
How to Find Subdomains Using Free Online Services?
Subdomains are critical assets of your software applications and server infrastructure. They contain numerous details that can be useful to threat actors as a way into your system.
In essence, a subdomain is simply an addition to the root/main domain, however, it ends up being a completely independent site.

Reasons to have a subdomain can be different and the most important one is organizing website content. Very frequent examples you may have come across are:
- Blog.example.com
- Forum.example.com
- Mail.example.com
- Cloud.example.com
- Example.com
The list goes on to tens or even hundreds of them.
Why are subdomains important?
Developers usually test new features using dev.example.com or test.example.com, instead of directly updating the existing domain. However, after the official release, these subdomains can end up being not managed well enough, and that’s what may lead to security issues and serious risk to your business.
A hacker can uncover critical vulnerabilities affecting your assets by simply finding applications running on an exposed but forgotten subdomain, and you may be prone to an attack without realizing it.
In order to protect your assets, in this case, subdomains, you need to first see how exposed you are. To do so, it’s advised to run your domain against some subdomain finder tools. This will be useful for understanding your attack surface.
There is, of course, the old fashioned way of brute-forcing possible combinations – but that is definitely time-consuming, and hackers have faster and easier solutions nowadays.
Quick tip: Some services might not give complete results, and some might give old subdomains that are not currently used. If you decide to use free services to find your subdomains, we advise using a couple of them and saving results from all, just in case.
Besides, we gave you a lot of options, and the majority of services are fast. You will be doing a great deed to your organization simply by validating your results.
Free online services
There are many paid tools that will give you in-depth knowledge of your subdomains, but you can also leverage free services. They will do the job just as fine (if you know how to use them).
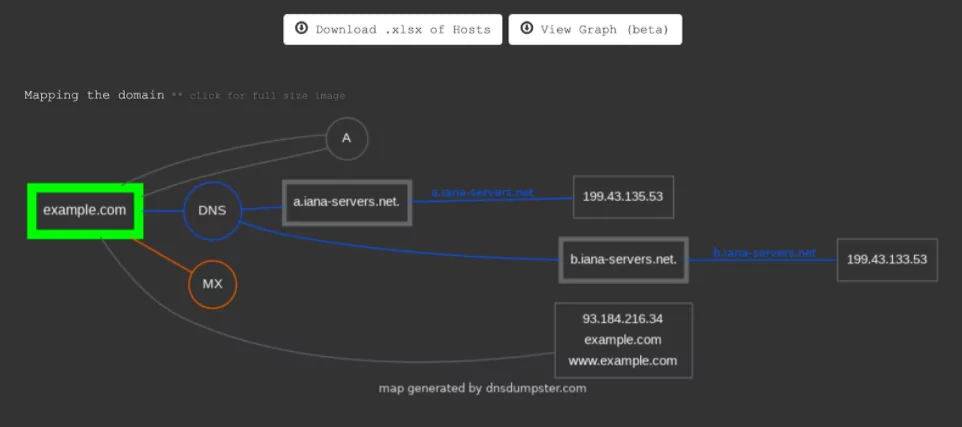
1. DNSdumpster
DNS dumpster is a HackerTarget.com project used to get host-related information. It gives DNS server, MX record, TXT record information as well.
A graph view and .xlsx downloadable file option are also available.
2. Nmmapper
NMMapper searches the domain you enter in the search box in different tools like Sublist3r, Amass, Nmap, etc. These are known to be powerful tools used for subdomain enumeration, but installing and using them might be harder than using a free online service.

You have the option to find the IP address the results resolve to, but that can be time-consuming.
3. Sypse
Spyse’s subdomain finder service allows you to collect subdomains of any domain. Sypse offers many tools and you can get the paid version for more in-depth results. However, the subdomain results from the free version alone can be quite useful.
4. Netcraft
Not exactly the perfect tool to find subdomains because as noted in the website “Only web sites which have been visited by users of the Netcraft Extensions at least five times within the last six months will be shown in the search results.”. However, it has a large domain database and you can profit from it. The way that this tool operates, is finding all (sub)domains containing a keyword that you give.
