
Fortinet Released Patch for FortiOS SSL-VPN RCE Vulnerability CVE-2022-42475
Fortinet has released a patch for a critical zero-day security vulnerability affecting its FortiOS SSL-VPN product. The vulnerability could lead to remote code execution and is actively exploited. Therefore Fortinet urges customers to patch immediately.
What is CVE-2022-42475?
The critical flaw, identified as CVE-2022-42475 (CVSS score: 9.3), relates to a heap-based buffer overflow (CWE-122) vulnerability that could enable an unauthenticated attacker to execute arbitrary code remotely through specially crafted requests.
Olympe Cyberdefense published about the vulnerability on December 9 and made the initial disclosure. The firm reviewed CVE-2022-42475 as “simple to exploit” but has not provided further information about exploitation.
Impacted products by CVE-2022-42475
The flaw affects the following products:
- FortiOS version 7.2.0 through 7.2.2
- FortiOS version 7.0.0 through 7.0.8
- FortiOS version 6.4.0 through 6.4.10
- FortiOS version 6.2.0 through 6.2.11
- FortiOS-6K7K version 7.0.0 through 7.0.7
- FortiOS-6K7K version 6.4.0 through 6.4.9
- FortiOS-6K7K version 6.2.0 through 6.2.11
- FortiOS-6K7K version 6.0.0 through 6.0.14
All users should update to the following versions to fix the security vulnerability, according to a security advisory published today by Fortinet.
Versions for FortiOS:
- 7.2.3 or above
- 7.0.9 or above
- 6.4.11 or above
- 6.2.12 or above
Versions for FortiOS-6K7K:
- 7.0.8 or above
- 6.4.10 or above
- 6.2.12 or above
- 6.0.15 or above
Are there any exploits in the wild forCVE-2022-42475?
The company claimed that the vulnerability is being actively exploited in the wild but has not provided any proof-of-concept yet.
Are there any threat actors actively exploiting CVE-2022-42475?
Fortinet has not yet identified any specific threat actors or groups that have exploited CVE-2022-42475.
How to detect CVE-2022-42475?
Fortinet advises checking for the following indicators of compromise (IOCs) on your systems:
Multiple log entries:
- Logdesc=”Application crashed” and msg=”[…] application:sslvpnd,[…], Signal 11 received, Backtrace: […]“
Filesystem artifacts:
- /data/lib/libips.bak
- /data/lib/libgif.so
- /data/lib/libiptcp.so
- /data/lib/libipudp.so
- /data/lib/libjepg.so
- /var/.sslvpnconfigbk
- /data/etc/wxd.conf
- /flash
Suspicious IP connections from FortiGate:
- 188.34.130[.]40:444
- 103.131.189[.]143:30080,30081,30443,20443
- 192.36.119[.]61:8443,444
- 172.247.168[.]153:8033
How to mitigate CVE-2022-42475?
If you cannot apply the patches right away, users are advised to monitor logs, turn off VPN-SSL, and set up access rules to only allow connections from particular IP addresses.
You can find the original security advisory by Fortinet here.
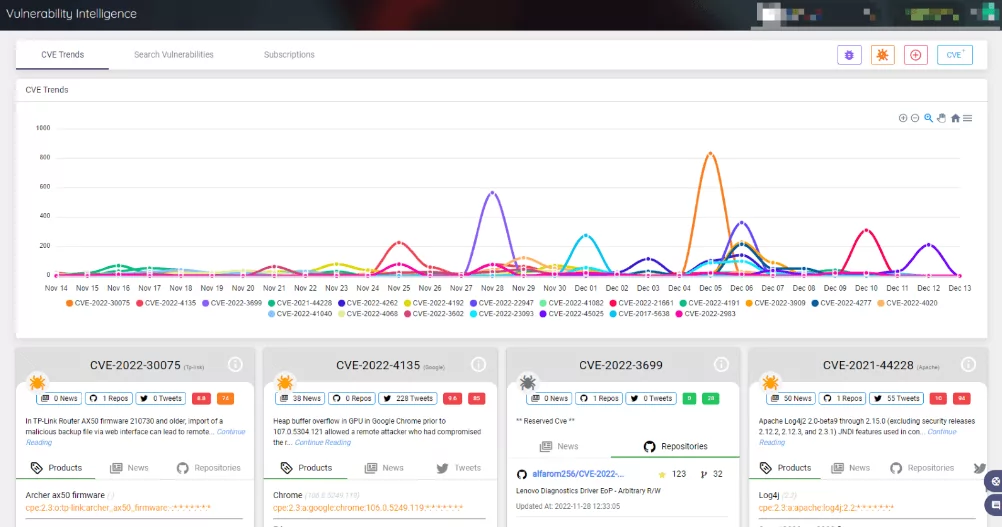
How can SOCRadar help with CVE-2022-42475?
Security teams constantly look for undiscovered assets or vulnerabilities that adversaries could use. When a vulnerability related to a company’s assets is visible on an external network and its applications are published, SOCRadar notifies the company.
The highly accurate scanning engine recognizes and notifies you when a critical vulnerability is cross-referenced to your digital assets, such as:
- Web application firewalls
- VPN appliances
- Network services
- Web applications
- JavaScript libraries
- Software
- CMS applications




































