

Microsoft November 2022 Patch Tuesday Fixed 11 Critical Vulnerabilities and 6 Zero-Days
What are the Vulnerabilities?
Microsoft November 2022 Patch Tuesday has been released with patches for a total of 68 vulnerabilities, which include 6 actively exploited zero days and 11 critical vulnerabilities.
The number for each vulnerability category is shown below:
- 27 Elevation of Privilege Vulnerabilities
- 16 Remote Code Execution Vulnerabilities
- 11 Information Disclosure Vulnerabilities
- 6 Denial of Service Vulnerabilities
- 4 Security Feature Bypass Vulnerabilities
- 3 Spoofing Vulnerabilities
How Critical are the Vulnerabilities?
The critical vulnerabilities in the Patch Tuesday and the products they affect are as follows:
| Product | CVE ID | CVE Title | CVSS Score |
| Azure | CVE-2022-39327 | GitHub: CVE-2022-39327 Improper Control of Generation of Code (‘Code Injection’) in Azure CLI | 9.8 |
| Microsoft Exchange Server | CVE-2022-41040 | Microsoft Exchange Information Disclosure Vulnerability | 8.8 |
| Microsoft Exchange Server | CVE-2022-41080 | Microsoft Exchange Server Elevation of Privilege Vulnerability | 8.8 |
| Role: Windows Hyper-V | CVE-2022-38015 | Windows Hyper-V Denial of Service Vulnerability | 6.5 |
| Windows Kerberos | CVE-2022-37967 | Windows Kerberos Elevation of Privilege Vulnerability | 7.2 |
| Windows Kerberos | CVE-2022-37966 | Windows Kerberos RC4-HMAC Elevation of Privilege Vulnerability | 8.1 |
| Windows Point-to-Point Tunneling Protocol | CVE-2022-41044 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | 8.1 |
| Windows Point-to-Point Tunneling Protocol | CVE-2022-41039 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | 8.1 |
| Windows Point-to-Point Tunneling Protocol | CVE-2022-41088 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | 8.1 |
| Windows Scripting | CVE-2022-41118 | Windows Scripting Languages Remote Code Execution Vulnerability | 7.5 |
| Windows Scripting | CVE-2022-41128 | Windows Scripting Languages Remote Code Execution Vulnerability | 8.8 |
See Microsoft’s release note for a complete list of vulnerabilities and affected products.
How Do the Vulnerabilities Work?
Zero Day Vulnerabilities
- CVE-2022-41128 (CVSS Score: 8.8): The JScript9 scripting language in the Windows Scripting Languages is vulnerable to remote code execution. The vulnerability requires users to enter an attacker-crafted website.
- CVE-2022-41040 (CVSS Score: 8.8): The attacker could run the PowerShell in the context of the system.
- CVE-2022-41082 (CVSS Score: 8.8): An unauthenticated, remote attacker could use arbitrary code execution to target Microsoft Exchange server accounts and execute malicious code via a network call.
- CVE-2022-41073 (CVSS Score: 7.8)and CVE-2022-41125 (CVSS Score: 7.8): Exploiting these vulnerabilities could enable an attacker with System privileges.
- CVE-2022-41091 (CVSS Score: 5.4): To circumvent Mark of the Web (MOTW) defenses, an attacker can create a malicious file, which results in a limited loss of integrity and accessibility of security features.
Critical Vulnerabilities
- CVE-2022-39327 (CVSS Score: 9.8): Azure CLI versions before 2.40.0 are vulnerable to code injection. Only the Windows-based computers that run any version of PowerShell and Azure CLI commands containing the ‘&’ or ‘|’ symbols are affected.
- CVE-2022-41080 (CVSS Score: 8.8): The vulnerability allows privilege escalation on Microsoft Exchange Server.
- CVE-2022-37966 (CVSS Score: 8.1): Successful exploitation could enable an unauthenticated attacker with administrator rights. Windows AD environments could be breached by an attacker using cryptographic protocol flaws in RFC 4757 (Kerberos encryption type RC4-HMAC-MD5) and MS-PAC.
- CVE-2022-41039 and CVE-2022-41044 (CVSS Scores: 8.1): A RAS server may receive a connection request specially crafted by an unauthenticated attacker, which may result in remote code execution (RCE).
- CVE-2022-41088 (CVSS Score: 8.1): An attacker can send a specially crafted malicious PPTP packet to a PPTP server to exploit this vulnerability, which could result in remote code execution.
- CVE-2022-41118 (CVSS Score: 8.1): The JScript9 and Chakra scripting in Windows Scripting Languages are vulnerable to remote code execution.
- CVE-2022-37967 (CVSS Score: 7.2): An authenticated attacker could exploit the cryptographic protocol flaw in Windows Kerberos and modify Kerberos PAC to gain administrative privileges.
- CVE-2022-38015 (CVSS Score: 6.5): Successful exploitation could allow a Hyper-V guest to interfere with the host’s functionality.
How to Detect any Malicious Activity Related to These Vulnerabilities?
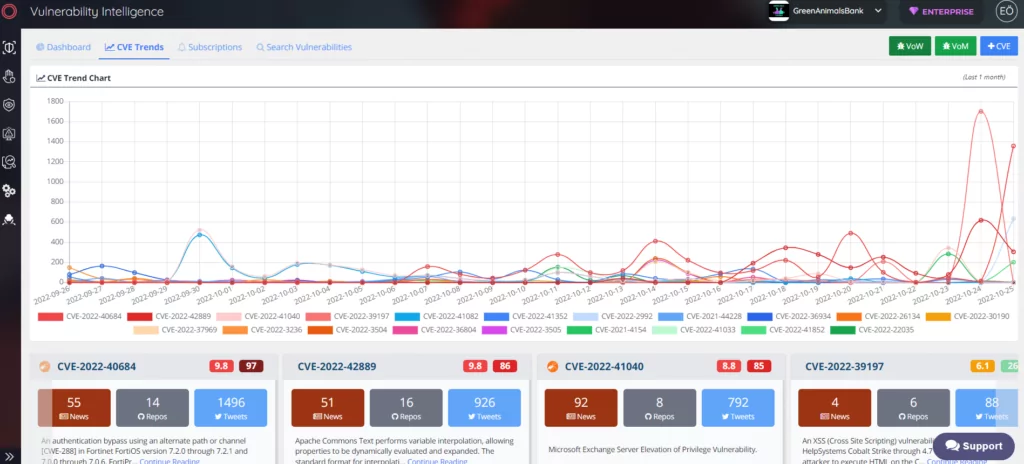
SOCRadar Extended Threat Intelligence automatically discovers your assets and alerts you when a vulnerability may affect your systems. It helps you gain actionable insight and better prioritize fixes.
How to Protect Against the Vulnerabilities?
Follow Microsoft’s security update guide and apply the patches accordingly as soon as possible to protect your products from being vulnerable.










