
Timeline: The Russian – Ukranian Cyber Space Wars
February 13: A file matching the DDoS attack IoCs was uploaded to VirusTotal.
February 15 & 16: Some Ukrainian websites were not accessible due to heavy DDoS attacks. Both UK and US officials have attributed these attacks to a known Russian GRU infrastructure stating The US has technical data to back it up. During attacks, it is reported that some customers could not access the banking websites and, in minimal cases, ATMs became unavailable too. In addition to these attacks, some fraudulent SMS messages were sent to Ukrainian phones, possibly creating panic. The source of these attacks was a Mirai botnet. Researchers matched the gathered IOCs to a botnet named Katana, which is, in fact, a variant of Mirai with improved DDoS capabilities. Katana source code is available for purchase for less than a thousand dollars, and it is possibly shared for free on some deep and dark websites.
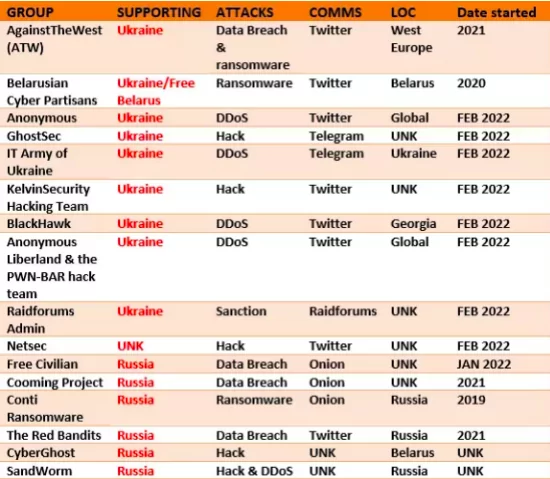
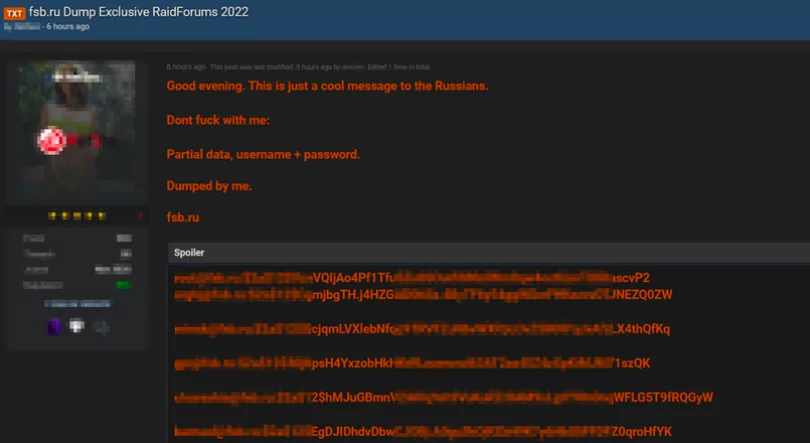
From February 20 to March 1: The cyberspace’s “underworld” dark has actively agreed to join the Russian – Ukrainian War as many different cyber threat actors continue their operations on the web. Hacktivists have announced that they supported one of the parties who fought many threats, from groups to ransomware gangs.
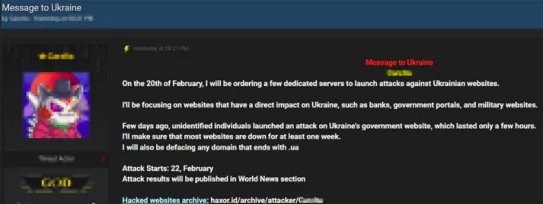
February 20: Before starting the Russian – Ukrainian War, the RAID forum announced that the DDoS attack on the Ukraine websites would be launched on February 20.
February 23: U.S. and UK agencies have detailed what they claim is another malware tool used by Russian APT hacking group Sandworm.
February 24: A call for help was announced for attacks by the Belarusian Cyber-partisan group has also been among the hacker groups that are taking sides with Ukraine.

