The Week in Dark Web – 12 March 2021 – Zero-Day Exploits and Then Some
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Database sale of an Israeli company, 2M Indonesian citizens PII data leak, Cobalt Strike new edition on sale are some of them. Here are the details of the major events that took place on the deep web this week:
Database of a Leading Company From Israel on Sale
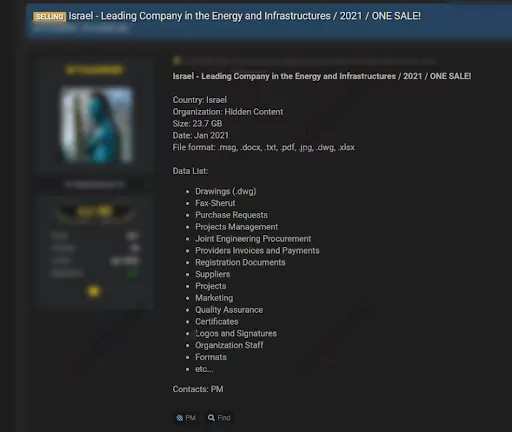
On March 8, 2021, on a dark web forum monitored by SOCRadar, the threat actor put for sale a database of a leading energy and infrastructure company from Israel. The threat actor allegedly had many different data that could pose a threat for the company, such as project management, invoices and payments, and signatures obtained in January 2021. According to the threat actor’s claim, the database included .msg, .pdf, .xlsx, .jpg and more different file formats.
PII (Personal Identifiable Information) Data of More Than 2 Million Citizens of Indonesia Leaked
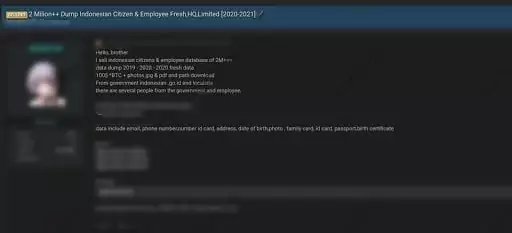
On March 10, 2021, the actor offered to sell a database of Indonesian citizens and employees on a dark web forum monitored by SOCRadar. According to the threat actor’s claim, the database, dumped from the Indonesian government website, contained over 2 million citizens’ and employees’ PII (Personal Identifiable Information) data like email, phone number, ID card, address, date of birth. The actor, claiming to have the database from the last three years, wanted to sell these PII data for $100 in BTC.
Zero-Day Exploits of QuickBook and Oracle Micros on Dark Web
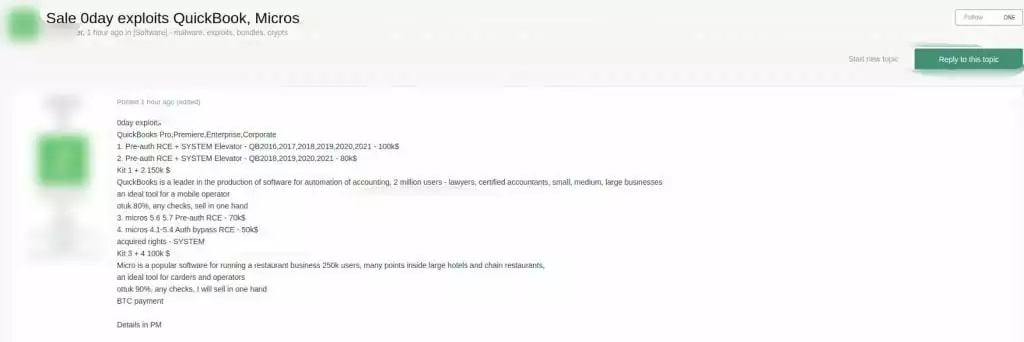
On March 11, 2021, the actor put four different 0day exploits allegedly belonging to QuickBook and Micros on a dark web forum monitored by SOCRadar. QuickBooks is an accounting software package developed and marketed by Intuit Inc., with $6.8 billion in revenue. QuickBooks products are mainly aimed at small and medium-sized businesses and are cloud-based platforms accepting in-house accounting applications and business payments, manages and pays invoices, and also payroll functions. The threat actor claimed to have two different zero-day pre-auth remote code execution vulnerabilities affecting QuickBooks and offered these vulnerabilities for $100K and $80K. Micros, working internationally with more than 5000 employees and a subsidiary of Oracle, produces software and services for restaurant sales points, hotels, hospitality and has a revenue of over $1 billion. The actor had assertedly zero-day Pre-auth remote code execution vulnerability and zero-day Bypass Authentication remote code execution vulnerability affecting Micros and also offered these vulnerabilities for $70K and $50K.
New Edition of a Command and Control Software Cobalt Strike on Sale
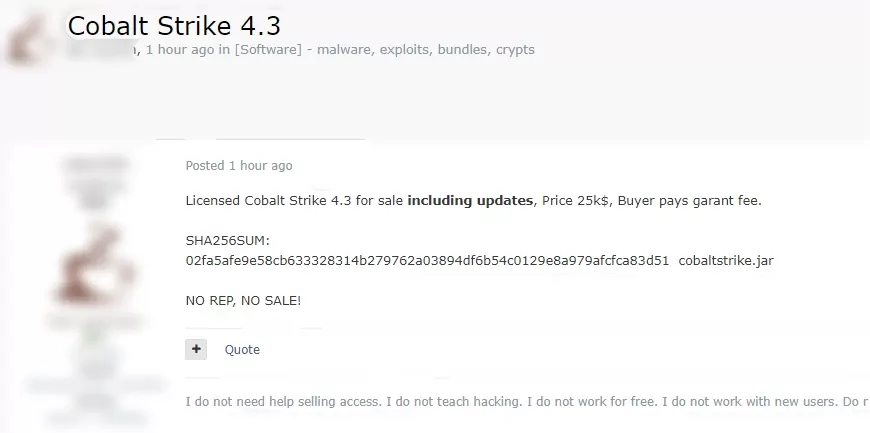
On March 9, 2021, the actor attempted to sell the license for new edition of Cobalt Strike, a software for Adversary Simulations and Red Team Operations, on a dark web forum monitored by SOCRadar. Cobalt Strike has been developed for ethical hackers, but like many other offensive cybersecurity tools, it has fallen into the wrong hands. Notorious APT Groups are known to have used Cobalt Strike including APT29 (Cozy Bear), Magic Hound, and Winnti which is one of the APTs known to be using recent Microsoft Exchange vulnerabilities to compromise email servers all around the world. The actor put the updated version of Cobalt Strike on sale for $25k and wanted to take guarantee fee.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.