
The Week in Dark Web – 1 November 2021 – Ransomware Attacks and Data Leaks
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Again, rise of ransomware attacks, some database thefts, and stealing customer data, that took their place on the headlines this week. Click here to read the last weeks post.
Find out if your data has been exposed on the deep web.
Unauthorized Access Sale Detected For A University From Russia On The Dark Web
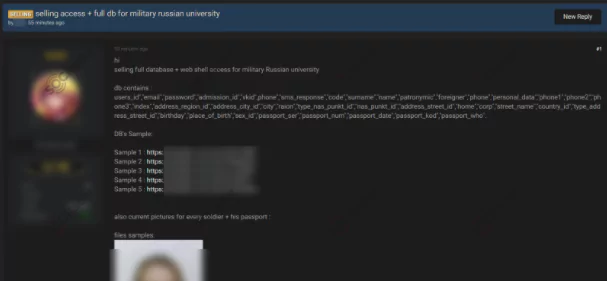
On October 27, on a dark web forum monitored by SOCRadar, a vendor attempted to sell unauthorized access allegedly for a military university from Russia. While the dark web vendor did not give the name of the university, it is stated that the buyer would have web shell access for the victim university and a database containing personally identifiable information (PII) belonging to the university’s students. According to the dark web post, the database comprised names, email addresses, phones, and pictures of the students’ passports.
The New Ransomware Victim of Conti
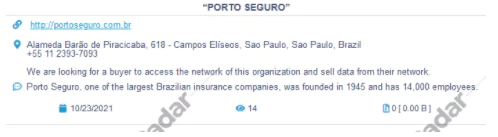
On October 23, SOCRadar detected a post allegedly announcing ransomware that targeted a firm from Brazil on the Conti groups’ website. Established in Sao Paolo, the victim corporation is engaged in finance and insurance with over $5 billion in revenue. The group behind the attack known as Conti is also responsible for last month’s ransomware attack on JVC Kenwood, a Japanese multinational electronics giant. If the victim organization would not cooperate with the ransomware group, the ransom gang threatened to leak banking data, licenses, certificates, agreements, contracts, and similar sensitive information belonging to the victim organization.
Customer Database of A Bank From Indonesia Leaked On The Dark Web
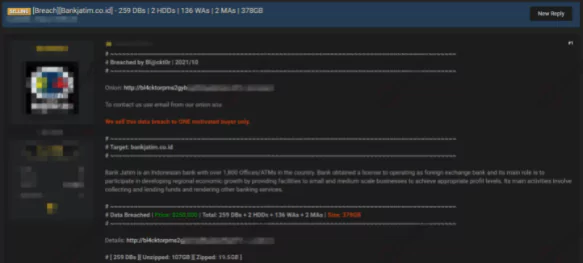
On October 20, a vendor claimed to have databases allegedly belonging to a bank from Indonesia on a dark web forum monitored by SOCRadar. The East Java-based victim bank has over $358 million with more than five thousand employees. According to the dark web post, breached databases and HDD data contain 378 GB of banking information. Also, the vendor wants $250 thousand for the databases.
The New Ransomware Victim Hit By The Groove Ransomware Gang
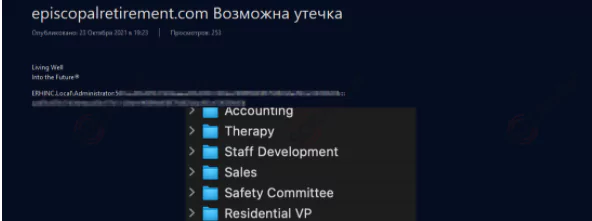
On October 19, SOCRadar found a post allegedly announcing a ransomware attack targeting a retirement services firm from the US on the Groove groups’ website. Established in 1951, the victim organization provides services for older adults living in their own homes with $7 million.
Database of Malaysian Doctors Leaked to Dark Web
On October 19, a vendor attempted to sell a database allegedly containing personally identifiable information (PII) belonging to Malaysian doctors on a dark web forum monitored by SOCRadar. The surfaced details include full names, emails, phone numbers, and organization names according to the sample. While it is not clear how the database was obtained, the dark web vendor stated that there is information of 1700 doctors in the database.
The New Ransomware Victim Hit By The LockBit 2.0 Ransomware Gang
On October 26, SOCRadar found a post allegedly announcing ransomware targeting a technology firm from France on the LockBits’ website. The victim organization is engaged in computer systems design with a revenue of $4.6 million.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































