
The Week in Dark Web – 18 January 2023 – Partnership Posts, Data Leaks, and Requests
Powered by DarkMirror™
Threat actors seek to acquire new capabilities by forming partnerships with their peers to ensure continuity in cybercrime operations. By adding a new member to the team, they can both expand their network and launch more effective attacks. Dark web forums and Telegram channels are their preferred medium for doing this.
Last week, we observed a “job posting” of cybercriminals operating in cryptocurrency fraud. This posting, which even states the “qualifications” sought in the candidate, clearly indicates that the threat actors are part of serious criminal networks, not just a few marauding hackers.
Here’s a brief summary of what happened on the dark web last week.
Find out if your data has been exposed on the deep web.
Data Request Post for Bulgarian Entities Detected
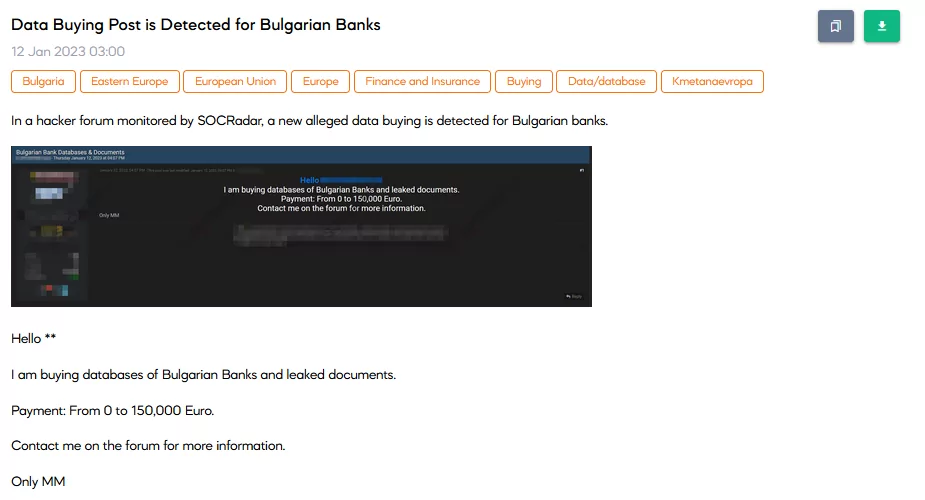
On 12 January, SOCRadar Dark Web Team detected multiple posts targeting Bulgarian entities. All the posts are shared in the same forum and have a similar outline. In this example, one can see that data concerning Bulgarian banks can be bought for a price of up to $150,000, according to the quality of the data. Similarly, posts targeted Bulgarian ministries for Finance, Defense, Science & Education on the same day.
New Partnership Post is Detected
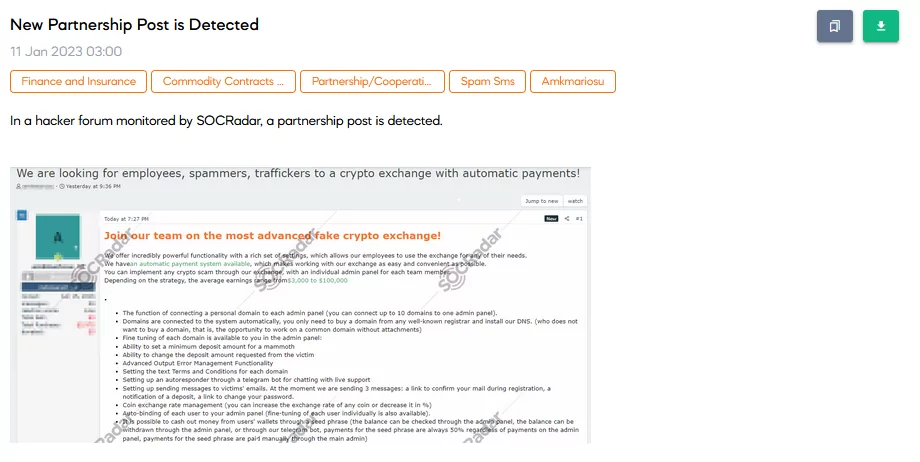
On 11 January, SOCRadar detected a new partnership post on a hacker forum. The post clarifies the expectations for the possible candidate along with its responsibilities. Considering the post, it can be said that the team behind this post is making money by attracting people to fake cryptocurrency exchanges. It is announced in the post that the members can earn between $3000 to $100,000
New RAT is Shared
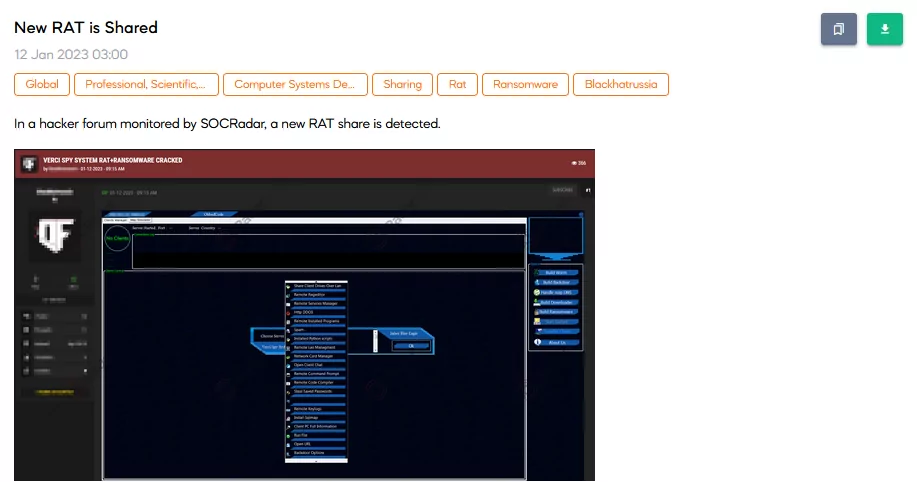
On 12 January, Verci Remote Access Tool (RAT) post was detected by SOCRadar. It is claimed that the RAT is a cracked full version. However, the post owner states that it may still contain backdoors from the developers, yet they are trying to improve the crack.
Database of French Citizens for Sale
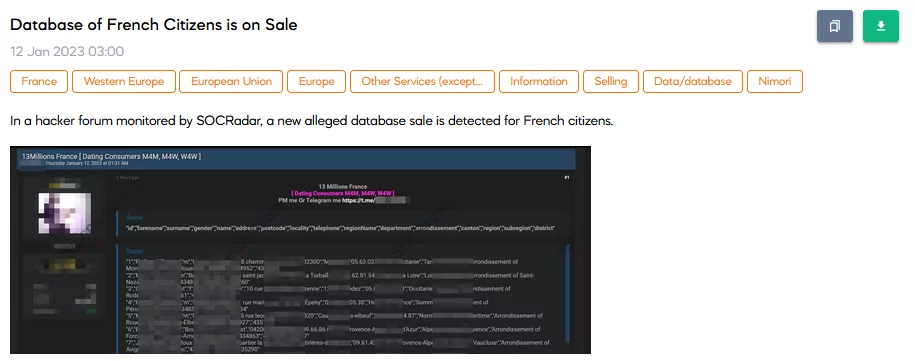
On 12 January, a SOCRadar dark web researcher detected a post selling a French Citizens database. The database contains more than $13 million lines of information, mostly personally identifiable information (PPI) of the French Citizens’. The information’s price is not known; the threat actor directs people to DM.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.




































