
The Week in Dark Web – 4 January 2023 – Access Sales, Data, and Malware Leakes
Powered by DarkMirror™
Entering the first week of the year, the most sensational incident on the dark web was the sale of 30M customer data allegedly belonging to Indian Railways. Again, LockBit did not sit still and added another name to its victim list.
Here’s a rundown of what’s been happening on the dark web over the past week.
Find out if your data has been exposed on the deep web.
Database of Indian Railways Customers for Sale
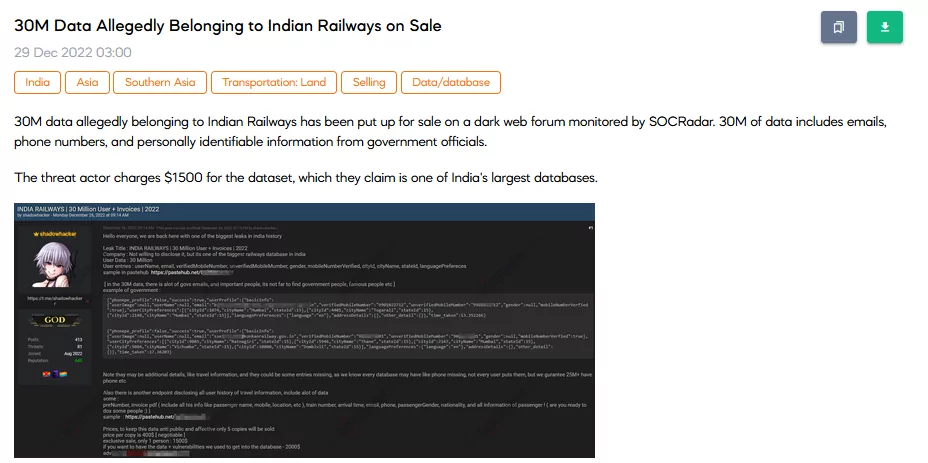
On 29 December SOCRadar Dark Web Team noticed a database sale of Indian Railways customers on a hacker forum. In the sale post, the threat actor highlighted that the database allegedly belonging to the Indian Railways has more than 30 million customers’ personally identifiable information. Furthermore, the vendor claims that government officials’ data is also in the database. The price tag for the database is $1500. Yet, the vendor also calls another sale option that combines the database and unauthorized network access for $2000.
Ransomware Attack: Port of Lisbon
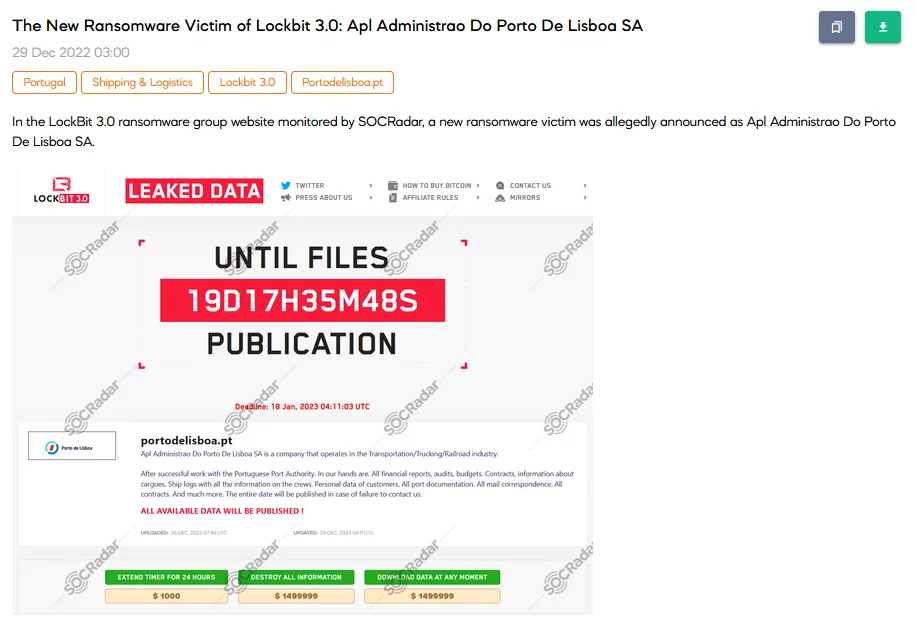
On 29 December, SOCRadar detected a new ransomware announcement that the Port of Lisbon, Portugal, had been attacked by the LockBit 3.0. The announcement highlights that the attack occurred in cooperation with an authority in the port. Furthermore, all financial reports, audits, budgets, contracts, information about cargoes, ship logs with all the information on the crews, and personally identifiable information of customers are obtained with the attack. The ransom is $1.5 million.
