
The Week in Dark Web – 21 March 2022 – Ransomware Attacks and Data Leaks
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Again, rise of ransomware attacks, some database thefts, and stealing customer data, that took their place on the headlines this week. Click here to read the last weeks post.
Find out if your data has been exposed on the deep web.
More Than 1,400 Access Sales
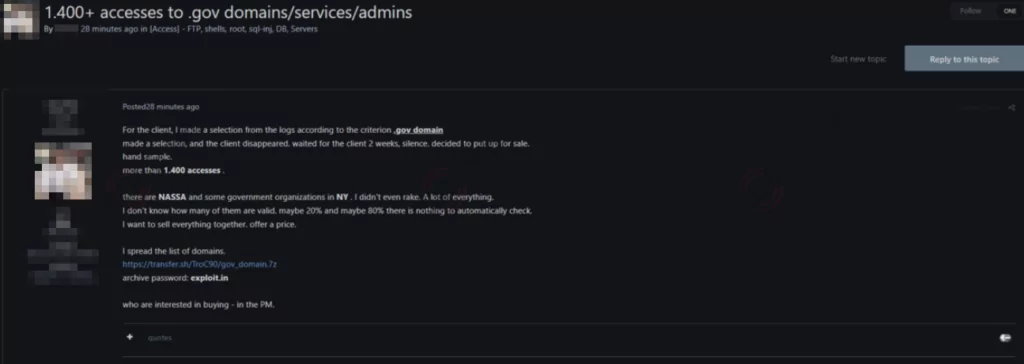
On March 17, a vast database of “.gov” domains, services, and admins puts on sale on the dark web. To vendor’s allegedly, this database includes more than 1,400 accesses belonging to NASA and NY government organizations. That is not clear that all of these data are valid to operate; no tool automatically checks all the data. In the dark web, vendor intends to sell all data together without a selection. While there is no accurate information about the stored data, according to SOCRadar analysts, with this database, ransomware groups could reach the data in other platforms on the internet as well.
Unauthorized Citrix Access
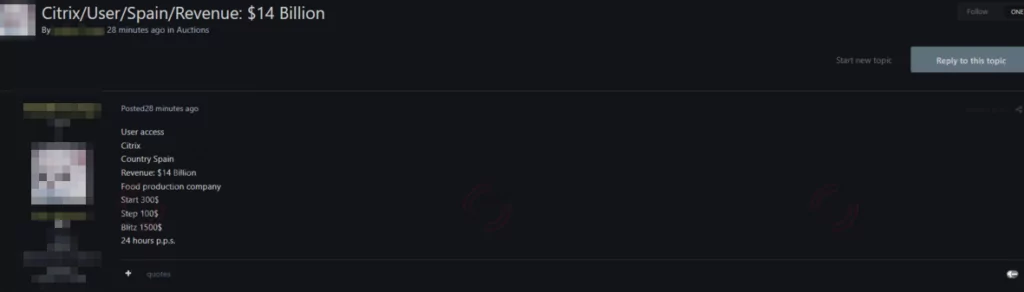
On March 17, a huge database of user access of a company was put up for auction on the dark web. The Spain-based victim company is related to food production, whose revenue is in the ballpark of $14 Billion. This leakage also includes their user accesses, which are on sale, to a workspace and cloud service based in the USA. Having had all the user access data, the ransomware group could reach all the information secured in the cloud as well as their database in the victim company. SOCRadar analysts state that if the victim company does not pay attention to the leakage, with the workers’ user accesses, the ransomware group could reach the data in other platforms on the internet as well, also using the cloud access which is leaked either.
