
CL0P’s Shell Attack, Stolen Reddit Data, and New Edge Stealer
Brace yourself for this week’s thrilling snapshot of the dark web, where secrets are the common currency, and anonymity reigns. We’re delving deep into the cyber shadows, where tales of a cunning ‘Shell Attack’ by notorious group CL0P stir the waters.
But that’s not all. Get ready to discover the unsettling reality of a massive Reddit data heist and ponder over the riddles of the ‘New Edge Stealer.’ This week, we pull back the veil on the hidden web where danger lurks, and innovation thrives in the most unexpected ways.
Are you curious yet? Keep reading because the dark web never sleeps.
<
Find out if your data has been exposed.
The New Ransomware Victim of Cl0p: Shell Global

On June 14, a SOCRadar dark web researcher detected that the Cl0p ransomware group had allegedly targeted Shell Global, a prominent British oil and gas multinational. According to the researcher’s findings, the Cl0p group listed Shell Global on their extortion site, indicating a potential breach of the company’s systems. This incident marks the second time that Shell has been targeted by the Cl0p ransomware, with the initial attack occurring in 2021 when the group exploited vulnerabilities in Accellion’s file transfer appliance. The motive behind these attacks appears to be extortion, with the hackers threatening to release sensitive information unless a ransom is paid. As Shell Global confirms the breach, it highlights the ongoing challenges that organizations face in protecting their digital infrastructure from sophisticated cyber threats.
The Reddit Files
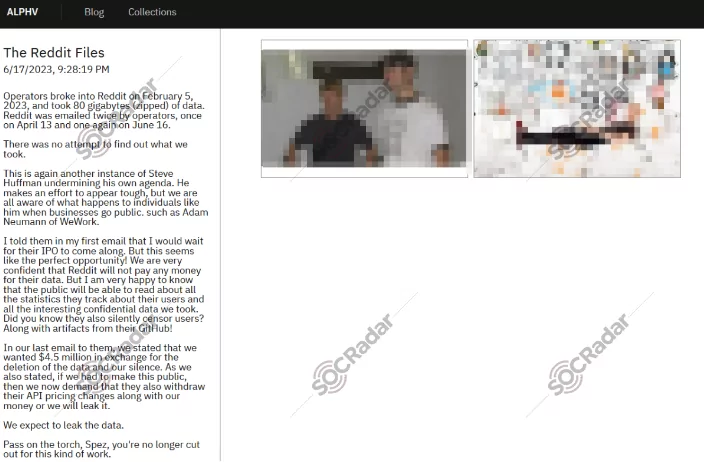
A SOCRadar dark web analyst has detected that Reddit is listed as a victim on the website of the BlackCat/ALPHV ransomware group. The notorious cybercriminal group has claimed responsibility for the February cyberattack on Reddit, in which they allegedly stole 80GB of data from the company. Reddit had previously disclosed that the breach occurred due to a phishing attack targeting one of their employees. Although Reddit stated that their primary production systems were not breached, the threat actors behind the attack now threaten to leak the stolen data unless a ransom of $4.5 million is paid.
Database of Azerbaijan Citizens is on Sale
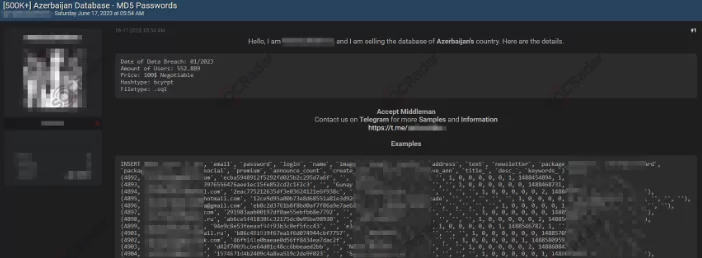
SOCRadar dark web team has detected a new alleged sale of a database containing information on Azerbaijan citizens. The threat actor claims to have access to this database and is advertising it for sale. The details provided include the date of the data breach, which is stated as January 2023, the number of users affected, which is approximately 552,889, and the price of the database listed at $100, with room for negotiation. The hash type mentioned is “bcyrpt,” indicating the type of hashing used for the passwords in the database. The filetype is mentioned as “SQL,” suggesting that the data is stored in a structured query language format. The seller also mentions accepting a middleman for the transaction. For further samples and information, the seller directs interested parties to contact them on Telegram using the provided link.
Edge Stealer is on Sale
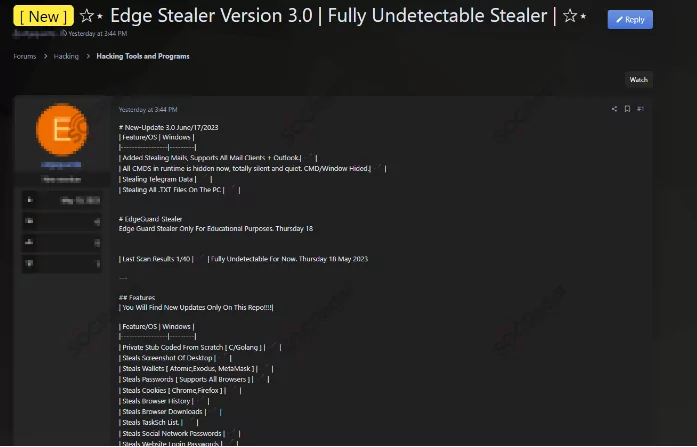
SOCRadar dark web team has discovered the alleged sale of a new version of the “Edge Stealer” called version 3.0. The threat actor behind it claims that the updated stealer includes features like stealing emails from various email clients, capturing Telegram data, and gathering .TXT files from the victim’s computer. It also boasts the ability to hide all command prompt windows during runtime, making it harder to detect. The seller promotes the stealer as undetectable and lists a range of other functionalities, including stealing passwords, cookies, browser history, wallets, and more.
Accounts of Service of the Republic of Poland are on Sale
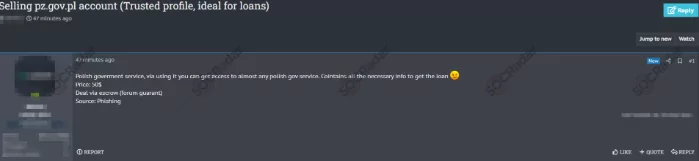
SOCRadar researchers have identified a new alleged sale of accounts related to the Service of the Republic of Poland. The threat actor claims that these accounts provide access to various Polish government services and include all the necessary information to obtain loans. The price listed for these accounts is relatively low, at $50. However, given the nature of the sale and the suspiciously low price, there is reason to question the authenticity and legitimacy of the content being offered.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.



