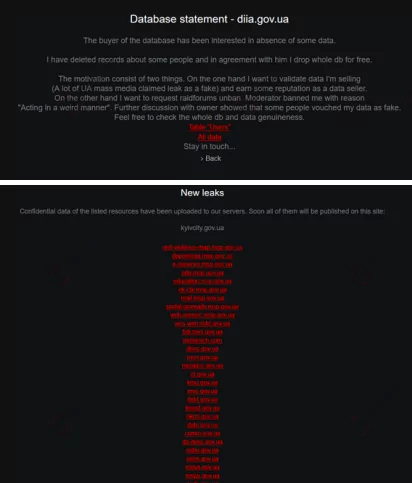
February 24: The group Free Civilian, known for its attacks against Ukraine, identified itself as cyber warfare when the actual war began and published several sensitive data from the Ukrainian state.
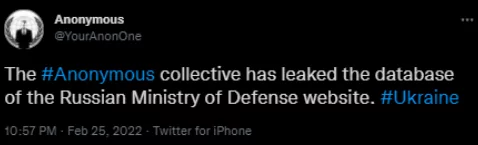
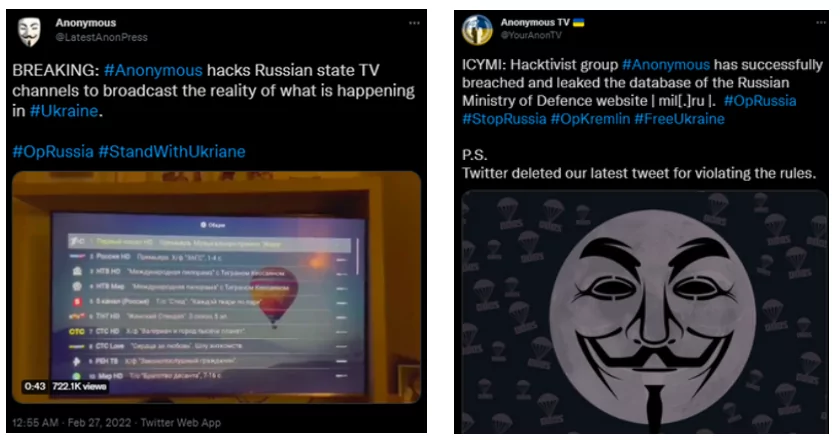
February 25: International Hacker Group Anonymous declared a cyberwar on Russia over its attack on Ukraine. Anonymous will publish what has been hidden for years and threaten that this information will be a devastating blow to Putin and his “corrupt murtads.”
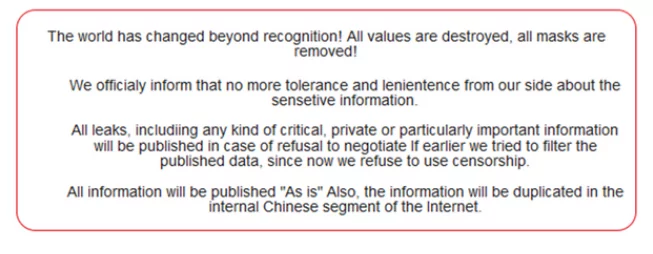
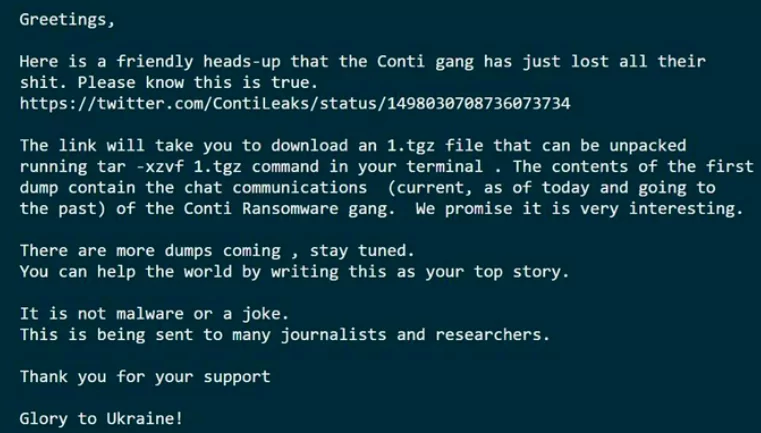
February 25: The Conti ransomware group, which talked about itself through the ransomware attacks, said Anonymous was next to Russia by announcing its statement targeting Russia.
