Enhancements
Raccoon Stealer Resurfaces with New Enhancements The developers behind the information-stealing malware, Raccoon Stealer, have broken their six-month silence on hacker forums. They are now promoting a...
Telegram Channels Unveiled: The Hidden Dangers Lurking in Shared Files
Telegram Channels Unveiled: The Hidden Dangers Lurking in Shared Files In today’s interconnected world, cyberspace has become a breeding ground for legitimate and malicious activities; Telegram, a pop...

Possible Cyber Threats in the 2024 Olympics
Possible Cyber Threats in the 2024 Olympics The design of the Paris 2024 Olympic and Paralympic torch, introduced on July 25, 2023, struck the first gong for The Paris 2024 Summer Olympic and Paralymp...
What is EMOTET Malware and How to Protect Yourself
What is EMOTET Malware and How to Protect Yourself According to Arne Schoenbohm, who leads the German Federal Office of Information Security (BSI), EMOTET is the king of malware. EMOTET actively attac...

The Mindset Behind Phishing Campaigns
The Mindset Behind Phishing Campaigns Phishing attacks are cybercrimes that target individuals, businesses, and organizations. These attacks use deception and manipulation techniques to trick victims ...
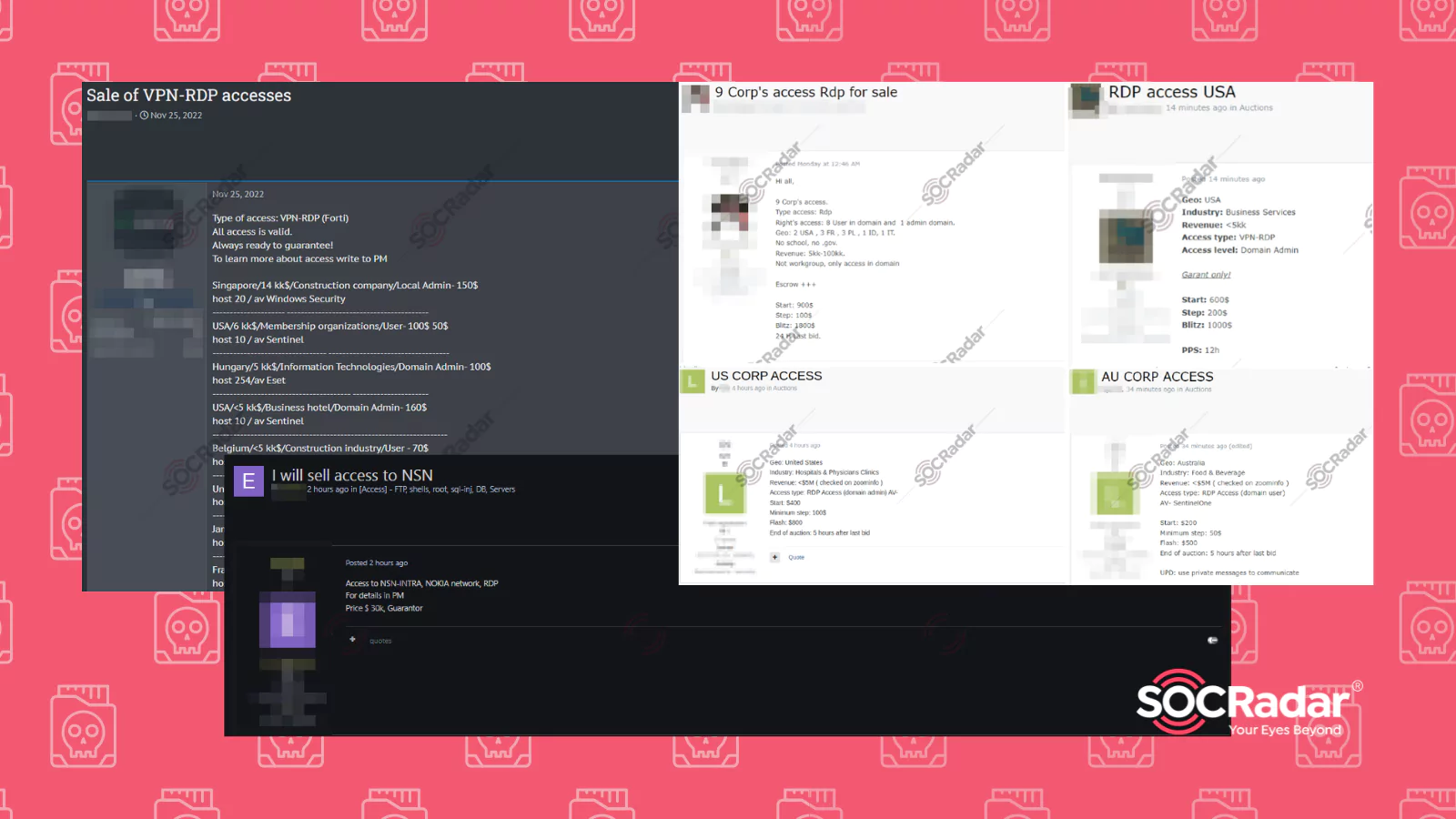
RDP Access Sales on Dark Web Forums Detected by SOCRadar
RDP Access Sales on Dark Web Forums Detected by SOCRadar Remote Desktop Protocol, or RDP, is a protocol developed by Microsoft. It allows the user to control another computer over a network connection...






























