
Ivanti Avalanche Received an Update for Over Two Dozen Vulnerabilities (CVE-2024-24996, CVE-2024-29204…)
Ivanti has recently issued security updates to address multiple vulnerabilities in Avalanche. These vulnerabilities, ranging from medium to critical severity, pose risks such as information disclosure, command execution, and Denial-of-Service (DoS) attacks.
Ivanti Avalanche serves as a Mobile Device Management (MDM) solution, allowing administrators to remotely manage devices and updates.
Importantly, the update includes two critical vulnerabilities, identified as CVE-2024-24996 and CVE-2024-29204. These vulnerabilities both originate from heap overflows.
What is CVE-2024-24996 / CVE-2024-29204?
CVE-2024-24996 is a critical heap overflow vulnerability found in the WLInfoRailService component of Ivanti Avalanche. An unauthenticated, remote attacker can exploit this vulnerability to execute arbitrary commands.
The severity score of this vulnerability on the Ivanti advisory is 9.8 out of 10 on the CVSSv3 scale.
Similarly, CVE-2024-29204 is another critical heap overflow vulnerability, allowing the execution of arbitrary commands. It affects the WLAvalancheService component of Ivanti Avalanche.
The severity score for this vulnerability on the Ivanti advisory is also 9.8 out of 10 on the CVSSv3 scale.
Notably, the exploitation of these critical vulnerabilities does not require any user interaction.
To stay informed about emerging security vulnerabilities affecting your digital assets, leverage SOCRadar’s Attack Surface Management (ASM).
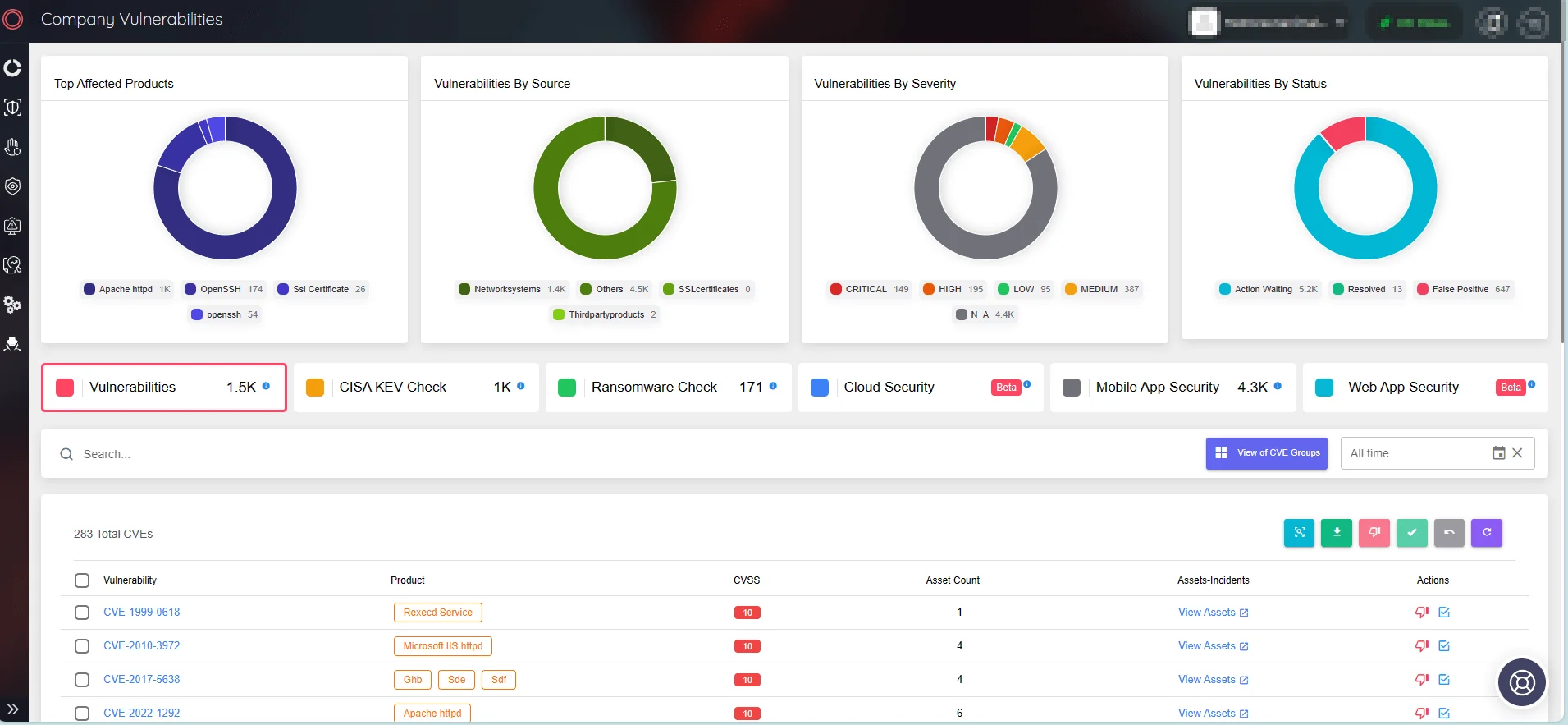
Safeguard your products and software against emerging vulnerabilities with SOCRadar’s ASM
The High-Severity Vulnerabilities in Ivanti Avalanche MDM
Ivanti’s patch encompasses a total of 27 vulnerabilities. The remaining 25 issues, excluding the critical heap overflows, are of medium to high severity. The following is a brief overview of the update’s high-severity vulnerabilities.