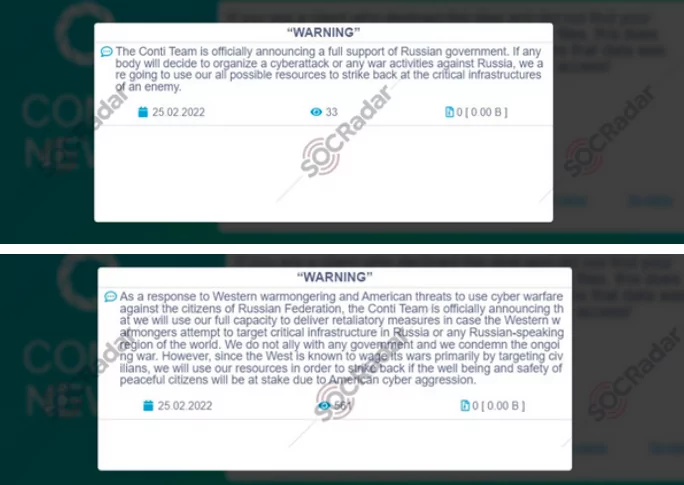
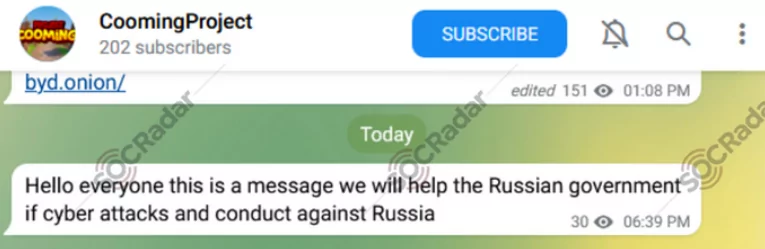
February 25: Meanwhile, The Cooming Project Group, which has been selling/sharing data from critical institutions since 2021 in Russian-speaking hacker forums, has also been among the hacker groups next to Russia.
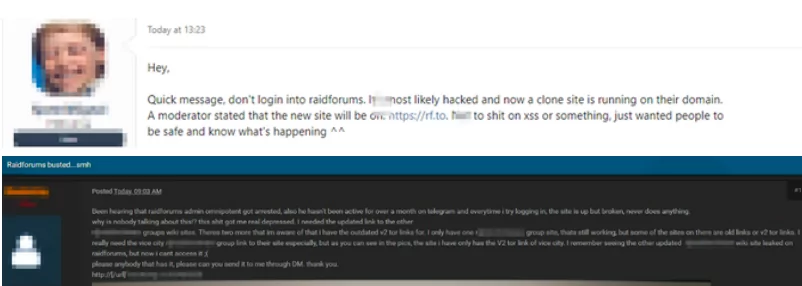
February 25: Many posts related to this issue were detailed due to increased Ukrainian data in the forum. Access to the forum was immediately turned off, and the access shortage is still in progress.
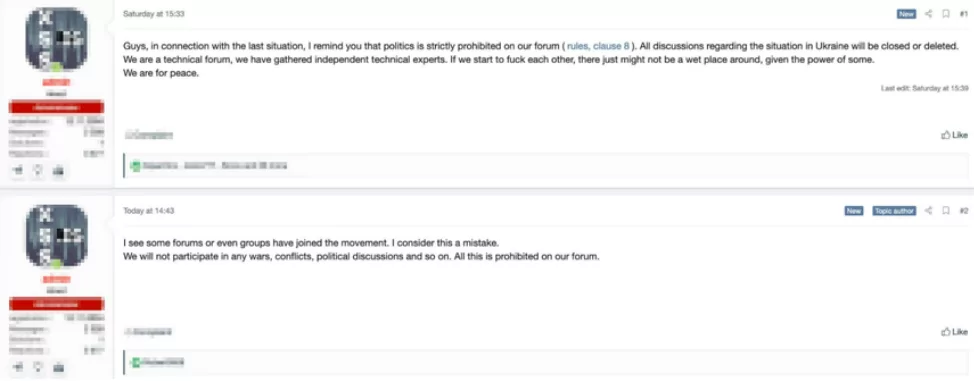
February 26: The XSS forum has made a statement about specifying the side, “We are for peace,” “We will not participate in any wars, conflicts, political discussions and soon. All this is prohibited on our forum.”
