UNC5221 Targets Critical Ivanti Flaw (CVE-2025-22457) with TRAILBLAZE & BRUSHFIRE Malware
A recently disclosed critical vulnerability in Ivanti products, CVE-2025-22457, has drawn urgent attention across the cybersecurity community. The flaw, confirmed to be actively exploited in the wild, impacts widely used enterprise solutions including Ivanti Connect Secure (ICS) VPN appliances, Pulse Connect Secure, Ivanti Policy Secure, and ZTA gateways. If left unpatched, it could allow remote attackers to execute arbitrary code and gain full control of affected systems.
In parallel, another severe vulnerability was revealed in the Apache Parquet Java library, highlighting how attackers are increasingly eyeing foundational components in modern data pipelines.
Let’s break down these threats, examine the tactics used by advanced threat actors, and go over what security teams should do next.
CVE-2025-22457: Critical Buffer Overflow Threat in Ivanti Products
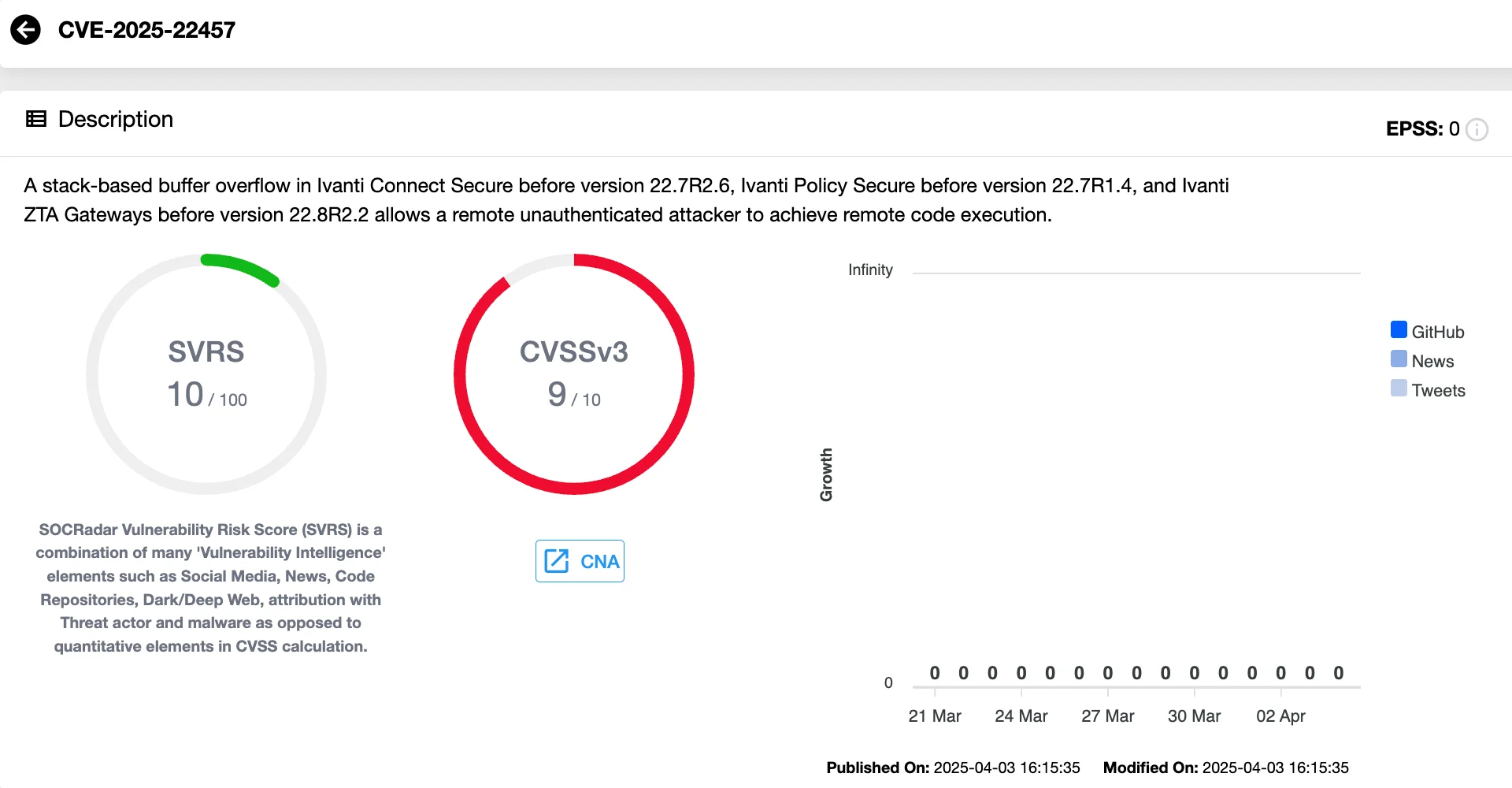
The latest Ivanti vulnerability, CVE-2025-22457, carries a CVSS score of 9.0, classifying it as critical. At its core, the flaw stems from a stack-based buffer overflow and can be remotely triggered without authentication. If exploited, it allows attackers to execute arbitrary code, potentially leading to full system compromise.
