Money Message Ransomware Leaks MSI Signing Keys for Intel Boot Guard
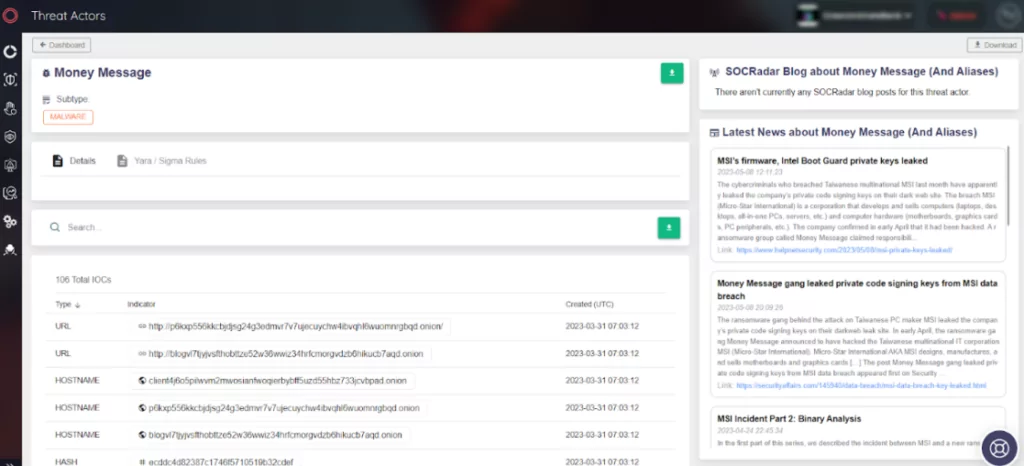
MSI, a leading Taiwanese PC manufacturer, suffered a ransomware attack last month. The threat actors behind the attack, the Money Message gang, published the company’s private code signing keys on a dark website last week for double extortion.
In the March attack, threat actors claimed to have stolen 1.5TB of data and demanded a $4 million ransom payment, threatening to leak MSI’s data.
Which MSI Products Are Affected?
The full leaked data set includes firmware image signing keys for 57 PCs as well as private signing keys for Intel Boot Guard, which is used on 116 MSI products.
Several device vendors, including Intel, Lenovo, and Supermicro, are thought to be affected by Boot Guard keys. However, Intel Boot Guard appears to be ineffective on some devices based on the 11th Tiger Lake, 12th Adler Lake, and 13th Raptor Lake.
How Does Intel Boot Guard Leak Affect Security?
Intel Boot Guard is a hardware security technology that prevents computers from running malicious UEFI firmware. UEFI bootkits (a form of rootkit) could especially be dangerous because they load before the operating system (OS), thus avoiding detection and persistence even when the user reinstalls the OS.
The security feature, Intel Boot Guard, verifies if signatures are valid by using a private signing key and a public key built into Intel hardware. Since the embedded keys that verify leaked keys cannot be modified, it leaves devices vulnerable to malicious firmware and renders the security feature useless.
Attackers Could Deploy Malicious Updates
Although MSI reported that the affected systems are back to normal and their financial business was not significantly impacted, the company warned users to only get firmware/BIOS updates from their official website and not to download files from other sources.
Unfortunately, the Intel OEM (Original Equipment Manufacturer) keys leak could allow threat actors to sign malicious updates and payloads and deploy them on targeted systems without being detected; furthermore, security experts state that the leak has an effect on the entire ecosystem.
MSI also warned users about fraudulent emails targeting the online gaming community under the guise of a potential collaboration.
Enhancing Security Measures with SOCRadar
Threat actors and Advanced Persistent Threat (APT) groups use various techniques and tools to accomplish their goals.
Monitoring and comprehending these adversaries’ actions is critical. It offers valuable insights into their current tactics, techniques, and procedures (TTPs) that may be more important than frequently altered Indicators of Compromise (IOCs).
SOCRadar notifies you about threat groups’ actions and enables you to establish use cases that more efficiently identify and thwart malicious activities.