
The Week in Dark Web – 14 December 2022 – Access Sales and Leaks
Powered by DarkMirror™
Just a few weeks remain to close 2022. We are all in the mood for the holiday season, but it seems threat actors continue their efforts on the dark web.
Here’s the quick wrap-up of the last week’s headlines from the dark side.
Find out if your data has been exposed on the deep web.
Unauthorized Access Sale for Iran Airlines
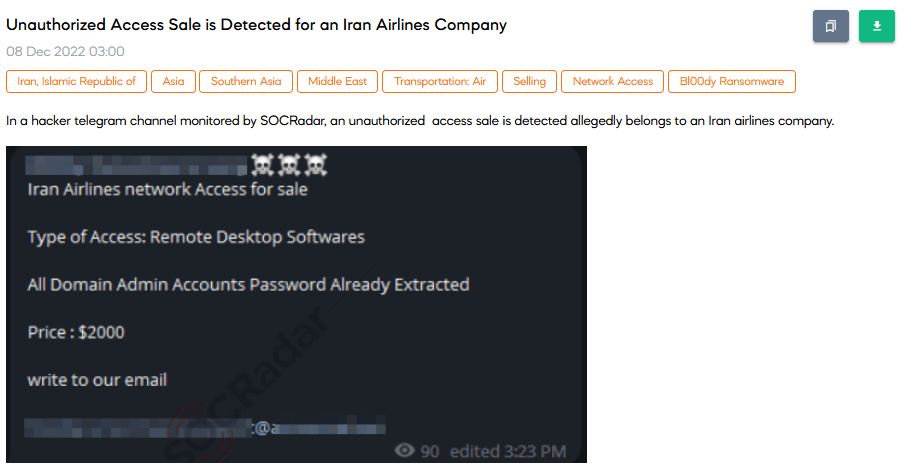
On 8 December SOCRadar Dark Web team found a Telegram post about unauthorized admin access to Iran Airlines’ network. The responsible group’s account shares the post and directly leads possible buyers to their e-mail address which is rare compared to Telegram DM and TOX messages. The price of access is $2000.
Source Code of S500 RAT for Sale
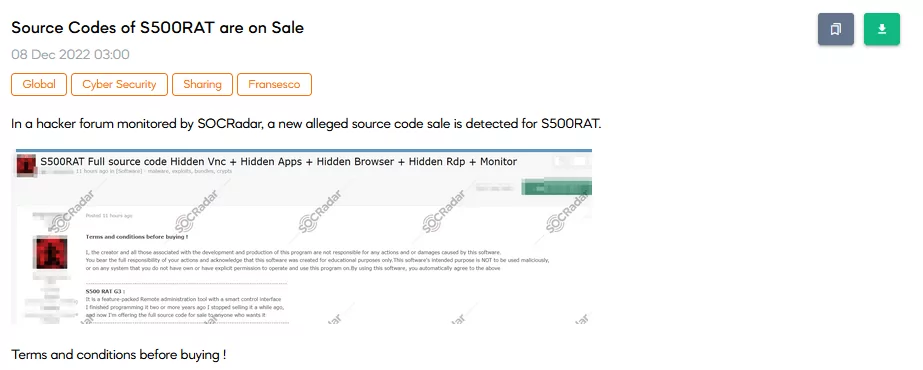
SOCRadar has found a source code sale related to S500 Remote Access Tool (RAT). A threat actor shared a service sale post about the same RAT the previous week. The vendor, allegedly the creator of the RAT, states that they decided to sell complete source code instead of giving it as a service. The vendor also refuses to take responsibility for the RAT after the sale.
Information of Russian Military Personnel for Sale
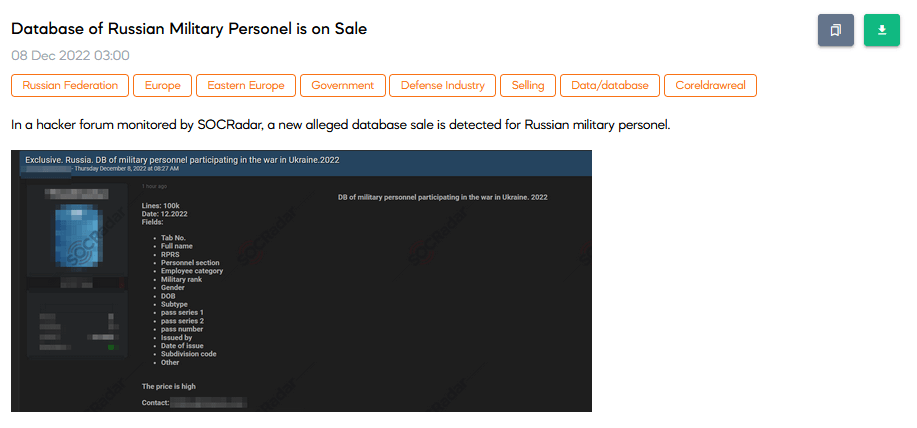
SOCRadar Dark Web Team has found a hacker forum post that sells personally identifiable information about Russian Military Personnel Operating in Ukraine War. The database includes 100 thousand lines of information. Instead of naming a price, the vendor states that the price is high.
Database Sale of an Asian Virtual Card Service
SOCRadar Dark Web Researchers found a sales post that offers a database of a Virtual Card Service that operates globally. According to the post, the database includes highly valuable banking information such as 40+ million payment cards, 65+ million virtual cards, transactions, and balances. The price of the database sale is $185.000.
Database of Iranian Nuclear Program is Leaked
On 6 December, a vast Iranian nuclear program database leaked via a forum post. The database contains 50GB of information. The leak originates from a data breach that occurred on 23 October. The vendor states that the group responsible for the breach, Black Reward, shares the data since the Iranian Government has not responded to their terms related to political prisoners and arrests in recent protests.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.




