Unauthorized Webshell Access Sale for Multiple Governments
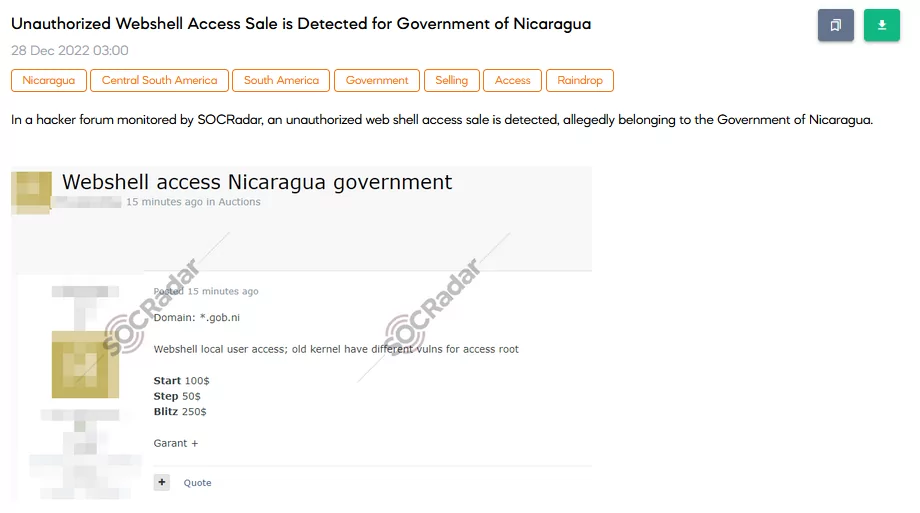
On 28 December, SOCRadar Dark Web researchers found multiple unauthorized webshell access sales belonging to three different governments. These governments are Nicaragua, Ghana, and Peru. Each access is shared identically with the same explanations and the same auction values.
Passport Information of Russian Citizens Leaked
On 27 December, the SOCRadar Dark Web team found a post that shared passport scans of Russian citizens on a hacker forum. In the post, four thousand passports are exposed to the forum users.
A New Brute Force Tool is Shared
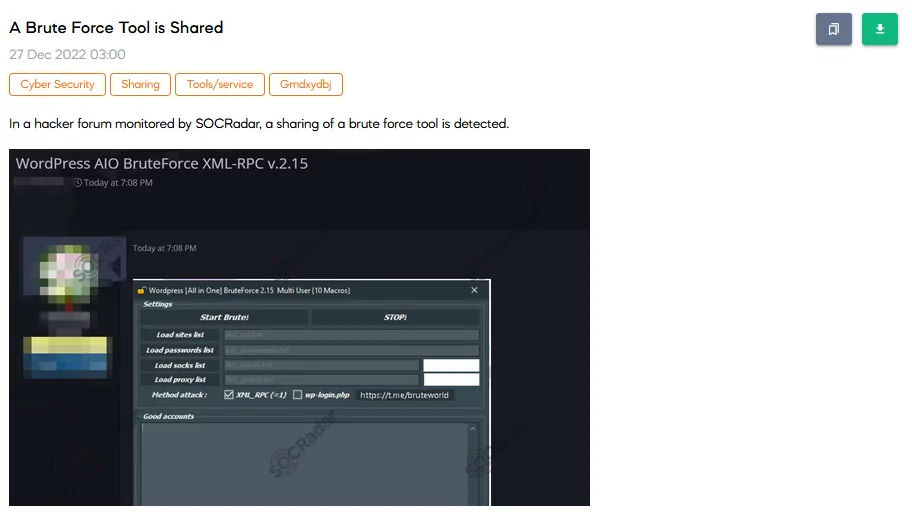
On 27 December, SOCRadar Dark Web Researchers detected a brute force tool. These kinds of tools are used for compromising passwords using the computation power of computers.
XWorm RAT v2.3 Has Been Leaked
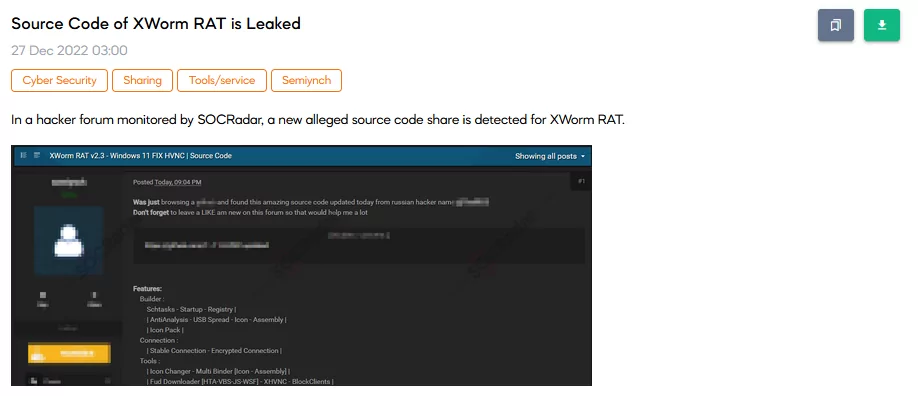
On 27 December, the SOCRadar Dark Web team detected a source code leak belonging to XWorm Remote Access Tool (RAT). The post states that another user shares the source code in a Russian hacker forum. Yet the post owner mirrors the RAT to improve their reputation.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.




































