APT5 Exploits Zero-Day Vulnerability on Citrix ADC and Gateway Devices
Citrix has just released a patch to address a critical zero-day vulnerability affecting its products. The vulnerability is identified as CVE-2022-27518 (CVSS score: 9.8) and allows remote code execution for unauthenticated attackers.
VP of Citrix, Peter Lefkowitz, stated on a blog that Citrix is aware of several targeted attacks in the wild using CVE-2022-27518.
The National Security Agency (NSA) has also addressed the issue with guidance to detect the malicious activity of threat actors that might exploit CVE-2022-27518. The vulnerability exploitation is already attributed to a threat group named APT5, also known as UNC2630 and Manganese.
The threat group has targeted several organizations affected by CVE-2022-27518, but Citrix and the NSA have not provided any additional information. It needs to be clarified how many organizations were affected.
About the Threat Actor: APT5
The Chinese threat actor group APT5 has been observed to target industries in the U.S., Europe, and Asia, but its primary focus is on telecommunications and high-tech firms. APT5 appears to be made up of numerous subgroups and has been active since at least 2007.
The group employs a lot of malware with keylogging capabilities to monitor corporate executives, gather valuable information, and breach their networks.
The group also targeted Fortinet and Pulse Secure around 2019 to exploit their VPN servers and access files without authentication, which could allow them to take over devices.
Affected Citrix Products
CVE-2022-27518 affects Citrix ADC and Gateway versions 12.1 and 13.0 before 13.0-58.32.
In addition to using a vulnerable version, the devices must be configured as SAML SP or SAML IdP for an exploit to succeed.
Check the ns.conf file for the following commands to find out your currently set configuration:
- add authentication samlaction –> the device is configured as SAML SP
- add authentication samlIdpProfile –> the device is configured as SAML IdP
Is There a Mitigation Available?
Customers are advised to immediately patch the vulnerability because, according to Citrix’s blog, there is no option other than disabling SAML authentication.
Find fixed versions and more information on Citrix’s blog.
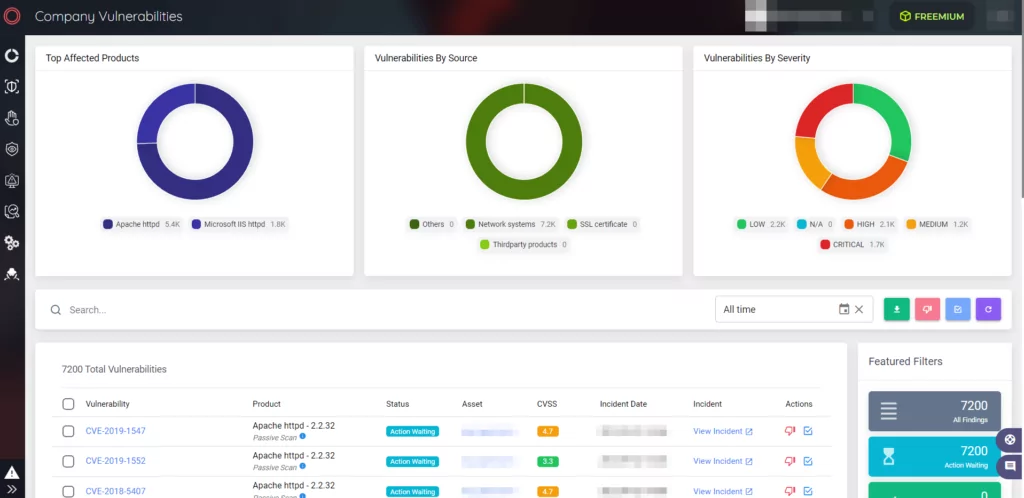
Get Notified When a Vulnerability Affects Your Organization
To ensure your safety, SOCRadar will monitor your digital assets and notify you when there is a threat to your organization. Receive immediate alerts on zero-day vulnerabilities like CVE-2022-27518 with Vulnerability Detection.
You can read our blog about three critical vulnerabilities Citrix patched on November 2022.




































