Critical Remote Code Execution Vulnerability in Adobe ColdFusion (CVE-2023-29300)
[Update] January 9, 2024: “CVE-2023-38203 and CVE-2023-29300 in Adobe ColdFusion Have Joined the CISA KEV Catalog”
[Update] September 4, 2023: Fortinet has reported on active exploitation attempts in Adobe ColdFusion. See the subheading: “Ongoing Exploitation Attempts Targeting Adobe ColdFusion Vulnerabilities.”
[Update] July 21, 2023: Added the subheading: “CISA Adds Adobe ColdFusion Vulnerabilities to KEV Catalog (CVE-2023-29298, CVE-2023-38205).”
[Update] July 20, 2023: Added the subheading: “Adobe Emergency Update for Zero-Day Patch Bypass Vulnerability (CVE-2023-38205).”
Adobe ColdFusion, a popular server-side scripting language, is currently facing a critical vulnerability that allows remote attackers to execute arbitrary code. The vulnerability, tracked as CVE-2023-29300, affects multiple versions of ColdFusion, including 2018, 2021, and 2023. Immediate action is recommended to patch the flaw and protect systems from potential exploitation.
Your System at Risk: Unauthorized Attackers One Step Away from Compromise
CVE-2023-29300 is a pre-authentication remote code execution vulnerability in Adobe ColdFusion. It holds a severity rating of 9.8, indicating its critical impact. Attackers can leverage this flaw to execute commands on vulnerable ColdFusion servers, even without authentication, making it a high-risk vulnerability.
The vulnerability was discovered by CrowdStrike researcher Nicolas Zilio and was disclosed by Adobe on July 11th. Although initially not observed in real-world attacks, recent reports indicate that CVE-2023-29300 has been actively exploited in limited attacks.
Exploiting this vulnerability requires the presence of a valid CFC (ColdFusion Component) endpoint. However, researchers have found that it can be combined with CVE-2023-29298 to bypass ColdFusion lockdown mode, allowing remote code execution even on locked-down instances.
Adobe has promptly released security updates for ColdFusion versions 2018, 2021, and 2023 to address these critical vulnerabilities. Admins are strongly advised to upgrade their ColdFusion installations to the latest available version to mitigate the risks associated with CVE-2023-29300.
To further enhance security, Adobe recommends implementing lockdown measures and reviewing their respective Lockdown guides for ColdFusion 2018, 2021, and 2023. Additionally, updating the ColdFusion JDK/JRE to the latest LTS releases for JDK 17 is also recommended.
Adobe Emergency Update for Zero-Day Patch Bypass Vulnerability (CVE-2023-38205)
Adobe has issued an emergency ColdFusion security update to address critical vulnerabilities, including a fix for a new zero-day exploit used in recent attacks. The out-of-band update includes three vulnerabilities, which are as follows:
- A remote code execution (RCE) vulnerability known as CVE-2023-38204 with a CVSS score of 9.8 (Critical).
- Two Improper Access Control vulnerabilities: CVE-2023-38205 with a CVSS score of 7.8 (High) and CVE-2023-38206 with a CVSS score of 5.3 (Medium).
Of these vulnerabilities, CVE-2023-38204 is the most severe but there are no reports of exploitation activity related to it.
However, according to Adobe, CVE-2023-38205 has been exploited in limited attacks. Notably, CVE-2023-38205 is a patch bypass for the fix of the ColdFusion authentication bypass vulnerability (CVE-2023-29298).
On July 13, researchers from Rapid7 discovered that attackers were chaining exploits for CVE-2023-29298, CVE-2023-29300, and CVE-2023-38203 to take advantage of vulnerable ColdFusion servers, allowing them to install web shells and gain remote access to devices. Researchers reported their findings to Adobe, leading to the emergency update.
It is advised to apply the emergency update timely, as the vulnerability is already under exploitation.
