
New Botnet Sale and Recruitment Post, US and Canada RDP Access Sale, Dymocks Database
In this week’s dark web update, the SOCRadar Dark Web Team has revealed a series of troubling developments; among their recent findings, databases from a Brazilian travel company and Dymocks have come to light.
Additionally, the team has uncovered an active sale of a new botnet, operational on a daily basis, and has detected a fresh recruitment post suggesting potential hacking activities. Unauthorized RDP access sales also continue to be a concern, and in this week’s dark web digest, the team has identified another sale offering such access to American and Canadian companies.
Let’s delve into the details of these critical findings and explore the evolving landscape of cyber threats on the dark web.
Find out if your data has been exposed.
Database of a Brazilian Travel Company is on Sale
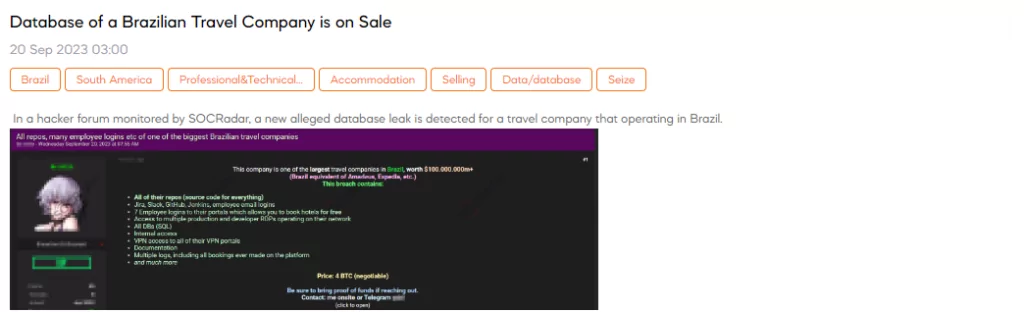
SOCRadar Dark Web Team detected a post that a threat actor claims to have access to a significant amount of sensitive data from a travel company operating in Brazil. The breach allegedly includes access to the company’s source code repositories, employee login information for various platforms (Jira, Slack, GitHub, Jenkins), access to employee portals allowing free hotel bookings, RDP (Remote Desktop Protocol) access to production and developer systems, all databases (SQL), internal network access, VPN access to VPN portals, documentation, booking logs, and more. The price for this data is 4 BTC (Bitcoin).
Unauthorized RDP Access Sales are Detected for American and Canadian Companies
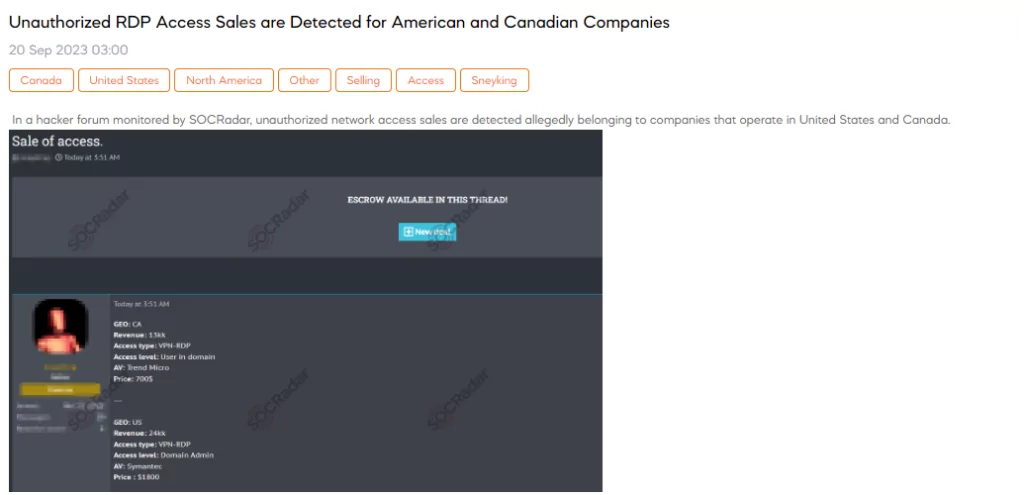
SOCRadar Dark Web Team uncovered a post in which a threat actor is advertising the sale of unauthorized network access to companies operating in the United States and Canada. This illicit offer outlines specific details for each target, including revenue figures, access methods (VPN-RDP), and the level of access within the network. The actor discloses the antivirus software in use by the targeted organizations and sets prices at $700 for the Canadian access and $1,800 for the American access.
New Botnet is on Sale
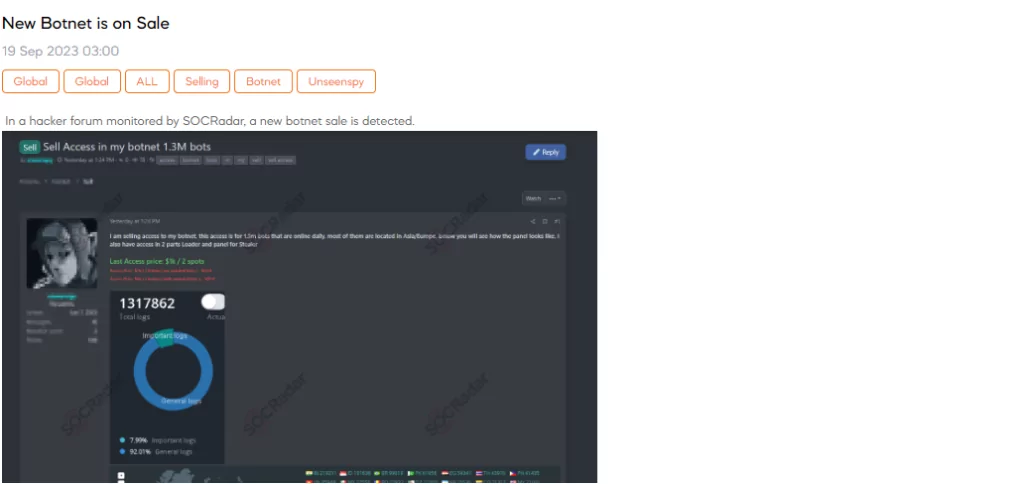
On 19 September, The SOCRadar Dark Web Team has detected a post in a hacker forum that a threat actor is claiming to be selling access to a botnet. This botnet allegedly consists of 1.3 million bots that are online daily, with a significant portion located in Asia and Europe.
New Recruitment Post is Detected
SOCRadar Dark Web Team has detected a post in a hacker forum where a threat actor is recruiting individuals who can provide databases of dietary supplements, banks, and Forex. This recruitment post is seeking employees with access to these databases, including those from call centers, teleshops, pharmacy chains, banks, and Forex institutions.
Customer Database of Dymocks is Leaked
SOCRadar Dark Web Team has uncovered a concerning post in a hacker forum, revealing an alleged data breach related to Dymocks, an Australian book retailer. This breach, dating back to June 2023 and disclosed by Dymocks in September 2023, reportedly exposed 1.2 million customer records, including 836,000 unique e-mail addresses, along with names, birthdates, genders, phone numbers, and physical addresses.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.



