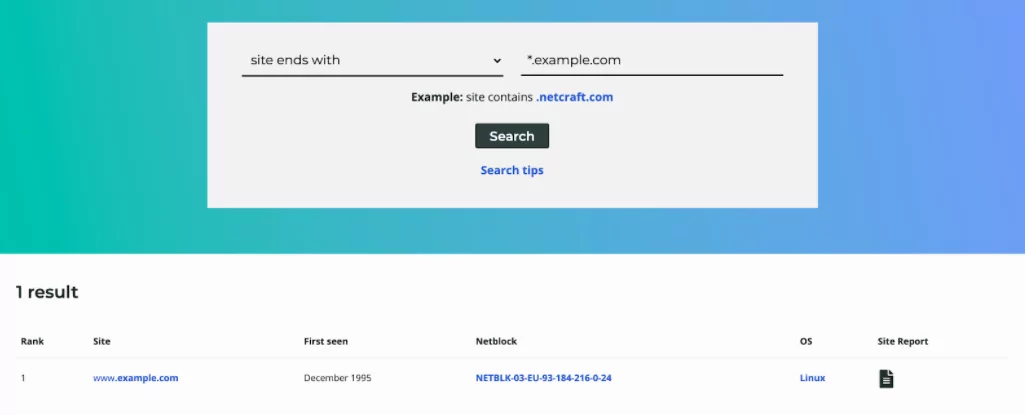
Without losing time on different tools to find additional information about a subdomain, you can easily view the detailed report that Netcraft offers.
5. Pentest-Tools
Pentest-Tools offers only 2 free scans daily, but that will do the job considering the in-depth reports it offers and the option to download those reports in PDF as well.
It’s easy to use! You write the domain name, hit scan, and get the report in a short while, depending on the number of subdomains you will retrieve.
6. SecurityTrails
SecurityTrails possesses 12 years of historical DNS records and offers it to users for free. It also offers a list of all subdomains of a root domain together with the hosting and mail provider.
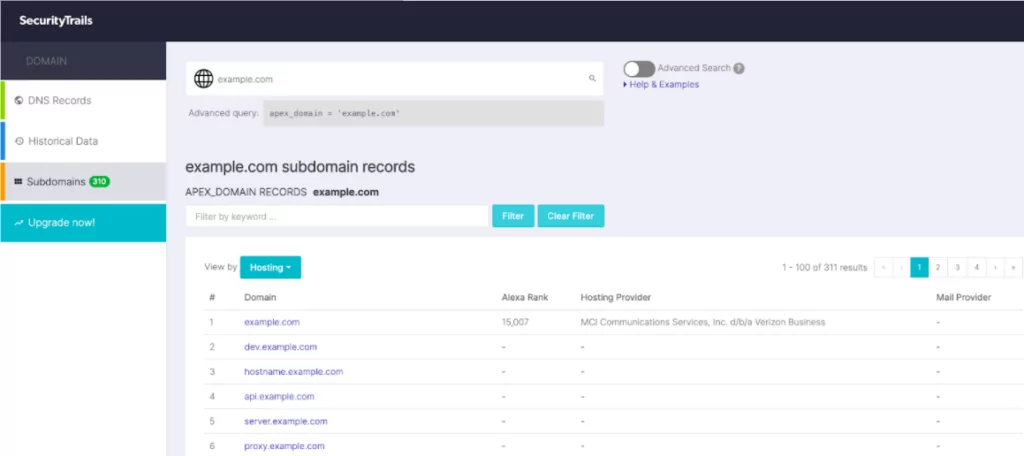
Since it contains historical data, the list can be overlong, but the good thing is that you get more results than in other tools. Besides, you can always use the filtering option to shorten the list and get more accurate results.
7. Censys
Censys is an amazing tool. You can benefit from it in different ways, like getting information about websites or IP addresses. Although it is not intentionally meant to retrieve subdomain information, it can still be more useful than many other free services.