Real-world exploitation has already been observed. Ivanti confirmed that a limited number of customers using Connect Secure and End-of-Support Pulse Connect Secure appliances have been compromised. So far, there’s no evidence of active attacks against Policy Secure or ZTA gateways.
Affected Products and Patch Availability
According to Ivanti’s advisory, the vulnerability affects several products. Here’s a breakdown of the impacted versions and corresponding fixes:
Ivanti Connect Secure
- Affected: Versions 22.7R2.5 and earlier
- Fix: Version 22.7R2.6 (released February 11, 2025)
Ivanti Policy Secure
- Affected: Versions 22.7R1.3 and earlier
- Fix: Version 22.7R1.4 (expected April 21, 2025)
ZTA Gateways
- Affected: Versions 22.8R2 and earlier
- Fix: Version 22.8R2.2 (expected April 19, 2025)
Pulse Connect Secure (End-of-Support)
- Affected: Versions 9.1R18.9 and earlier
- Fix: Version 22.7R2.6
- Note: This product reached End-of-Support as of December 31, 2024. Customers are urged to contact Ivanti and migrate.
Organizations using any of these versions should prioritize patching or migration as soon as possible to mitigate exposure.
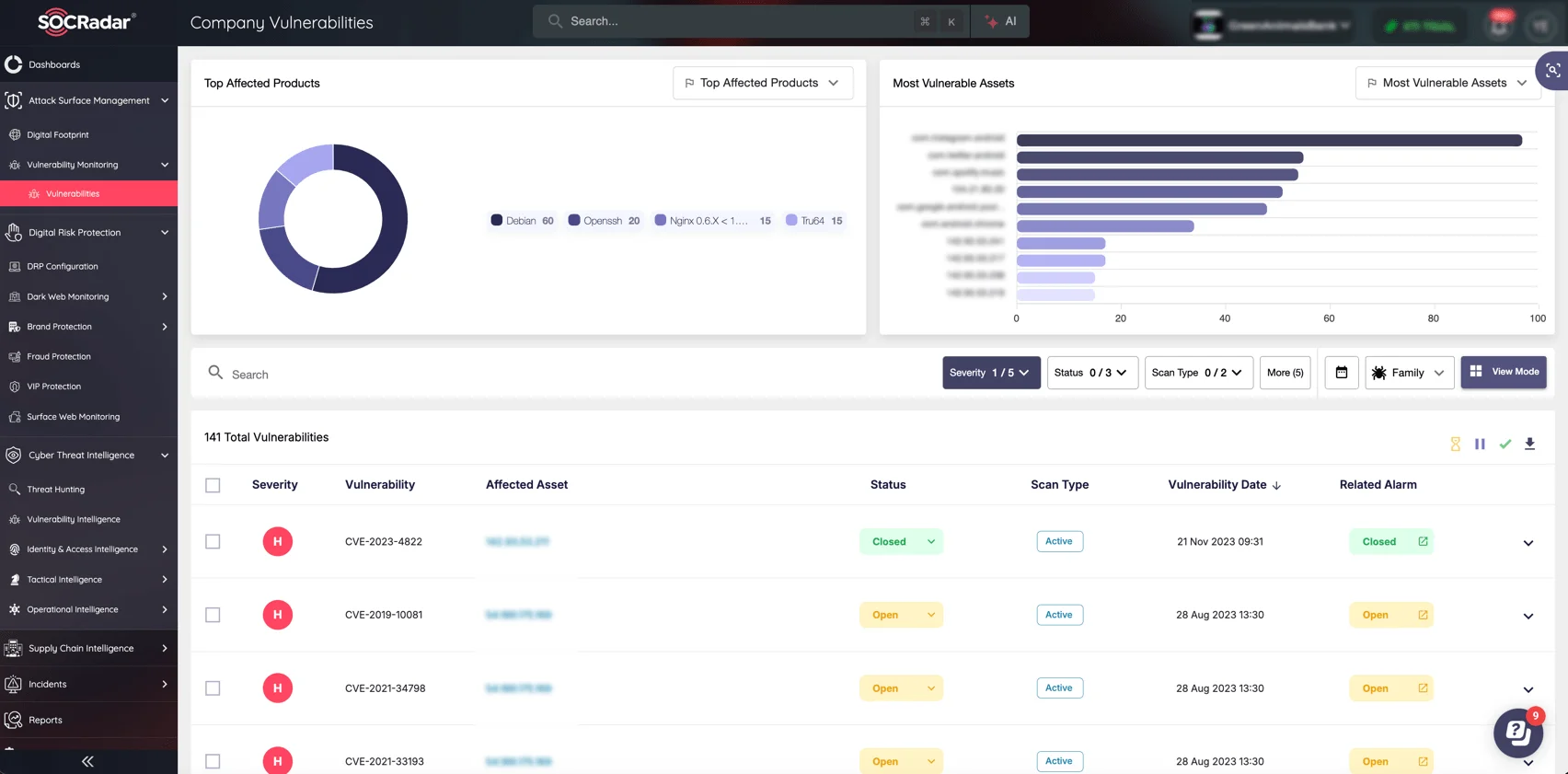
Vulnerabilities like CVE-2025-22457 show how attackers target widely exposed enterprise systems. SOCRadar’s Attack Surface Management (ASM) continuously identifies and monitors all your externally exposed digital assets, highlighting hidden risks like outdated software or misconfigured servers.
With automated discovery and visibility into your entire digital footprint, your organization can promptly patch vulnerabilities, enforce better security practices, and close entry points that cybercriminals exploit most frequently.
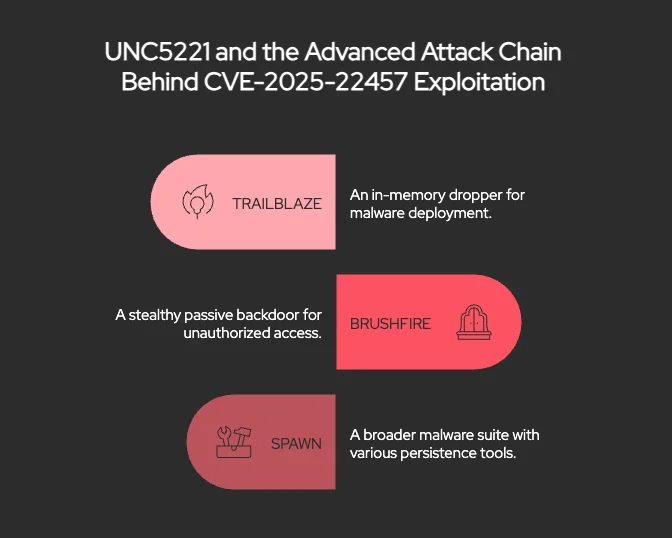