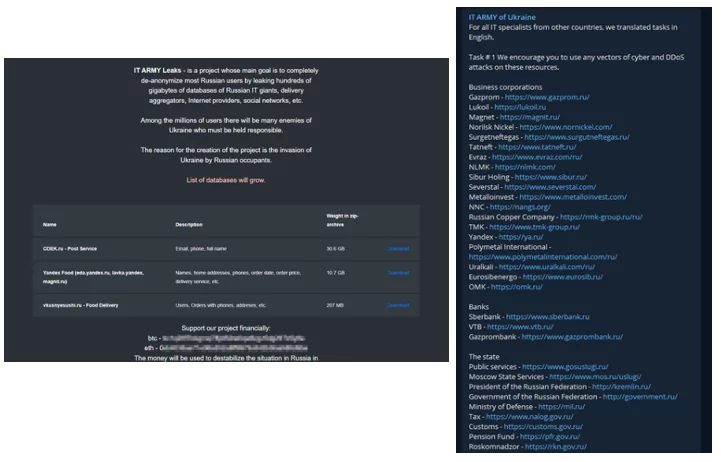
February 26: IT Army of shared sensitive data of Russian Federation on their blog, shortly after requesting assistance for DDoS attack on Ukrainian – state website, has also been among the hacker groups next to Ukraine.
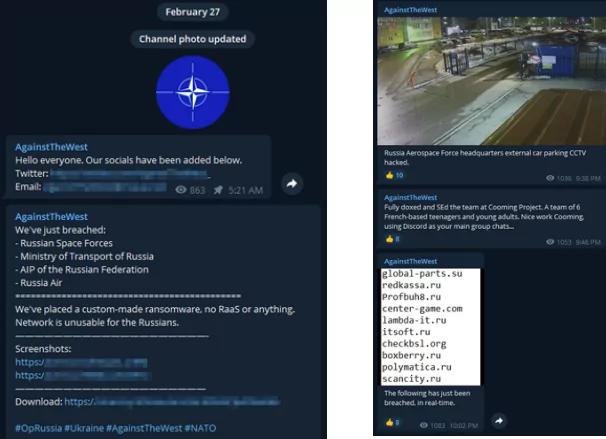
February 27: Against The West (AWS) group said that various Russian state institutions had ransomware infect their systems that there had been an attack with data – destroying malware and data interception. The group explained that the Russian Air Force Command hacked the CCTV camera and shared a camera screenshot.
February 27: Snatch group, after the Ukrainian attack, which showed itself with McDonald’s, has also been among the hacker groups next to Russia.
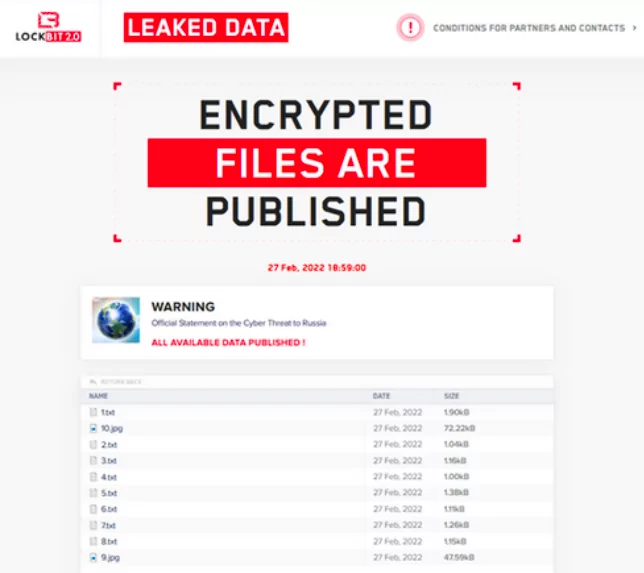
February 27: LockBit noted that there are hackers from different nations within. From Ukraine and Russia and from China to the United States, people from many countries are working for them. “It is the important work to us, and weal has an apolitical stance. We’re only interested in money.” in a statement, the groups’ aid under no circumstances would it attack critical infrastructure.
Cyber Attacks That Happened During the Ukraine-Russia War

Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access


