Database Was Put Up For Sale on the Dark Web
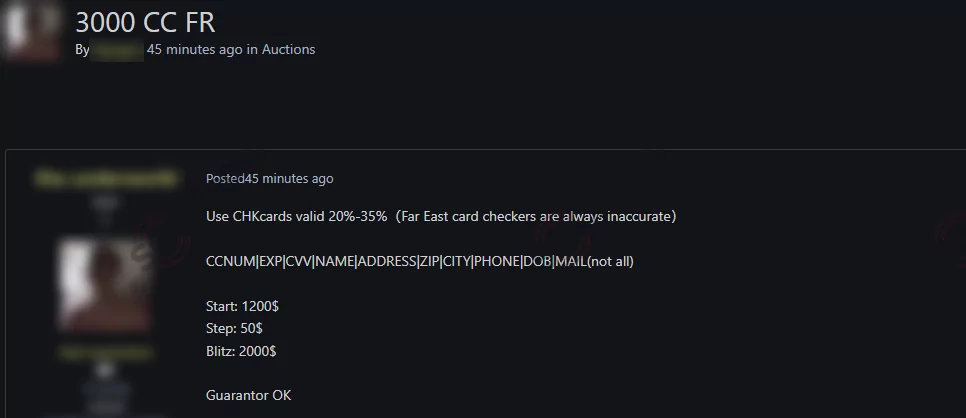
On March 17, a massive database was put up for sale on the dark web. To vendor’s allegedly, this database includes various CHK cards from the Far East, but only twenty-thirty percent of them are valid. Card zip codes, exp dates, and even CVV numbers of these cards are on sale on the dark web. Also, this database includes names, addresses, phones, and emails of card owners. This vast database is on auction with starting 1,200 dollars. SOCRadar analysts state that if nobody attends to solve this leakage, this situation can result in massive fraud.
LockBit Ransomware Groups’ Newest Victim
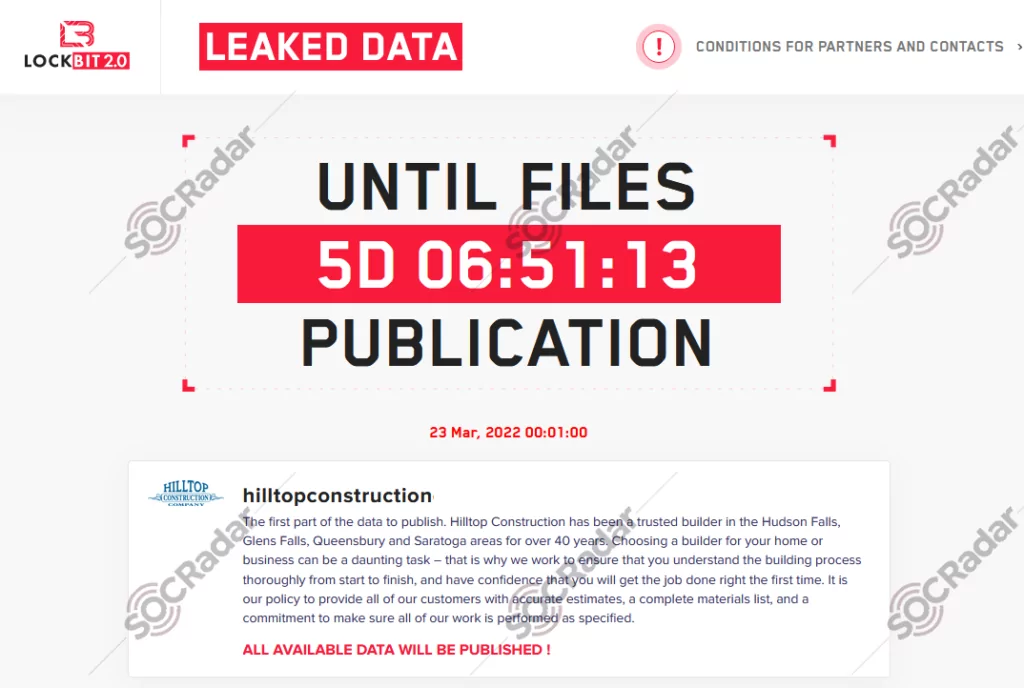
On March 17, a huge database of users of a company was put up for sale on the dark web. The victim company is a construction company that has been known as a trusted builder in Hudson Falls, Glens Falls, Queensbury and Saratoga for over 40 years. The ransomware group responsible, LockBit, which has taken credit for several high-profile attacks over the past months, including very well-known IT companies, state that all this available database will be published within a week. According to SOCRadar analysts, this leakage could result in more damage than expected. With the leaked database of the workers, the ransomware group probably could be able to reach their accounts in different platforms.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































