Clop Serial Attacks, TP-Link Exploit & macOS Stealer
Powered by DarkMirror™
Last week, the dark web’s most spectacular news was the victims that Clop announced one after the other. The threat actor, who targeted brands such as Rubrik and Hitachi with his attacks by exploiting the vulnerability of GoAnywhere, added the City of Toronto and Virgin Group to its list.
As we saw in the Clop case, vulnerabilities are often used as initial access vectors. Therefore, sharing the exploit code of a vulnerability in a TP-Link product is also noteworthy.
Find out if your data has been exposed.
The New Ransomware Victim of Clop: City of Toronto
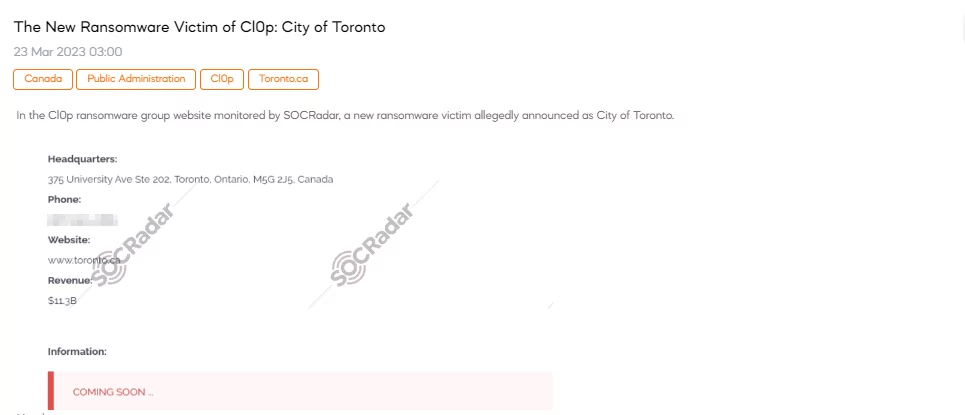
SOCRadar detected a new post revealing that the Clop ransomware gang has recently added the City of Toronto to its growing list of victims. The attack targeted the city government by exploiting a vulnerability in the GoAnywhere secure file transfer tool, which the group has been using to target and compromise more than 100 organizations. This news comes as Clop has announced that it has broken LockBit’s unofficial record for the number of victim posts per day.
CVE-2023-28760 Exploit is Shared for TP-Link
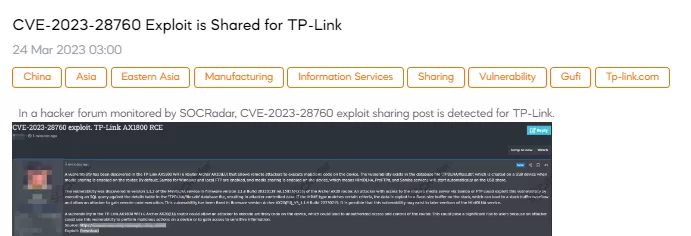
On March 24, SOCRadar detected a post that shared information about exploits in the TP-Link AX1800 WiFi 6 Router Archer AX20 (EU). The post reported a critical remote code execution (RCE) vulnerability, with the CVE identifier CVE-2023-28760, that can allow attackers to execute arbitrary code on the device, potentially leading to unauthorized access and control of the router.
The New Ransomware Victim of Clop: Virgin
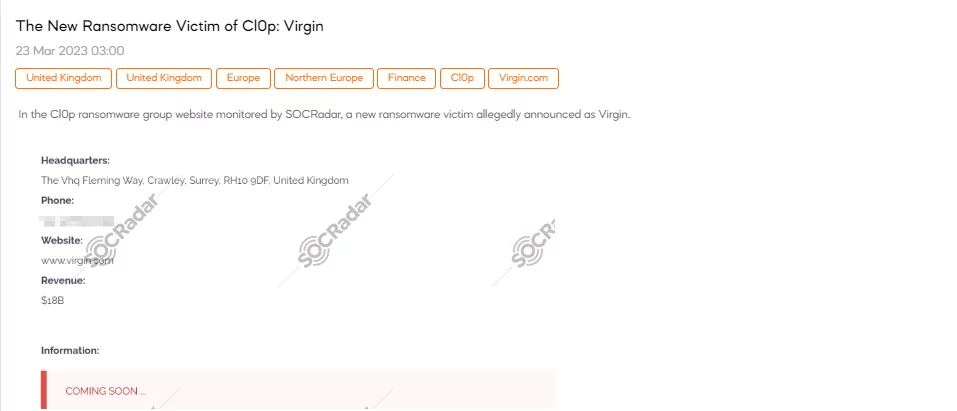
SOCRadar detected a new post revealing that the Clop ransomware gang has recently added Virgin to its list of victims, according to a new post. Virgin reported that the hackers illegally obtained some of their files through a cyber attack on their vendor GoAnywhere.
New macOS Stealer is on Sale
A new macOS stealer with alarming capabilities has been detected by the SOCRadar team. It can extract sensitive information such as passwords, credit card data, and keychain databases from various browsers, including Google Chrome, Firefox, Brave, and Edge. It can also extract files in different formats, including images, documents, and data from cryptocurrency wallets. It has many additional features. The threat actor has announced that it will develop the malware with more features. The price for the stealer is $500.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.