
The Week in Dark Web – 17 January 2022 – Access Sales and Data Leaks
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Again, rise of ransomware attacks, some database thefts, and stealing customer data, that took their place on the headlines this week. Click here to read the last weeks post.
Find out if your data has been exposed on the deep web.
Unauthorized Webmail Access Sale Detected For An Insurance Firm from Colombia On The Dark Web
On January 13, a dark web vendor attempted to sell unauthorized webmail access for an insurance and financial firm on a dark web forum monitored by SOCRadar. According to the dark web post, the buyer would have access to 315 GB of email files and over 300 thousand messages as well as Gmail access. Headquartered in Bogotá, the victim company is engaged in insurance, construction, health, and real estate services. The vendor also shared a screenshot as PoC.
Database of Canada-Saskatoon City Airport Publised On The Dark Web
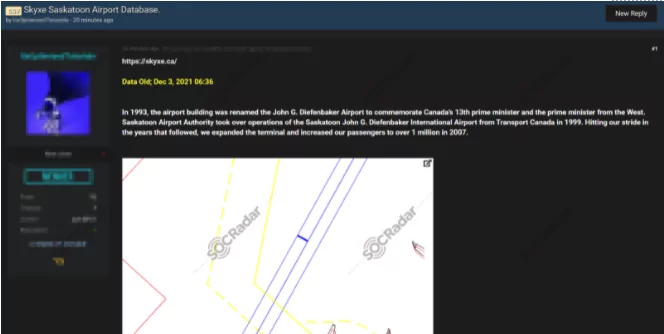
On January 5, SOCRadar detected a post allegedly publishing a stolen database of Skyxe Saskatoon Airport. The vendor shared samples demonstrating the content of the database. According to the underground market post and samples, there are documents including airport plans, financial sheets, and sensitive contracts in the shared database. The vendor also stated that the database was obtained on December 3, 2021, and is up to date.
Unauthorised Shell Access For An E-Commerce Company from Spain Put On Sale

On January 14, a vendor offered to sell unauthorised shell accesses allegedly for a Spanish e-commerce company on a Russian-speaking underground forum tracked by SOCRadar. While the dark web vendor did not detail how this access has been seized, it is stated that 70% of the payments are credit cards and 20% of those are PayPal. The vendor also set a starting price $200 for the auction.
An Investment Company from Switzerland Crippled by Cuba Ransomware
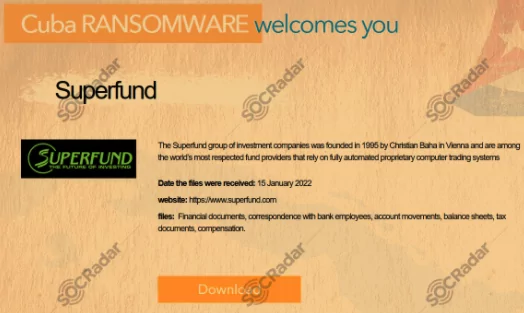
On January 13, a ransomware post allegedly announcing an attack that targeted the media giant of Portugal was detected in the Lapsus$ ransomware group telegram channel monitored by SOCRadar. Established in Lisbon, the victim group has a TV channel, a newspaper and various magazines with a revenue of $196 million. The ransomware group could leak all their data if the victim organisation refuses to negotiate.
Lapsus$ Group made its debut on the ransomware scene in 2021. It became famous with the Brazil Ministry of Health attack last month.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































