
$162M Stolen from Digital Asset Trader Wintermute
Evgeny Gaevoy, the CEO of Wintermute, said earlier today that the company had been hacked and had lost $162.2 million in DeFi operations.
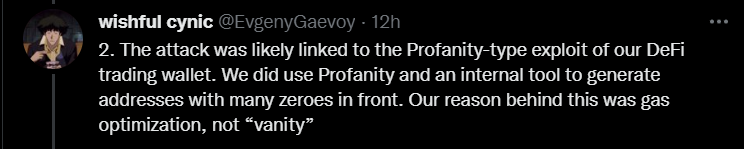
The Profanity tool was used to create the compromised Wintermute wallet.
Wintermute is a digital asset trading firm that provides liquidity to over 50 cryptocurrency exchanges and trading platforms like Binance, Bitfinex, Coinbase, and Kraken.
Because it has twice as much equity as was stolen, the business is still solvent. Though the platform will try to restore its functions, a service interruption can happen in the following days.
Gaevoy has given investors the option to recall loans. He also said that they are open to treating the security incident as a “white hat” event, which means they are willing to pay the hacker a bounty for successfully exploiting the vulnerability without incurring legal consequences. It is unclear if the hacker is ready to return the money.
Gaevoy shared more details about the incident on his Twitter account.
Digital assets valued at over $47,7 million are currently in the hacker’s wallet. The remaining funds have been transferred to Curve Finance’s “3CRV” liquidity pool, where distinguishing and freezing the tokens will be difficult.
Due to the recent Ethereum merge, powerful mining farms have experienced performance loss; some of these farms could possibly look to make a profit from the vulnerability.
Threat Actors Exploited Profanity to Carry Out the Hack
Experts of crypto believe that the hacker exploited a flaw in Profanity.
Profanity is an Ethereum vanity address generator that enables users to generate addresses that contain a predefined string of numbers and letters.
How Profanity works is as follows:
- Choose one of the 4 billion seed private keys at random.
- Deterministically increase it to 2 million private keys.
- From these private keys, generate the public keys.
- Increase them again until they reach the desired vanity address.
The Profanity project was abandoned by its creator because it had security flaws that allowed it to crack private keys. In fact, the keys were vulnerable to brute-force attacks.
It was found that, before analysts had even revealed the vulnerability, hackers had already exploited it to steal $3.3 million in another incident. Everyone with a wallet created using Profanity was advised to move their assets.
Profanity’s creator entirely archived it to stop anyone from using it and lessen the impact of recent incidents.
A proof-of-concept is available for the Profanity exploit.



































