High Severity Vulnerabilities Fixed by Chrome 115 Update (CVE-2023-3727, CVE-2023-3728, CVE-2023-3730, CVE-2023-3732)
Google recently announced the release of the latest Chrome update, Chrome 115, to the stable channel for Windows, MacOS, and Linux. This update, which promises new features alongside crucial security fixes, is set to roll out in the coming weeks. Here at SOCRadar, we want to delve into the significant security vulnerabilities that have been addressed in this update and why they’re essential for users to be aware of.
High Severity Vulnerabilities Addressed in Chrome 115 Update
The Chrome 115 update addresses a total of 20 security vulnerabilities, four of which have been assigned a high severity rating. Among these is CVE-2023-3727 and CVE-2023-3728, two use-after-free issues in the WebRTC component. Recognized by Google with a bounty of $7,000 each, these vulnerabilities are as significant as they are critical.
Another high severity flaw that Chrome 115 resolves is CVE-2023-3730, a use-after-free issue in Tab Groups, earning the researcher who reported it a $2,000 bug bounty. Further, CVE-2023-3732, an out-of-bounds memory access in Mojo, was reported by Mark Brand of Google Project Zero. As per Google’s policies, no bug bounty was issued for this internal discovery.
A use-after-free vulnerability can allow an attacker to execute arbitrary code, leading to possible system crashes or data corruption. An out-of-bounds memory access vulnerability, on the other hand, could allow an attacker to access information that they are not supposed to, potentially leading to data breaches.
Medium-Severity Flaws Patched
Chrome 115 also patches several medium-severity vulnerabilities, characterized as inappropriate implementations in several components, including WebApp Installs, Picture In Picture, Web API Permission Prompts, Custom Tabs, Notifications, and Autofill. These vulnerabilities can also have serious consequences if exploited, possibly allowing attackers to bypass intended access restrictions and perform unauthorized actions.
Tools like SOCRadar, which monitor for known vulnerabilities and cyber threats, play a vital role in safeguarding against such threats. Our platform could flag these vulnerabilities, thus helping organizations to promptly apply critical patches.
Google has not mentioned any active exploitation of these vulnerabilities, the immediate application of this update is highly advised to shield against potential exploits.
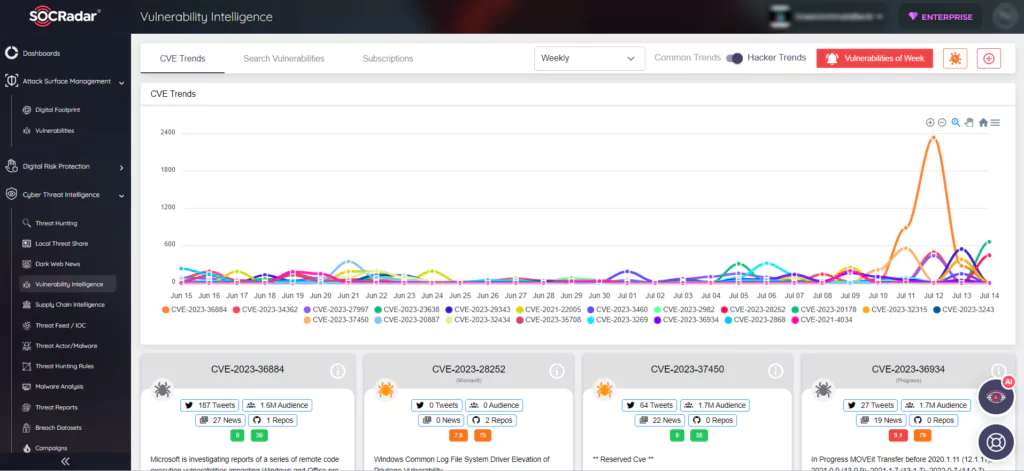
Proactive Cybersecurity: The Importance of SOCRadar’s Vulnerability Intelligence
In conclusion, it’s of utmost importance to keep your applications, like Google Chrome, up-to-date to diminish the risk of potential security vulnerabilities. Users are strongly encouraged to update to the latest version, Chrome 115.0.5790.98 for Linux and Mac, or Chrome 115.0.5790.98/99 for Windows, at their earliest convenience.
With the Vulnerability Intelligence module in SOCRadar, you can remain a step ahead of these potential threats. This comprehensive module proactively tracks and alerts you about critical vulnerabilities allowing for timely detection and remediation. By using SOCRadar, organizations can ensure a proactive, dynamic approach to managing their digital security and staying on top of the constantly evolving landscape of cybersecurity threats.