How To Find Domain Ownership in the GDPR Era
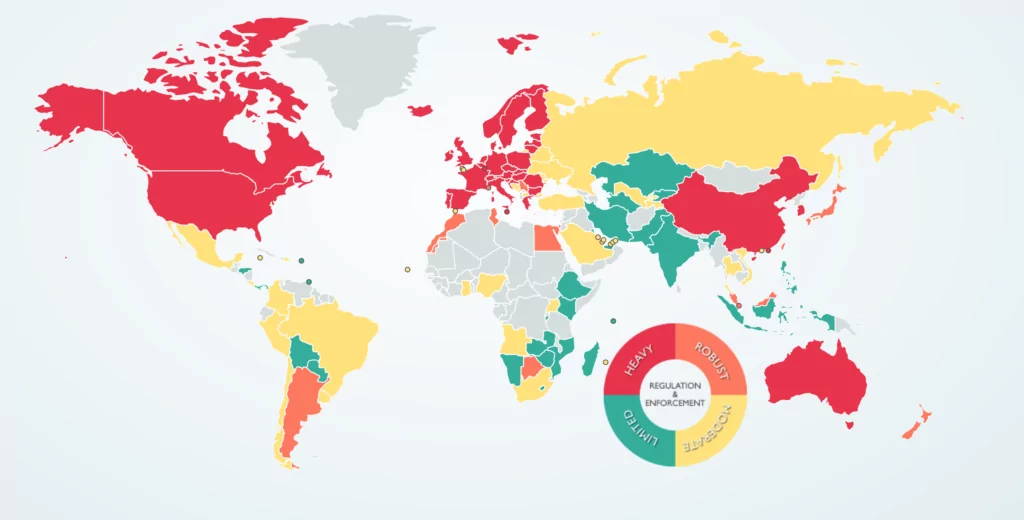
Data protection regulations
Data protection is an essential process in keeping important information safe and away from threat actor compromise. The criticality of this process is drastically increasing with the increase of data itself being stored in different storages. To find safe storage is one of the primary things in a company.
With data protection being an important process, in the meantime a big issue as well, there have been regulations put in place.
Data protection regulations are comprehensive legal provisions that address the security of personal data of the users coming from the country issuing the regulations.
Starting from the regulation of 28 European Union countries with issued GDPR, there have been other regulations put into force in many other countries around the world like:
- CCPA: California consumer privacy act
- LGPD: Brazilian general data protection law
- PDPA: Personal data protection act
- PDPB: Personal data protection bill
- APPs: Australian Privacy Principles
- LPPD: Law the protection of personal data (KVKK)
General data protection regulation
This data protection act was first introduced in 2018 and its very strict laws have ever since been applied by all countries of the EU and European Economic Area (EEA). In cases of data breaches, there have been experienced heavy fines for the company affected.
The regulations put in place by GRPD have helped the personal data of citizens of the EU to be kept secure. Its main idea is to allow citizens to have control over their personal data.

Some key points of the GDPR
GDPR constitutes 11 chapters and 91 articles. This regulation requires all companies collecting citizens (under the protection of GDPR) to describe how they use, and handle possible issues with that data.
Companies have to report data breaches on the strict timeline of 72 hours of learning of the breach, if they fail to do so, they can end up getting enormous fines.
Depending on the level of violation, fines for non-compliance can be up to 4% of the company’s global annual revenue.
Part of the regulation requires Data Protection Impact Assessments to be performed by companies, to identify consumer data risk and ensure those risks have been handled properly.
WHOIS records
Since the GDPR has made changes in the way data is collected and stored, it has affected the WHOIS database as well.
WHOIS database is a publicly accessible database given in human-readable format. It contains detailed information regarding the ownership of a domain as well as name server data. Plainly put, every registered domain, is collected by whois records, then given publicly to everyone on the internet.
Containing data of internet users, processing and giving this PII to the public, means this data can somehow be abuse. This fact makes WHOIS records be in conflict with the GDPR requirements.
Domain ownership
When a domain is registered, the person responsible for the registration needs to provide contact information to be identified, such as name, address, email address, phone number, and administrative contact. These can be personal info, or info of the business, in both cases there is personal data given.
Although these public WHOIS records are considered to be an invasion of privacy, there are many investigators and security professionals, and enthusiasts trying to uncover dangerous/malicious/phishing website owners. To do so, they need to access WHOIS information. So, now in the GDPR era, how can they find WHO IS behind these malicious sites.
Ways to find domain ownership
Investigators can still find domain ownership using different practices:
Reverse domain lookup
Maybe not a full solution to the problem and not a short cut to finding the owner of a domain, reverse domain check helps your research.
There are different OSINT tools you can use for this check, as examples we can say yougetsignal, spyontheweb and viewdnsinfo. These tools list all the domains registered in the same IP address as the domain you are researching. You may want to check a few tools, to get a fuller list.
After you get the domains hosted in the same IP, you may check if any of these does not use privacy services – this can lead to the owner.
