LOBSHOT hVNC Malware: A New Threat Distributed Through Google Ads
Cybersecurity researchers have discovered a new malware, called ‘LOBSHOT,’ distributed through Google ads.
This malware allows cybercriminals to take over infected Windows devices by using hVNC.
The hVNC is a type of VNC remote access software customized to operate on a hidden desktop within an infected device rather than the main desktop used by the device owner. This allows malicious actors to gain complete remote control over a Windows desktop without the victim’s knowledge.
LOBSHOT Malware Spreads via Fake Sites, Enables Remote Control
Recently, cybercriminals have increasingly been using Google ads to distribute malware through search results. They do so by impersonating legitimate websites for popular applications such as 7-ZIP, VLC, OBS, Notepad++, CCleaner, TradingView, and Rufus.
These ads appear to promote the legitimate AnyDesk remote management software but actually lead to a fake AnyDesk site at amydeecke[.]website.
This website distributed a harmful MSI file that executed a PowerShell command to download a DLL file from download-cdn[.]com, a domain associated with the TA505/Clop ransomware gang in the past.
However, the ownership of the domain has changed, and it is unclear whether TA505 is still using it, according to threat researcher Tommy Madjar.
The downloaded DLL file contains LOBSHOT malware, which is saved in the C:ProgramData directory and then executed using RunDLL32[.]exe. According to the report by Elastic Security Labs, more than 500 unique LOBSHOT samples have been observed since July 2022. These samples are typically compiled as 32-bit DLLs or executables, ranging from 93 KB to 124 KB in size.
The main feature of the malware is its hVNC module, which involves creating a hidden desktop and linking it to the malware. This allows the attacker to gain complete remote control over the infected device, enabling them to capture screenshots, use the keyboard and mouse, and perform other actions.
A Stealthy Malware that Evades Detection and Gathers Device Information
Lobshot uses a technique called dynamic import resolution and tries to avoid being detected by resolving the names of Windows APIs at runtime.
After being executed, the malware will verify whether Microsoft Defender is active or not. If it finds that the Defender is active, it will immediately stop its execution to avoid getting detected.
But if it doesn’t detect the Defender, it will create registry entries to start itself automatically whenever the user logs in to Windows.
After that, it will extract information about the infected device, such as the currently running processes, and transmit it to the attacker’s server.
LOBSHOT Malware Targets Over 50 Cryptocurrency Browser Extensions
LOBSHOT targets more than 50 browser extensions related to cryptocurrency wallets, including Chrome, Edge, and Firefox.
After identifying the Chrome, Edge, and Firefox extensions, the LOBSHOT malware executes a file located in the C:ProgramData directory. However, researchers were unable to confirm whether the file is used to steal the extension data or has some other function, as it was not present in their analysis.
The attackers behind LOBSHOT can perform various actions on an infected device by issuing commands to start a new explorer[.]exe process, opening a Run command window, launching a browser, changing system settings, modifying sound settings, accessing the clipboard, and more. Lobshot can also change its command-and-control server and update itself.
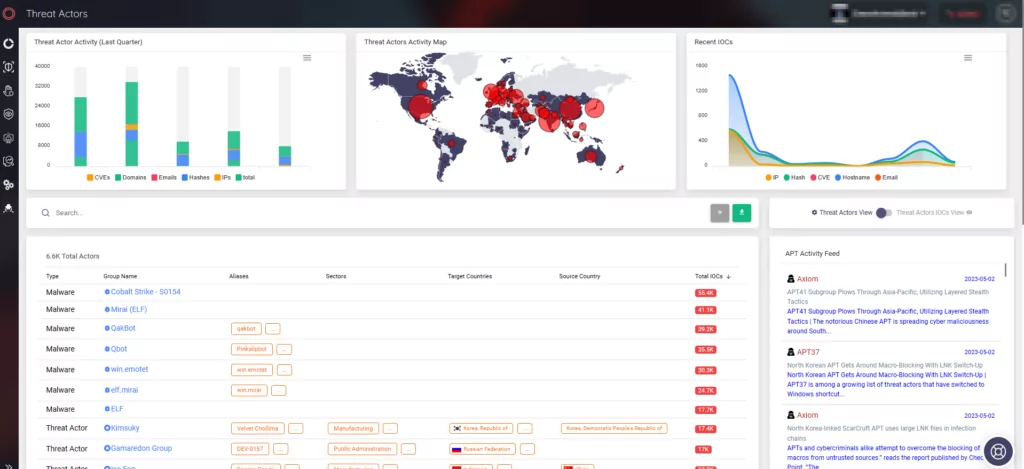
Stay Ahead of Threats with SOCRadar
SOCRadar tracks the behavior of threat actors and malware to keep your organization informed about potential risks. With the Threat Actor/Malware tab, you can stay up-to-date with the latest information on threat activities and indicators of compromise.