
The Week in Dark Web – 26 March 2021 – Grand Theft Data
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Citrix access sale, personal data sale from various organizations in tech, education, sourcing, and intrusion detection system sale for hackers were noted events that took place Here are the details of the major events that took place on the deep web this week:
Citrix Accesses On Sale

Nowadays, the Dark Web marks an increase in selling access to corporate networks. SOCRadar Analyst Team states these sales provide threat actors with the information required to hack into networks to infect critical machines with malware. On March 21, 2021, a dark web vendor attempted to sell Citrix accesses on a hacker forum monitored by SOCRadar. Citrix is a gateway with customers worldwide, providing companies with continuous remote access to their applications. The vendor asserted that there are companies having revenue of millions of dollars, and offered to sell Citrix accesses starting from $300 and emphasized a forum guarantor.
A Chinese Intrusion Detection System for Hackers On Sale
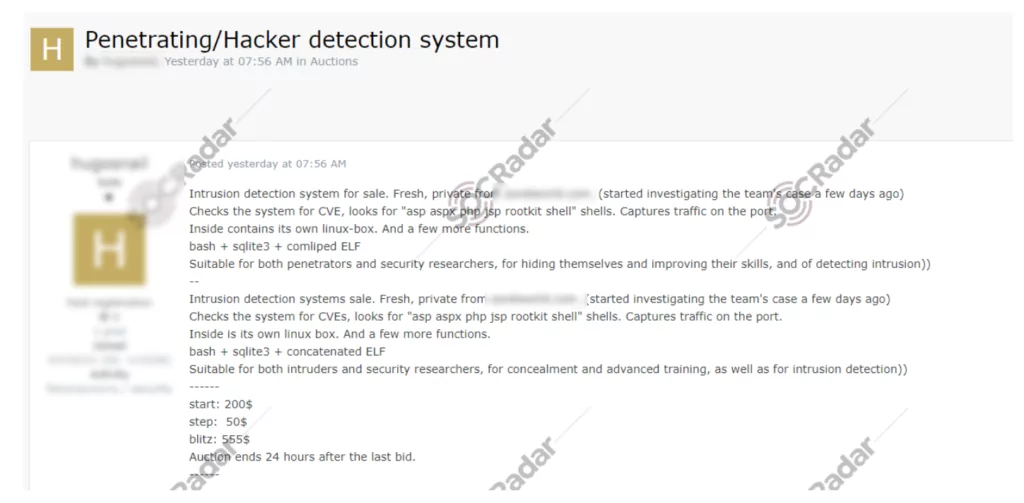
On March 24, 2021, on a dark web forum monitored by SOCRadar, a vendor offered to sell Intrusion Detection System (IDS) from Zorelworld, a Chinese network security company. Intrusion Detection System (IDS) is a software product that is used to monitor malicious activity or policy violations against networks or systems and the vendor claimed to have an IDS capable of checking the system for CVE, looking for asp, aspx, php, jsp rootkit shells. According to the vendor’s claim, the platform was suitable for both penetrators and security researchers, for hiding themselves and improving their skills.
Customer Database with 1.5 Million Users of a Job Search Engine Application On Sale

On March 23, 2021, on a dark web forum monitored by SOCRadar, a customer database sale was detected for Tanqeeb, Middle East’s leading job search engine application. Tanqeeb, with a revenue of over $17 million, provides people job opportunities from many websites, newspapers and internal jobs of different MENA and Gulf Countries like Saudi Arabia, Bahrain, Qatar. The vendor claimed the database includes 1.5 million user records and to be up-to-date.
Credentials of the Saudi Electronic University Website For Sale On Dark Web
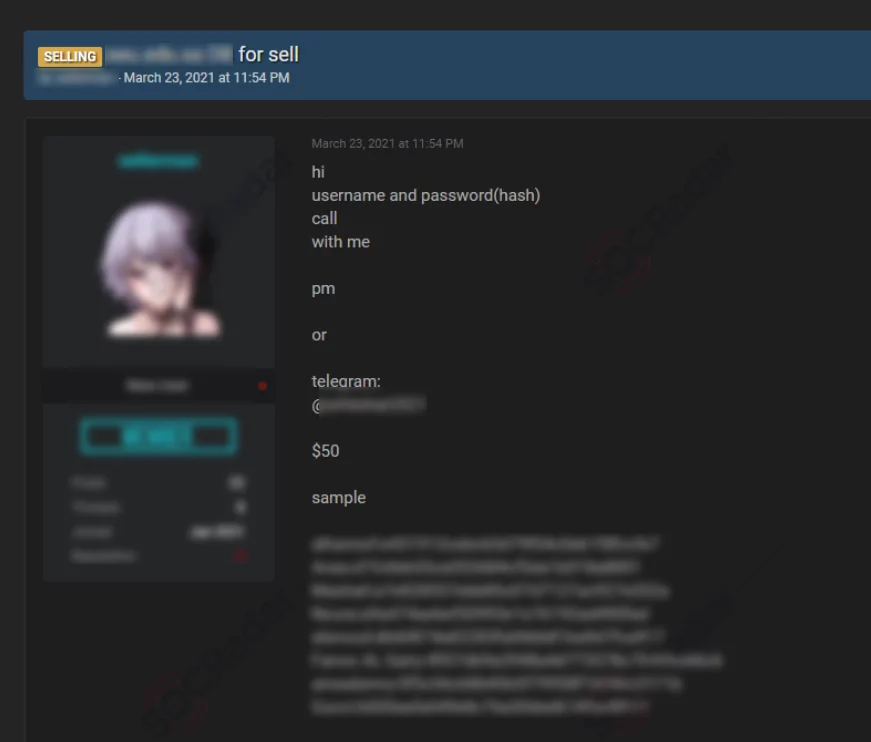
On March 23, 2021, on a dark web forum monitored by SOCRadar, a credential database allegedly belonging to Saudi Electronic University was leaked. Saudi Electronic University is a state-owned Saudi Arabian university that offers both undergraduate and postgraduate degrees with 10000 students. The vendor claimed to have the database containing usernames and passwords of the users of the University’s official website and also shared a sample showing the usernames and passwords in hashed formats.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