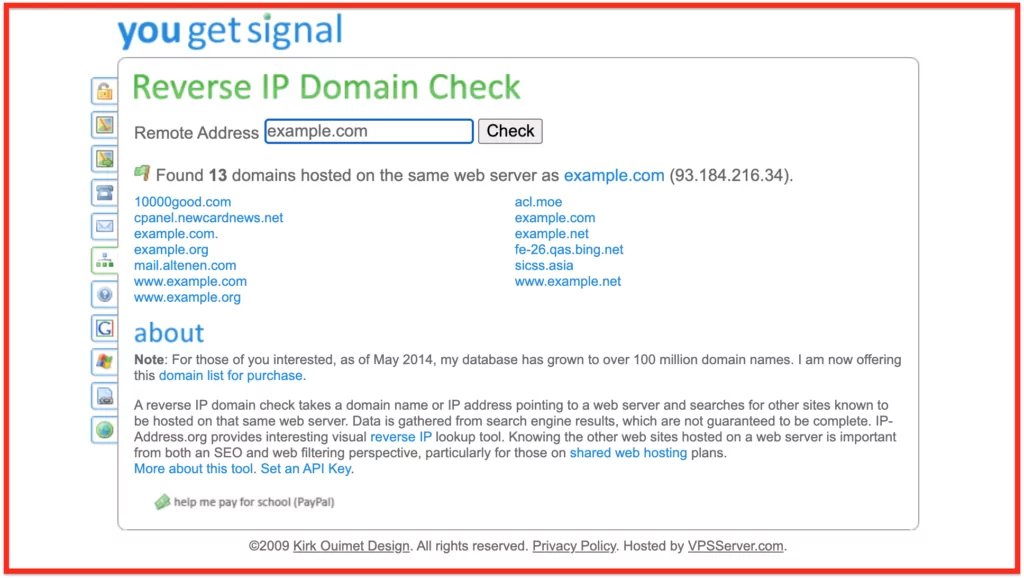
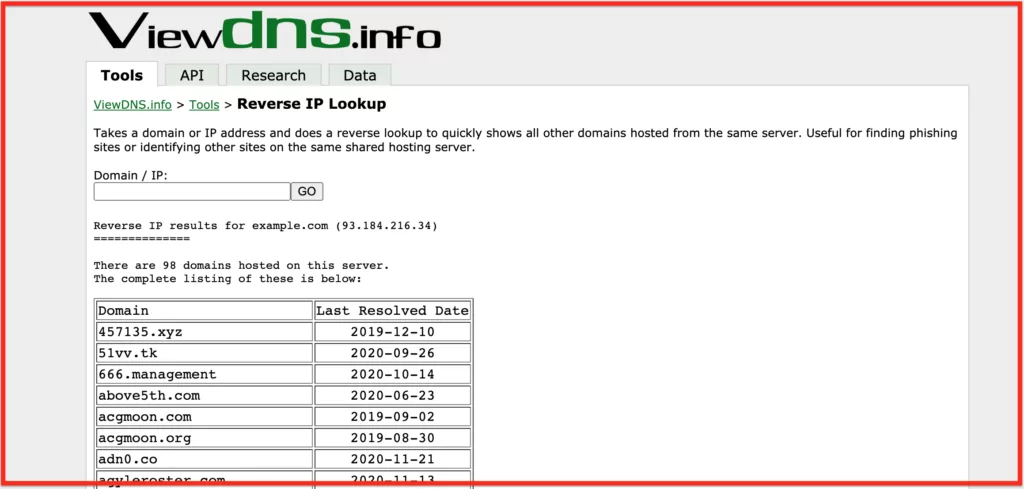
A similar option is to check for reverse WHOIS. That is, find the domains from the registrant’s name or email. This is maybe not exactly what you’d expect from this post because it sounds like a primitive way to find domain ownership, however, it can be helpful. Let’s say there is a known imposter who has registered many malicious domains, and you suspect he/she may be the owner of the domain being subject to the research. Checking domains registered by that owner, you will come closer to your research.
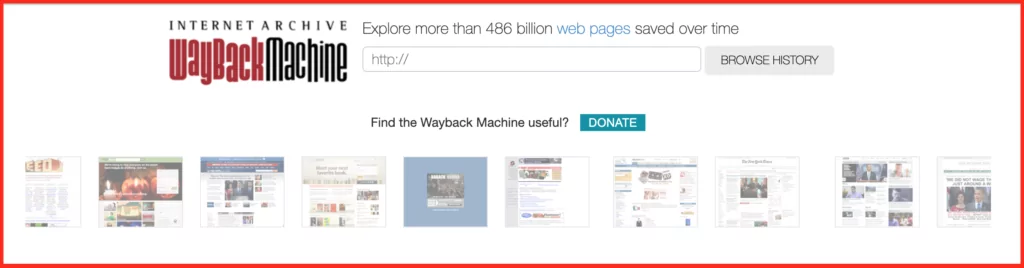
Website archives
Publicly available website archives like Wayback Machine show a historical version of the website being investigated. Contact details can be found this way, however, let’s not forget that domain ownership can be given to someone else. This means the chances for the contact details to be of the current owner are 50-50, not to say lower. Yet, it’s a good thing to try.
Historic WHOIS data
Domaintools is a very useful OSINT tool that gives access to historic WHOIS data of a domain. This way you can directly access previously registered WHOIS records of a domain. However, the same issue as with website archives stands here as well.
Contact the registrar
The three above-mentioned options are not ideal, and will maybe take too long to direct you to the right owner, however, they show there still is a way.
One of the most secure, however not fast ways to find domain ownership is to contact the registrar. For this, you would need an attorney and very good evidence to justify the reason for requesting the information. Including attorneys and legal actions will take time, which makes this not a very preferable route – timeliness is key in these cases.
Discover SOCRadar® Community Edition for free
With SOCRadar® Community Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.