
The Week in Dark Web – 19 March 2021 – US Law Firms On Target
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Unauthorized network access sale for Tata Communication and law firms from the US, Binance API keys database leaked, customer database of IDC games shared for free, Ecuadorian Citizens’ Information on the darknet. Here are the details of the major events that took place on the deep web this week:
Unauthorized Network Access for the Telecommunication Giant TATA On Sale

On March 15, 2021, on a dark web forum monitored by SOCRadar, an unauthorized network access sale was detected for Tata Communications. Tata Communications is one of the world’s leading telecommunication companies with a revenue of more than $ 2.34 billion. The company, with over 12000 employees, has giant customers like Microsoft, Oracle, and IBM; also, the threat actor, who wanted $18k in BTC for the access, emphasized that the buyer would have access to the web servers, internal networks, and databases of Tata and its customers. According to the SOCRadar Analyst, these databases, which may include confidential data belonging to the organization or customers, can be leaked and pose serious threats to brand reputation.
Database including 160 Binance API Keys On Sale

Threat actors can hack into many blockchain and cryptocurrency-related technologies for stealing funds. On March 15, 2021, a threat actor attempted to sell a database containing API keys of Binance on a dark web forum monitored by SOCRadar. Binance is one of the world’s largest cryptocurrency exchanges and according to the threat actor’s claim, the database comprises keys of 160 API whose balances corresponded to $637000 on March 14, 2021. Also, the actor asserted that he tried to withdraw but could not find the correct method to get coins. Therefore, he offered to sell keys for %15 of the total balance, which corresponded to $95550.
Customer Database of IDC Games Shared for Free on a Dark Web Forum
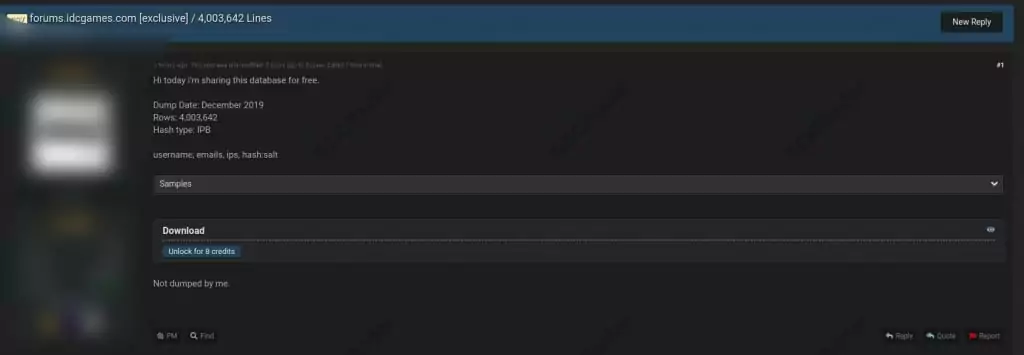
On March 15, 2021, on a dark web forum monitored by SOCRadar, a threat actor shared a database of IDC games for free. The actor claimed that the database, dumped in December 2019, contained 4 million customers’ emails, usernames and IP addresses. Further, the actor shared a sample, and passwords are visible in IPB (Invision Power Board) hashed format. SOCRadar Analyst states that if the hashed passwords are cracked and hackers obtain the credentials of 4 million users, this can lead to new exploits for different companies, whose employees are users of IDC Games.