Vulnerabilities in the web component of Ivanti Avalanche:
Path traversal vulnerabilities
- CVE-2024-23535 (CVSS: 8.8)
- CVE-2024-24992 (CVSS: 8.8)
- CVE-2024-24994 (CVSS: 8.8)
- CVE-2024-24997 (CVSS: 8.8)
- CVE-2024-24998 (CVSS: 8.8)
- CVE-2024-24999 (CVSS: 8.8)
- CVE-2024-25000 (CVSS: 8.8)
- CVE-2024-27976 (CVSS: 8.8)
Race Condition (TOCTOU) vulnerabilities
- CVE-2024-24993 (CVSS: 8.8)
- CVE-2024-24995 (CVSS: 8.8)
Unrestricted File-upload vulnerability
- CVE-2024-23534 (CVSS: 8.8)
These vulnerabilities, if exploited, could enable an authenticated, remote attacker to execute arbitrary commands as SYSTEM.
The two other high-severity vulnerabilities do not reside in the web component; one of them is yet another heap overflow issue, affecting WLInfoRailService, tracked as CVE-2024-22061 (CVSS: 8.1), and the other is a Use-After-Free vulnerability in WLAvalancheService that leads to Remote Code Execution (RCE), tracked as CVE-2024-27975 (CVSS: 8.8).
Which Ivanti Avalanche versions are affected?
All older versions of Avalanche, preceding version 6.4.3, are susceptible to the vulnerabilities outlined in the update.
Have these vulnerabilities been exploited in the wild?
Ivanti has stated that it is unaware of any customers being exploited by these vulnerabilities prior to their public disclosure via the advisory.
Are there any mitigations for these vulnerabilities?
Ivanti has not mentioned the availability of any mitigation methods for these vulnerabilities.
How to apply the patches for CVE-2024-24996, CVE-2024-29204, and the other recently disclosed vulnerabilities?
To mitigate the security vulnerabilities, it is strongly advised to download the Avalanche installer and upgrade to the newest version, 6.4.3.
You can access the update through Wawelink, while a comprehensive guide for updating the product is available here.
Receive the Latest Vulnerability Insights
Use SOCRadar’s Vulnerability Intelligence to easily manage vulnerabilities and prioritize patching.
