Urgent Patching Required for High Severity Vulnerabilities in Zoom
With the widespread adoption of Zoom during the pandemic, the video conferencing platform has become ubiquitous, installed on countless computers and mobile devices worldwide. However, the immense user base and extensive reach of Zoom also make it an attractive target for potential security threats. The sheer scale of its user base raises concerns about the potential attention it may receive from malicious actors seeking to exploit vulnerabilities.
There are newly discovered vulnerabilities which have been identified that might enable remote attackers to gain unauthorized access to systems, escalate privileges, and obtain sensitive data on devices where Zoom is installed. In this blog, we will delve into the latest vulnerabilities discovered in Zoom and explore the necessary steps to protect your devices and ensure a secure Zoom experience.
Vulnerability Details
Here are the technical details of the recently discovered vulnerabilities in the Zoom client software:
CVE-2023-36538 (High Severity): Improper Access Control in Zoom Rooms for Windows (before version 5.15.0) enables an authenticated user to escalate privileges locally.
CVE-2023-36537 (High Severity): Improper Privilege Management in Zoom (versions prior to 5.15.0) may result in privilege escalation for authenticated users.
CVE-2023-36536 (High Severity): Untrusted Search Path in Zoom Rooms installer (before version 5.15.0) exposes a vulnerability that allows unauthorized access.
CVE-2023-34119 (High Severity): Insecure Temporary Files in Zoom Rooms (versions preceding 5.15.0) create a potential avenue for privilege escalation.
CVE-2023-34118 (High Severity): Improper Privilege Management in Zoom Rooms for Windows (before version 5.14.5) enables an authenticated user to escalate privileges locally.
CVE-2023-34116 (High Severity): Improper Input Validation in Zoom Desktop Client for Windows (before version 5.15.0) enables an escalation of privilege through network access.
CVE-2023-34117 (Low Severity): Relative Path Traversal in Zoom Desktop for Windows (versions prior to 5.15.0) allows unauthorized users to disclose sensitive information.
Patch and Update Recommendations
To safeguard against these vulnerabilities and protect user data, it is crucial to take the following actions:
- Update Zoom: Upgrade to the latest version (5.15.0 or later) of the Zoom software.
- Apply Patches: Ensure all current security updates are applied promptly.
- Download Official Releases: Obtain software updates directly from the official Zoom website (https://zoom.us/download) to avoid malicious sources.
- Regularly Check for Updates: Stay vigilant and regularly check for new software releases and security patches.
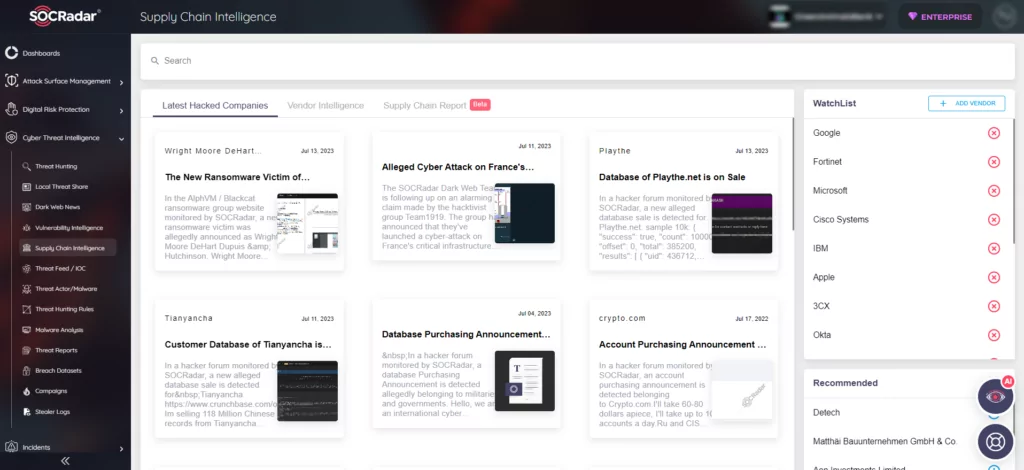
SOCRadar’s Supply Chain Intelligence
By promptly addressing these vulnerabilities and implementing necessary updates, users can strengthen their Zoom security posture and mitigate potential risks. Furthermore, organizations have the opportunity to utilize SOCRadar’s Supply Chain Intelligence, which provides proactive monitoring and assessment of the security posture within their software supply chain. By extending this capability to vendors like Zoom, organizations can effectively mitigate the risks associated with vulnerabilities such as those mentioned above.