UNC5221 and the Advanced Attack Chain Behind CVE-2025-22457 Exploitation
Threat intelligence from Mandiant confirms that the exploitation of CVE-2025-22457 began as early as mid-March 2025. Attackers deployed a multi-stage malware arsenal that includes:
- TRAILBLAZE: an in-memory dropper
- BRUSHFIRE: a stealthy passive backdoor
- SPAWN: a broader malware suite that includes multiple components for persistence and evasion
The attack sequence is particularly sophisticated. According to the report, it starts with exploiting the buffer overflow to run a shell script that scans for vulnerable web processes. From there, the TRAILBLAZE dropper is injected into memory, which then delivers BRUSHFIRE into an active web service. The malware uses SSL hooks to covertly execute encrypted shellcode, while additional modules like SPAWNSLOTH, SPAWNSNARE, and SPAWNWAVE help evade detection by tampering with logs and obscuring system artifacts.
This activity has been attributed to UNC5221, a China-linked espionage group with a known history of targeting edge devices. They’ve also been associated, at least loosely, with groups like APT27, UTA0178, and Microsoft’s Silk Typhoon, although Mandiant stops short of confirming these connections.
In this case, UNC5221 is believed to have reverse-engineered Ivanti’s February patch to create an exploit for unpatched systems, marking the first time they’ve been observed moving from zero-day to n-day exploitation in this product line.
To further mask their operations, UNC5221 leveraged a global obfuscation network of compromised appliances, including Cyberoam firewalls, QNAP NAS devices, and ASUS routers. This infrastructure helps anonymize their traffic during attacks, making attribution and detection even more challenging.