CISA Adds Adobe ColdFusion Vulnerabilities to KEV Catalog (CVE-2023-29298, CVE-2023-38205)
Cybersecurity and Infrastructure Security Agency (CISA) has added the Adobe ColdFusion vulnerabilities, CVE-2023-29298 and CVE-2023-38205, to the Known Exploited Vulnerabilities (KEV) Catalog.
The agency has assigned the due date to patch the actively exploited vulnerabilities as August 10, 2023.
CVE-2023-38203 and CVE-2023-29300 in Adobe ColdFusion Have Joined the CISA KEV Catalog
As of January 8, 2024, CISA has also added the CVE-2023-38203 and CVE-2023-29300 vulnerabilities in Adobe ColdFusion to the Known Exploited Vulnerabilities (KEV) Catalog due to indications of active exploitation.
While these vulnerabilities are recognized for being part of exploit chains, meeting additional criteria, such as providing clear remediation guidance, is essential for inclusion in the KEV Catalog.
Organizations are urged to promptly address CVE-2023-7024 by the designated deadline of January 29, 2024.
Ongoing Exploitation Attempts Targeting Adobe ColdFusion
Fortinet’s IPS telemetry data reveals multiple attempts to exploit the Adobe ColdFusion vulnerability, CVE-2023-29300.

Despite the availability of patches, the attacks persist. The ongoing exploitation attempts raise concerns due to the substantial risk of arbitrary code execution associated with this vulnerability.
Researchers have analyzed the attacks and detected active probing linked to the interactsh tool. The tool is commonly used by researchers to generate specific domain names for exploit testing; however, malicious actors exploited it to validate vulnerabilities through domain monitoring, with domains like mooo-ng[.]com, redteam[.]tf, and h4ck4fun[.]xyz involved.
Fortinet reports that another technique employed by the attackers was the use of a reverse shell. By establishing reverse shells, they exploited vulnerabilities within target systems, thereby gaining access to victims’ computers. Furthermore, some Adobe ColdFusion exploits used Base64-encoded payloads. These attacks originated from various IP addresses, including 81[.]68[.]214[.]122, 81[.]68[.]197[.]3, and 82[.]156[.]147[.]183.
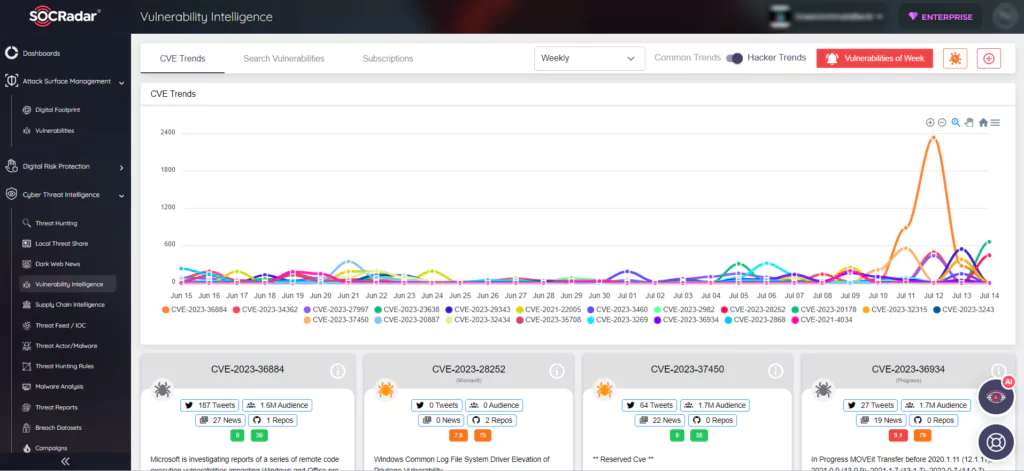
Vulnerability Management with SOCRadar
Protecting your ColdFusion environment is crucial, especially in light of the active exploitation of this critical vulnerability. By combining the necessary security updates, robust patch management practices, and the power of SOCRadar’s vulnerability management capabilities, organizations can effectively protect their systems and safeguard against emerging threats.