The Vulnerability Intelligence feature keeps you up to date on known vulnerabilities, exploits, repositories, and emerging hacker trends. Such insights can help organizations improve vulnerability management and protect themselves from potential cyberattacks.
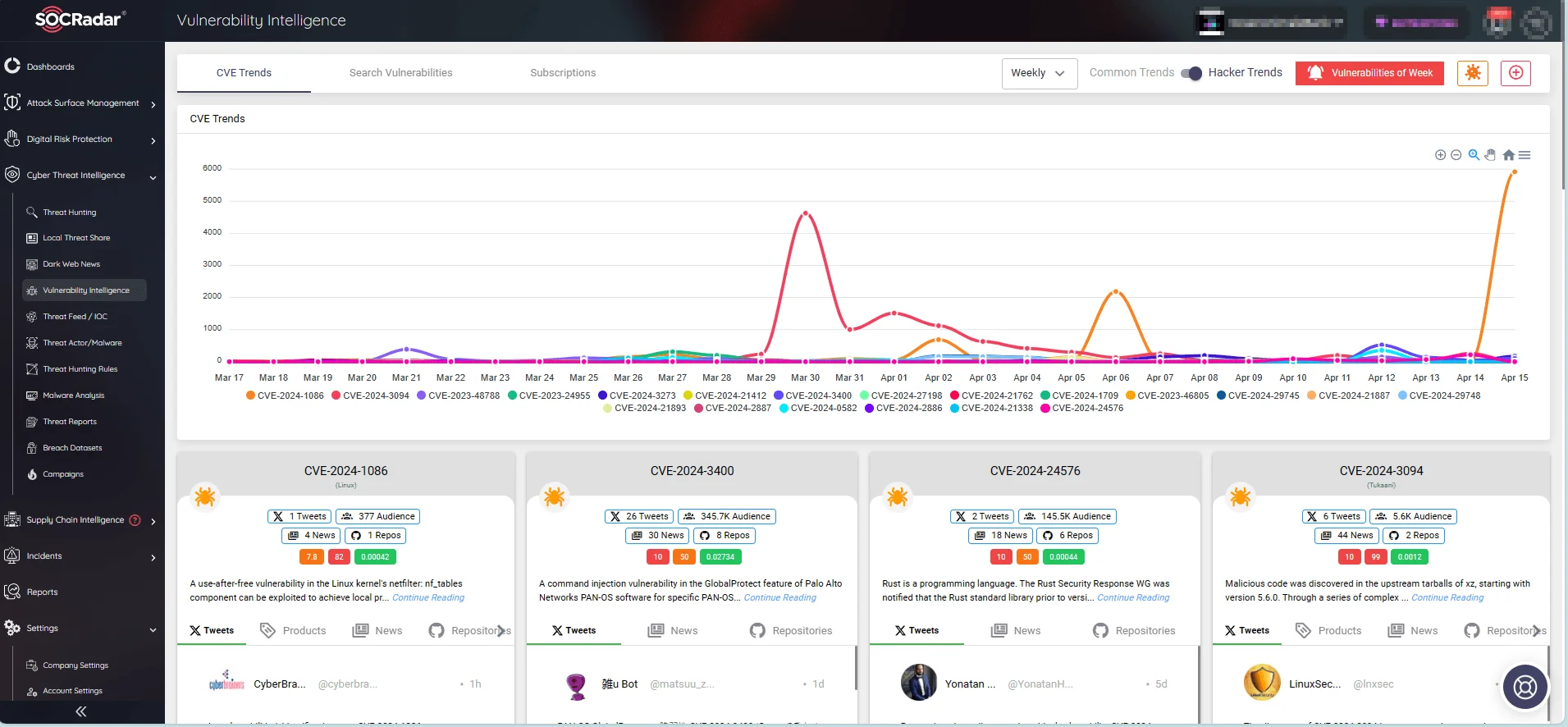
SOCRadar’s Vulnerability Intelligence, CVE Trends




