Mitigation Guidance: What Ivanti Customers Should Do Now
Ivanti has issued urgent guidance for customers to address the risks posed by CVE-2025-22457. For those using Connect Secure, the company recommends immediately upgrading to version 22.7R2.6. If Indicators of Compromise and ICT results suggest a breach, Ivanti advises performing a factory reset before redeploying the appliance with the latest patch.
Notably, version 22.7R2.6 also resolves several other critical vulnerabilities:
- CVE-2024-38657
- CVE-2025-22467
- CVE-2024-10644
These bugs could allow a remote, authenticated attacker to write arbitrary files or execute code, amplifying the urgency to patch.
For full technical details and official updates, refer to Ivanti’s April Security Advisory.
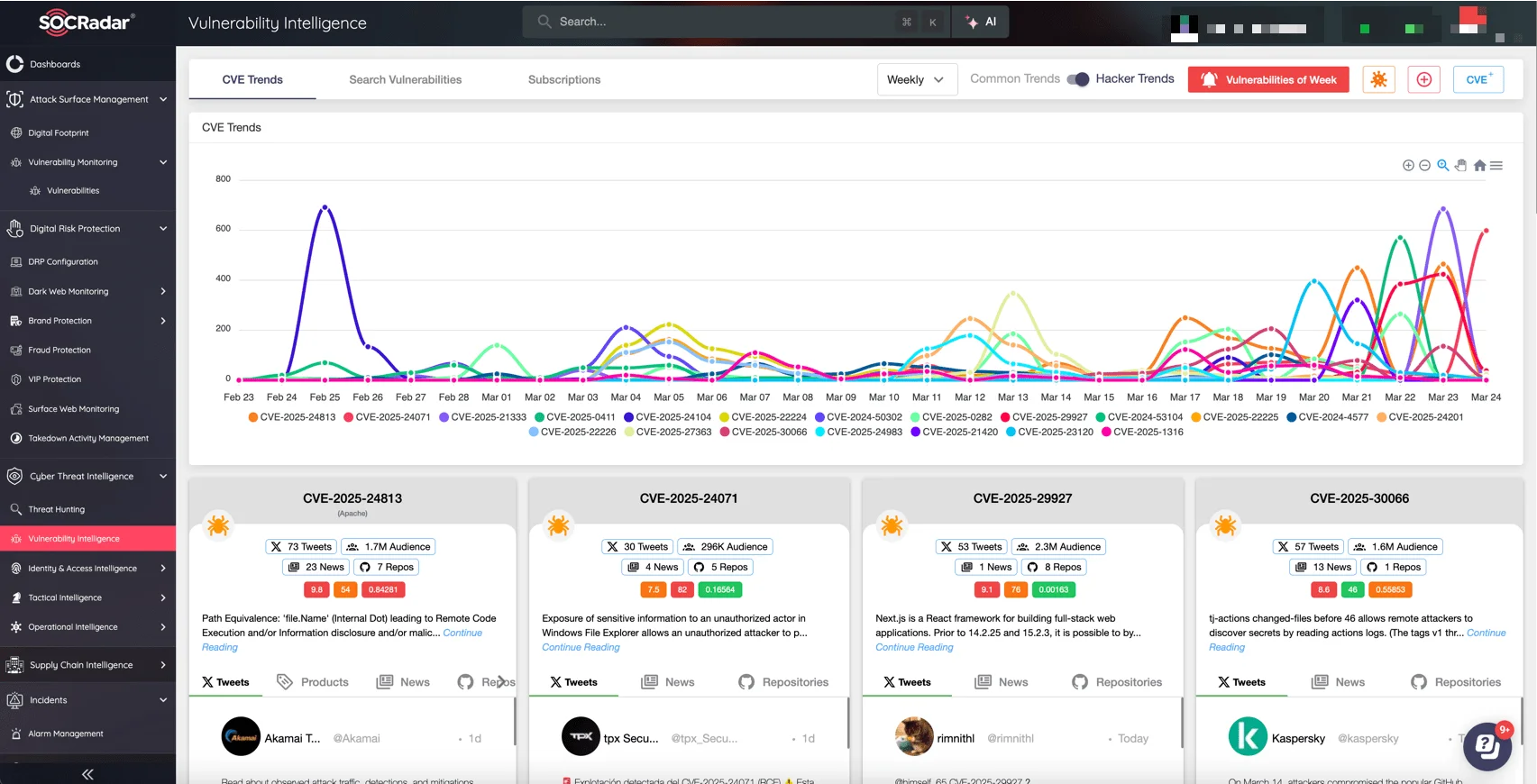
Enhance your security team’s ability to tackle high-risk threats like CVE-2025-22457 with SOCRadar’s Vulnerability Intelligence, part of the comprehensive Cyber Threat Intelligence module. Quickly identify critical vulnerabilities affecting your assets, get actionable insights on active exploitation, and prioritize fixes based on actual threat scenarios, not just CVSS scores.