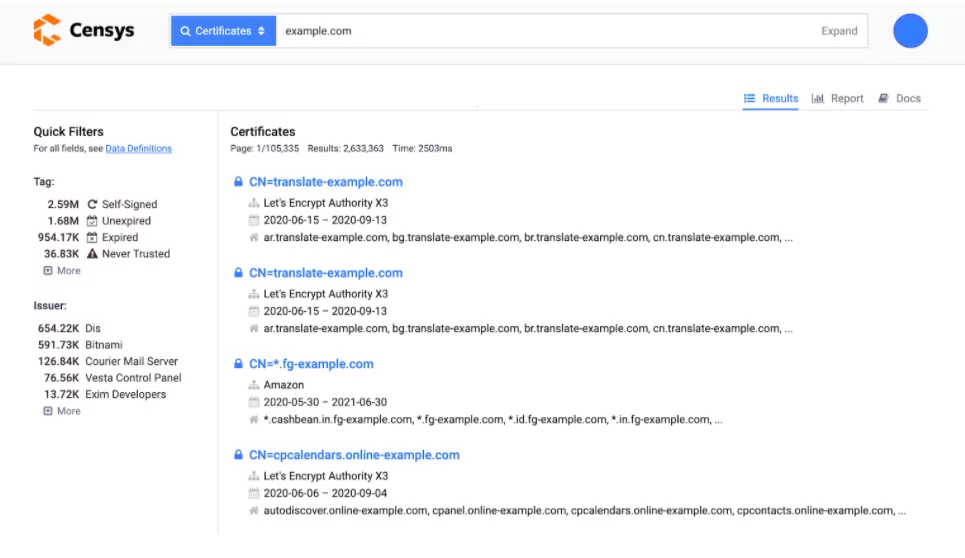
If you select the certificate search, Censys gives you information about certificates registered in any domain containing the words you write in the search box. If you write your domain name, the results list can be useful but not well filtered. However, if you do your search as follows Example.com, it will limit the search only to your subdomains.
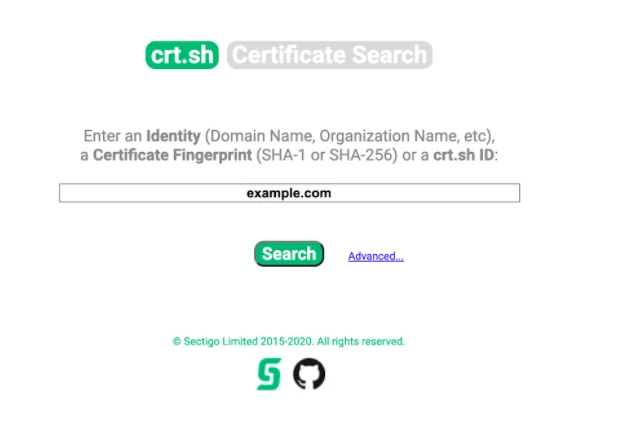
8. Crt.sh
Just like Cencys, Crt.sh offers a certificate search service. It is completely free and gives detailed information about certificates registered on a domain or subdomain.
You can simply write the root domain, and the results will end up in long lists of certificates. One thing you need to be careful about is that it gives duplicate results and to not get confused you need to make them unique. Another disadvantage is that it doesn’t offer an option to download the list.
9. BinaryEdge
Another not completely free tool is BinaryEdge. It is a powerful tool to find, besides others, subdomains as well. It offers 250 queries a month for the free version, and that is quite enough to once in a while check your digital assets.
