
All You Need To Know About the ManageEngine Vulnerability (CVE-2022-40300)
What is the Vulnerability in ManageEngine (CVE-2022-40300)?
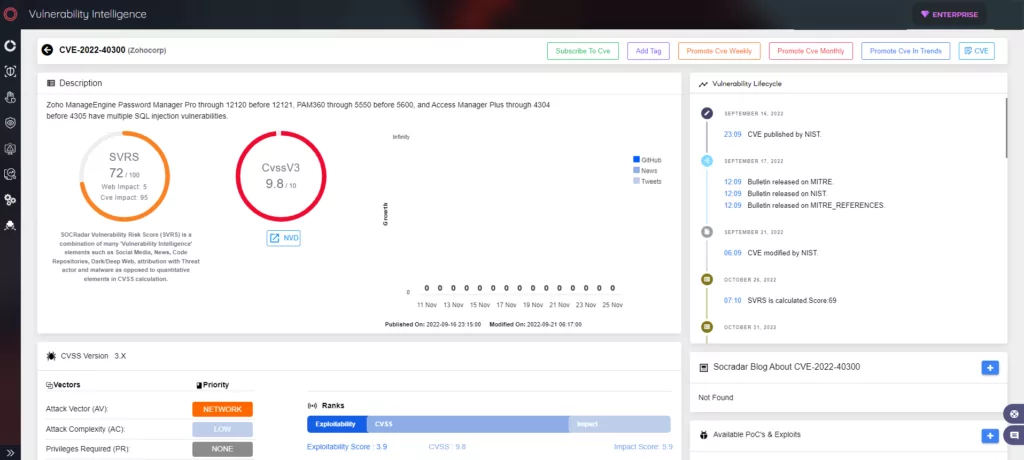
Recently, Zoho has patched a vulnerability tracked as CVE-2022-40300 in ManageEngine. The vulnerability affects a few products and could lead to SQL injection due to resource types being validated improperly in AutoLogonHelperUtil class.
How Critical is the CVE-2022-40300 Vulnerability?
The vulnerability in ManageEngine is of critical severity, with a CVSS score of 9.8.
Which Versions are Vulnerable?
|
Products |
Versions |
|
Password Manager Pro |
From 12120 before 12121 |
|
PAM360 |
From 5550 before 5600 |
|
Access Manager Plus |
From 4304 before 4305 |
How Does the CVE-2022-40300 Vulnerability Work?
A remote attacker has to send a crafted HTTPS request to their targeted server’s default port to exploit the CVE-2022-40300 vulnerability.
If the request is successful, the attacker will get access to the product’s web interface and will be able to run arbitrary SQL codes with System privileges in the database service’s security context.
A user with System privileges can add or edit a resource type in the products’ web interface, which will be submitted as an HTTP multipart or form-data request to the AddResourceType.ve endpoint.
Is There Any Exploit Code for the Vulnerability?
A malicious HTTP request example that could exploit the CVE-2022-40300 vulnerability and details are available on Zero Day Initiative’s blog.
Is There Any Mitigation or Patch Available?
ManageEngine has not provided any workarounds. It is advised to apply the patches to fix the issues. The fixes are available on ManageEngine’s advisory.
How to Detect any Malicious Activity Related to This Vulnerability?
To determine whether CVE-2022-40300 has been exploited on your server, a detection device has to monitor the traffic on the vulnerable ports, as well as inspect HTTP POST requests to a Request-URI that contains the /AddResourceType.ve string.
You can find additional information about detection on Zero Day Initiative’s blog.




































