
An Overview of Optiv CTI Estimate 2020: Attack Tools, Techniques and Procedures
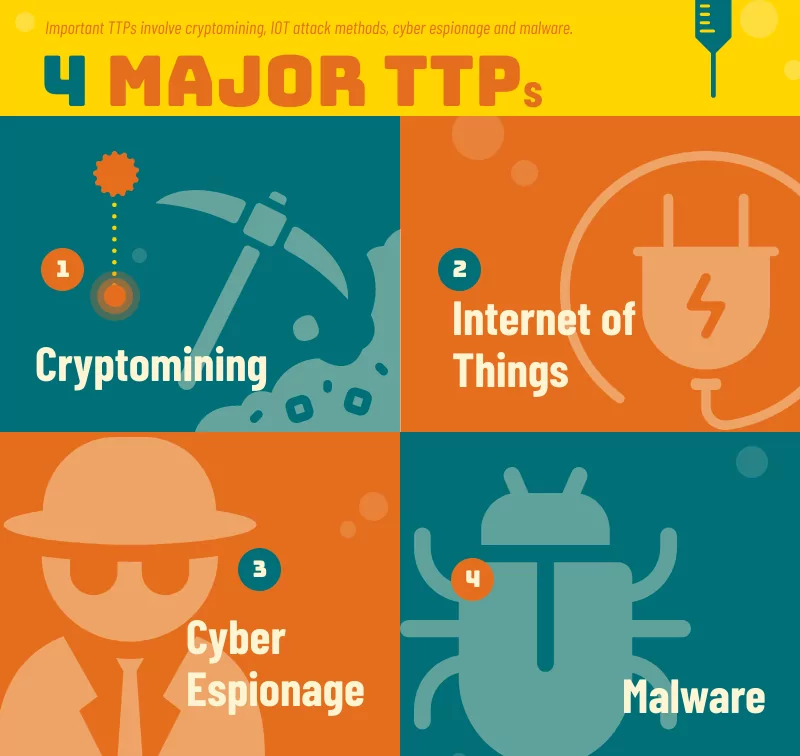
The term Tools, Techniques and Procedures (TTPs) refers to a method used to evaluate the cyber activity or to identify a certain actor of threat. According to Optiv’s 2020 Cyber Threat Intelligence Estimate Report, relevant TTPs include cryptomining, IoT, cyberspying and malware attacking methods.
Cryptomining
In order to address complex mathematical problems and check Internet transactions, the cryptocurrency mining (cryptomining) uses computer-processing power and the miners are compensated with a small sum.
Public mining pools are co-operating miners’ communities that agree to share block rewards according to their contribution to mining hash power.
Nearly 9 percent of the cloud organizations showed signs of relation and probable success across public mining pools of the Monero (XMR) sector as stated by Palo Alto. It is emphasized in the report that near to 60% of all public XMR mining network connections to XMR pools are in the USA. Most of the time, such transactions take place on ports like 80 and 443 that are supposed to ignore company firewall rules. The report mentions some frequently used cloud crypto miner tools such as;
- Rocke: The tool has developed cyber operations beyond cryptomining with another tool named Godlua that performs scripting and shell operations inside the cloud infrastructure through proxy Lua (a programming language mainly used in embedded applications).
- 8220 Mining Group: The factual signs of 8220 network operations are focused on port 8220. Although the port 8220 is an unusual one, it may be used for custom purposes for default-networked environments. Palo Alto finds that 21 percent of cloud organizations have networking connections which appear to have 8220 signatures, based on established 8220 indicators of compromise (IOCs).
- Pacha: 93% of cryptocurrency Pacha traffic was bound for China, although it is unclear what kinds of network operations are conducted.
Internet of things
Palo Alto researchers reported that 98% of IoT traffic was unencrypted revealing personal and sensitive details on their networks and that 57% were prone to medium to high intensity assaults, although the amount of IoT devices exposed was estimates at 4.8 billion devices up from 22.5% at the end of 2018. The vulnerable levels of low patches and the aging operational technology (OT) Protocols are a product of IoT. The report list top IoT attack methods as follow;
- Exploits target device vulnerabilities
- Password attacks
- Unclosed backdoors
- Unsegmented networks
- Botnet attacks
The report also made the following recommendations against such IoT attacks;
- Develop an IoT security strategy
- Discover IoT devices
- Patch printers
- Segment IoT devices across VLANs
- Implement active around the-clock monitoring
- Use a vulnerability management process
Cyber espionage
Cyber spying or cyber espionage is the act or activity of extracting information and secrets from entities, adversaries and rivals without the authorization and consent of information holder. Some commonly leveraged public tools include;
- PsExec: It enables system administrators to remotely access and manage their systems over the Server Message Block (SMB) protocol, TCP port 445.
- Mimikatz: Its functionality encompasses password dumping from memory, PINs, hashes and Kerberos tickets.
- X-agent: It is also called CHOPSTICK. Its functionality focuses on information gathering and includes capabilities such as logging keystrokes, transmitting remote files, taking screenshots and modifying registries.
- Empire: An open-source post-exploitation framework.
- Netstat: This operating system utility is used to display TCP connections, network connections and listening ports common within Windows, Linux and UNIX.
- Cobalt Strike: A commercially available penetration-testing tool.
The report offers some suggestions for cyber espionage:
- Enforce a security policy
- Ensure operating systems, software and firmware are patched to the latest updates
- Implement multi-factor authentication
Malware: Kryptik, Obfuse and Emotet
The Kryptik trojan has been built to get details about FTP servers on an infected host. It scans the .ini or.dat file paths list of Windows.
Obfuse is a virus that has been developed to capture sensitive information stored on a device supplied via porn pages, online gaming, file sharing between peers, false advertisements, free software from third parties and spam attachments.
Emotet is a malware application that was originally developed to capture bank data. However, it has developed into a significant consumer hazard.
On the report of recommendations against such malware;
- Install next-generation antivirus coupled with endpoint detection
- Implement techniques within Microsoft environment
Malware: Ransomware
Ransomware is a form of malware that continuously blocks access to a victim’s data without paying any ransom. While certain common ransomware may lock up the device to a lesser degree, advanced malware uses a strategy, in which it encrypts the victims’ data, renders them unavailable, and allows a ransom to decrypt them. Attackers may do it by deactivating individual highly essential resources for an organization, such as MSExchangeIS, that will inaccessible Microsoft Exchange information. Hackers sometimes can stop services for data destruction or encrypt data for impact on services such as Swap and Microsoft SQL Server data stores. Recommendations based on the report;
- Consider implementing IT recovery plans
- Research trusted sources
- Identify potentially malicious software
Discover SOCRadar® Community Edition for free
With SOCRadar® Community Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.


