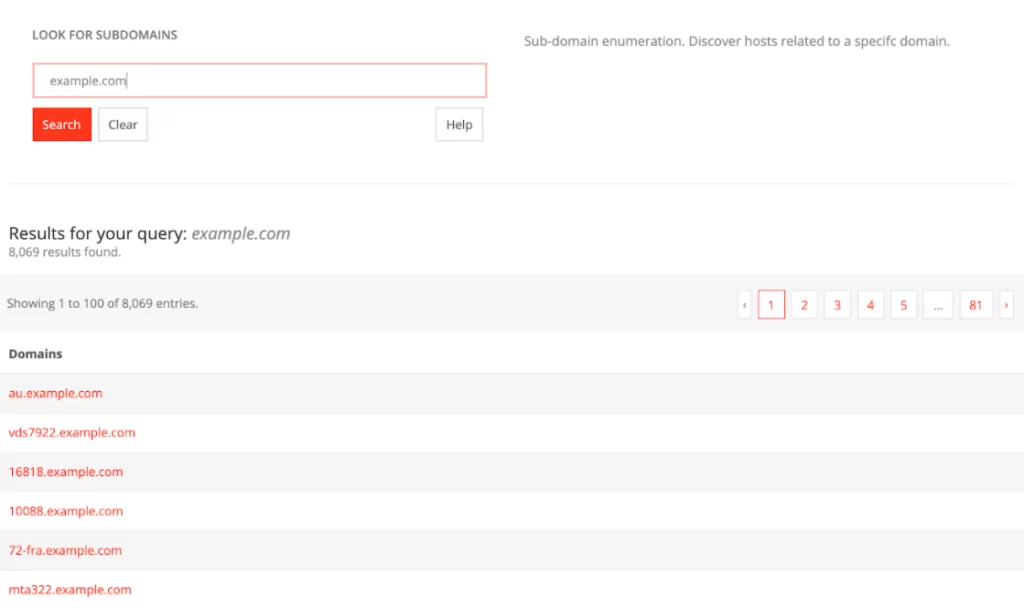
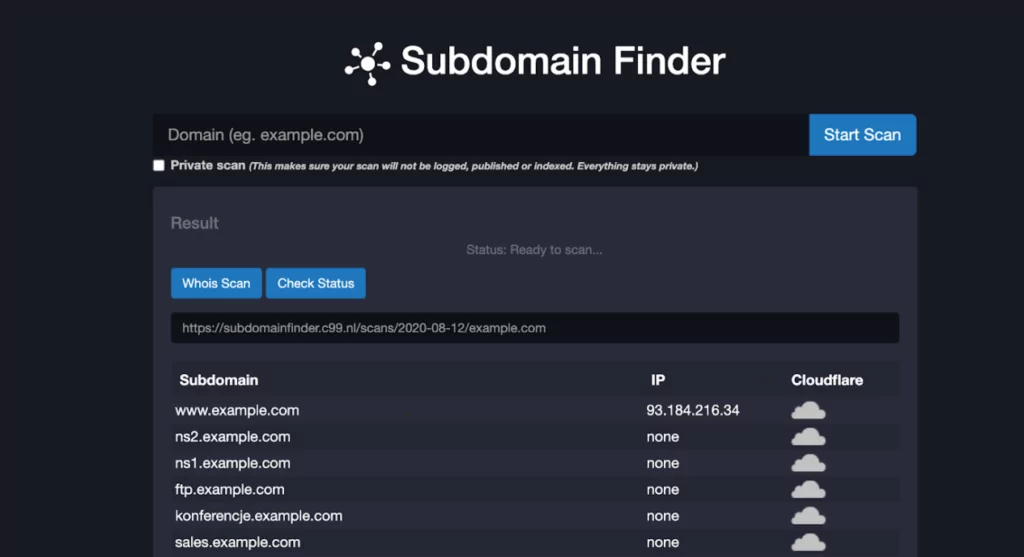
10. Subdomain Finder
Subdomainfinder is specially designed to retrieve subdomains of a given root domain. After the result you will see subdomain, which you can visit by simply clicking on it, the IP address it resolves, and whether it is tunneling through CloudFlare or not.
Discover SOCRadar® Community Edition for free
With SOCRadar® Community Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.



































