US Experiences Increased DoS and DDoS Activities Across Multiple Sectors
The United States is currently observing an upswing in targeted Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) activities, according to recent alerts by the Cybersecurity and Infrastructure Security Agency (CISA). Organizations in different industry sectors have experienced these incidents, which can disrupt regular operations and bring about additional costs.
Understanding DoS and DDoS Attacks
DoS and DDoS activities are essentially attempts to disrupt the usual functioning of a network, service, or server by overwhelming them with excessive internet traffic. Although these events can create temporary operational disruptions and potential cost implications, they are typically manageable with the right response measures.
CISA recommends organizations suspecting a DoS or DDoS attack to promptly seek help from appropriate technical professionals. These include network administrators and internet service providers (ISPs), who can confirm the existence of an attack, identify the source, and apply suitable mitigation tactics.
A Look at the Recent Incidents
The recent surge in these targeted activities coincides with several incidents reportedly linked to Anonymous Sudan, an online group tracked by multiple cybersecurity researchers. According to BleepingComputer, some believe this group may have ties to Russia and has been designated as Storm-1359 by Microsoft.
Anonymous Sudan has claimed to be behind several DDoS attacks that caused temporary outages on online portals for both private and government organizations, including the U.S. Treasury Department’s Electronic Federal Tax Payment System (EFTPS.gov) and the U.S. Commerce Department.
Recently, the group also alleged to have launched an attack on Stripe’s business management dashboard. Moreover, Microsoft confirmed several outages on its Outlook, OneDrive, and Azure web portals were due to DDoS attacks reportedly conducted by this group.
Emphasizing Proactive Measures
In response to the increase in these activities, CISA, alongside the FBI and MS-ISAC, offers guidance on what organizations can do before and after a DDoS attack. These include measures like subscribing to dedicated DDoS protection services that can help reroute malicious traffic away from targeted assets.
Federal civilian executive branch (FCEB) agencies are also advised to leverage tools provided by the General Services Administration (GSA), such as the Managed Security Service (MSS) and the Managed Trusted Internet Protocol Service (MTIPS), to counter the effects of DDoS activities and restore impacted systems.
As the cybersecurity landscape continues to evolve, organizations across all sectors are encouraged to maintain their vigilance and adopt proactive measures to navigate through such incidents.
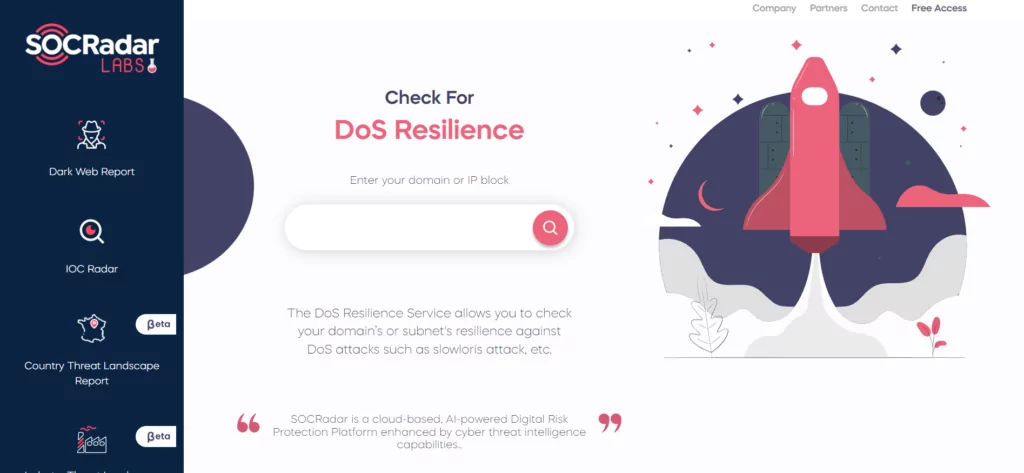
Test DoS Resilience: Free Service by SOCRadar
You can evaluate the resistance of your domain or subnet against DoS attacks such as the slowloris attack by utilizing the complimentary DoS Resilience Service provided by SOCRadar.