** https://socradar.io/solutions/credentials-and-data-leak-detection/
Ecuadorian Citizens’ All Information Leaked on Dark Web
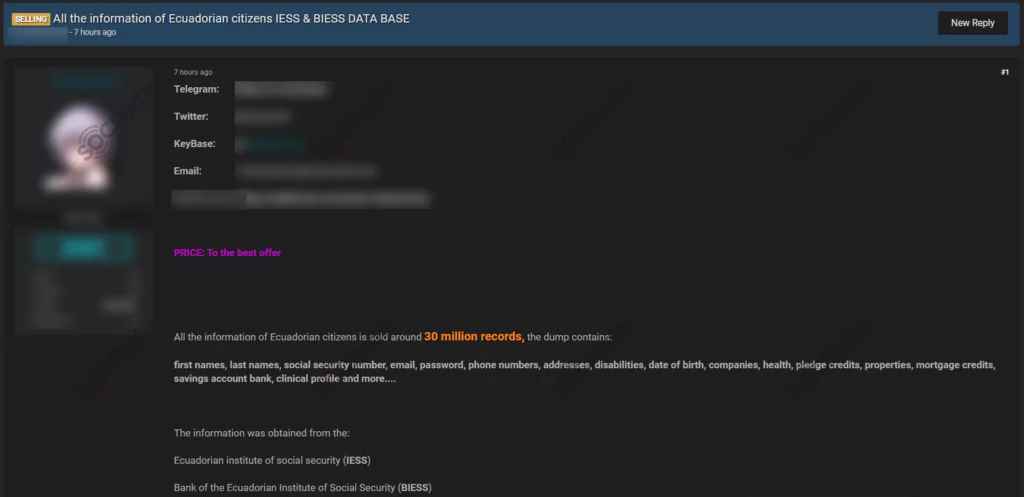
On March 15, 2021, a threat actor offered to sell a database allegedly including Ecuadorian citizens’ information on a dark web forum monitored by SOCRadar. According to the actor, claiming to obtain the database from the Ecuadorian Institute of Social Security (IESS) and Bank of the Ecuadorian Institute of Social Security (BIESS), the database covered all data of 30 million people, from general information like full name, social security number and emails; to detailed information such as clinical profile and mortgage credits. By seizing this Personally Identifiable Information (PII) -or here it can be Sensitive Personally Identifiable Information (SPII)- hackers can get the victims’ digital footprint and use it for fraudulent activities like spending money on credit cards or draining bank accounts. Furthermore, they can use the compromised PII for social media scams to gain additional PII and complete different cyber-attacks.
Unauthorized Network Access Sales Detected for Law Firms in the US
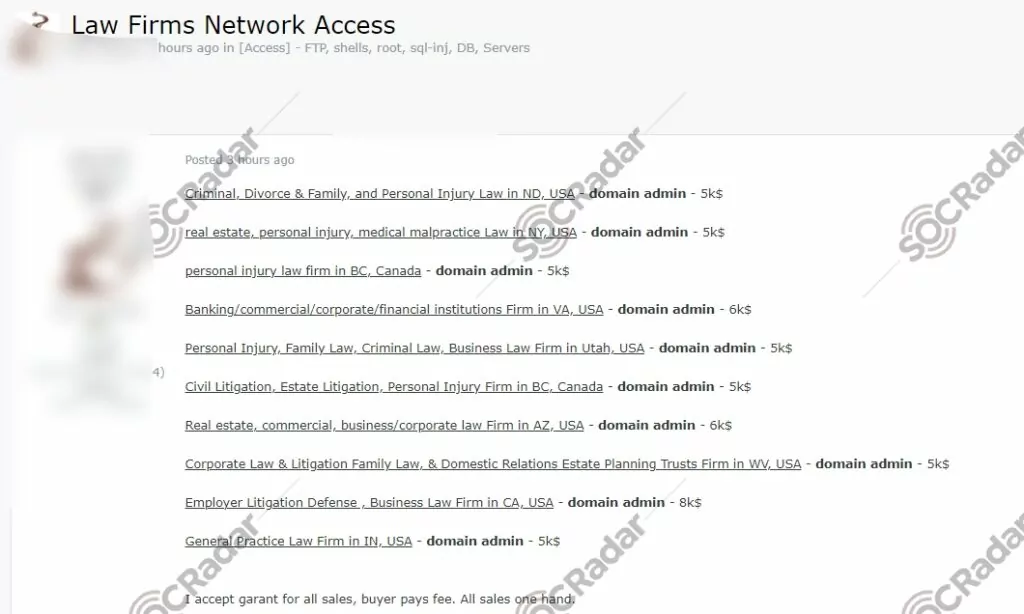
Nowadays, hackers are commonly trading network access to the organizations’ networks. With unauthorized network access, threat actors can to reach out to companies’ all data or leak sensitive information about the organizations like customer databases containing PII (personally identifiable information). On March 16, 2021, on a dark web forum monitored by SOCRadar, a threat actor put unauthorized network accesses belonging to American law firms on sale. The actor attempted to sell network accesses for asserted 10 law firms from 10 different states from the U.S. While some of these firms were Commercial litigation companies, some were law firms dealing with Divorce & Family cases. According to the actor’s claim, all network accesses are in the domain admin level, which means the buyer could edit information in Active Directory and access all data belonging to the firms.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