SOCRadar’s real-time vulnerability tracking and alerts help your team rapidly move from detection to mitigation, preventing breaches before attackers can exploit them.
Indicators of Compromise (IOCs) Related to CVE-2025-22457 Exploitation & YARA Rules
Below are Indicators of Compromise (IOCs) associated with the exploitation of CVE-2025-22457, as well as YARA rules for detection, as provided on the Google Cloud blog.
Indicators of Compromise (IOCs):
| Code Family | MD5 | Filename | Description |
| TRAILBLAZE | 4628a501088c31f53b5c9ddf6788e835 | /tmp/.i | In-memory dropper |
| BRUSHFIRE | e5192258c27e712c7acf80303e68980b | /tmp/.r | Passive backdoor |
| SPAWNSNARE | 6e01ef1367ea81994578526b3bd331d6 | /bin/dsmain | Kernel extractor & encryptor |
| SPAWNWAVE | ce2b6a554ae46b5eb7d79ca5e7f440da | /lib/libdsupgrade.so | Implant utility |
| SPAWNSLOTH | 10659b392e7f5b30b375b94cae4fdca0 | /tmp/.liblogblock.so | Log tampering utility |
YARA Rules:
rule M_APT_Installer_SPAWNANT_1
{
meta:
author = “Mandiant”
description = “Detects SPAWNANT. SPAWNANT is an
Installer targeting Ivanti devices. Its purpose is to persistently
install other malware from the SPAWN family (SPAWNSNAIL,
SPAWNMOLE) as well as drop additional webshells on the box.”
strings:
$s1 = “dspkginstall” ascii fullword
$s2 = “vsnprintf” ascii fullword
$s3 = “bom_files” ascii fullword
$s4 = “do-install” ascii
$s5 = “ld.so.preload” ascii
$s6 = “LD_PRELOAD” ascii
$s7 = “scanner.py” ascii
condition:
uint32(0) == 0x464c457f and 5 of ($s*)
}
rule M_Utility_SPAWNSNARE_1 {
meta:
author = “Mandiant”
description = “SPAWNSNARE is a utility written in C that targets
Linux systems by extracting the uncompressed Linux kernel image
into a file and encrypting it with AES.”
strings:
$s1 = “x00extract_vmlinuxx00”
$s2 = “x00encrypt_filex00”
$s3 = “x00decrypt_filex00”
$s4 = “x00lbb_mainx00”
$s5 = “x00busyboxx00”
$s6 = “x00/etc/busybox.confx00”
condition:
uint32(0) == 0x464c457f
and all of them
}
rule M_APT_Utility_SPAWNSLOTH_2
{
meta:
author = “Mandiant”
description = “Hunting rule to identify strings found in SPAWNSLOTH”
strings:
$dslog = “dslogserver” ascii fullword
$hook1 = “g_do_syslog_servers_exist” ascii fullword
$hook2 = “ZN5DSLog4File3addEPKci” ascii fullword
$hook3 = “funchook” ascii fullword
condition:
uint32(0) == 0x464c457f and all of them
}
Apache Parquet Hit by Severe RCE Vulnerability
Beyond Ivanti, another serious threat has emerged in the broader vulnerability landscape. A critical flaw in the Apache Parquet Java library, tracked as CVE-2025-30065, has been disclosed, carrying a maximum CVSSv4 score of 10.0. This vulnerability opens the door for Remote Code Execution (RCE) if a system reads a specially crafted Parquet file.
Apache Parquet is widely used in data engineering pipelines and analytics platforms, offering high-performance compression and schema-rich support for complex data. However, versions up to and including 1.15.0 contain a bug in the parquet-avro module that mishandles schema parsing.
According to researchers, attackers could exploit this issue by tricking a vulnerable system into importing a malicious Parquet file, particularly dangerous in environments that routinely ingest external or unverified data.
The flaw has been patched in version 1.15.1, and while no active exploitation has been reported, its potential impact on large-scale data processing systems makes prompt patching essential.
For a full technical breakdown and mitigation guidance, refer to this advisory on CVE-2025-30065.