

Cyber Kill Chain Model in Cyber Threat Intelligence
Cybersecurity helps to reduce the risk of cyber-attacks and to eliminate the risks. Finding out the best solution to prevent the attacks is very important. However, how can it be possible to reach the maximum potential of the cybersecurity system? In that case, the Cyber Kill Chain comes into play with its layered security structure.
What is The Cyber Kill Chain?
The Cyber Kill Chain is a cybersecurity model created by Lockheed Martin in the early 2000s. The kill chain helps monitor the traces of cyber-attacks, determine the vulnerabilities, and understand the mechanisms of advanced persistent attacks (APTs). This cybersecurity model was developed from a military model, which is also a layered structure model:
“Identify the target → Prepare for it → Engage → Destroy”
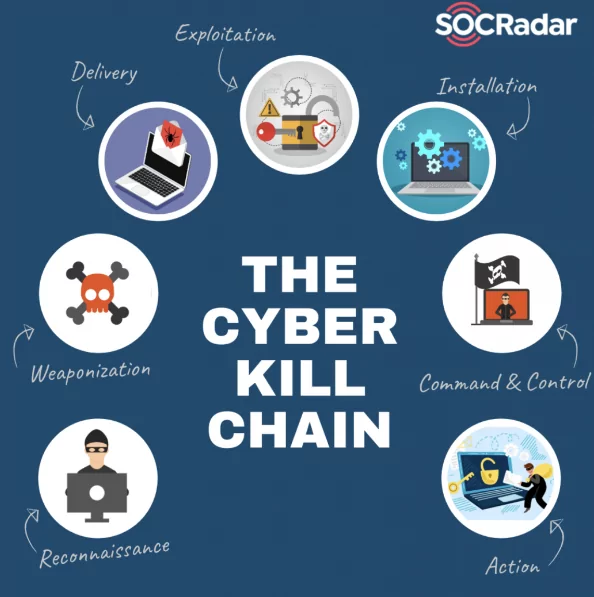
The Cyber Kill Chain has a sequence of steps covering mainly seven stages, from “Reconnaissance” to “Action on the Objective” as a final stage.
How does The Cyber Kill Chain Works?
The cyber-attack risk can be minimized with the help of the layered structure of the Cyber Kill Chain, as mentioned. The Cyber Kill Chain has seven main stages.
1. Reconnaissance: (Observation and gathering data)
This first stage can be defined as the observation of the target. The attackers gather data and find out tactics for the attack. These collected data are used to find out the vulnerabilities of the target system.
2. Weaponization:(Leveraging vulnerability and building up)
In this stage, attackers start to build up malware based on consideration of the vulnerabilities of the target system, which are determined by the first step of the chain. The intention of the attack and the requirements are also considered to develop this malware.
This stage also helps attackers not to be detected by security systems that the organizations already have.
3. Delivery
The attackers transmit the weapon (malware) from the target. Transmission requires a medium. This action can be accomplished in many ways, including websites, removable disks, and e-mails. This can be considered the most crucial step since this is the phase in which an attack can be prevented.
4. Exploitation
By delivering the malware by the victim host, the boundaries are violated. And the attackers are triggered to exploit the victim’s systems by running their codes on the system. Exploitation attacks are mostly scripting and data exchange.
Most of the time, the targets are vulnerabilities of the victim’s systems.
5. Installation
A backdoor or remote access installed by the malware can enable the intruder to maintain its permanence. This is also a crucial stage since the attacks can be again prevented in that stage with, for example, HIPS (Host-based Intrusion Prevention System.).
6. Command and Control
The intruder controls the victim’s system and network at this stage to achieve some sanctions on the system. Searching for credentials and changing permissions are some of the attackers’ actions in this stage to boost their competency in the victim’s system.
7. Actions on Objective
Finally, the attacker can reach their specific goals by extracting the data from the victim’s system. These goals may include gathering, encrypting, and extracting confidential information from the system.
How to Use It with Cyber Threat Intelligence?
To prevent attacks on the systems, the way of thinking and the acting of the attackers should be understood. The cyber kill chain helps to understand these and shows the system’s main requirements and vulnerabilities. And the victim can focus on their vulnerabilities and improve them to resist the attacks. The beauty of the cyber kill chain model is that it allows intervention at every stage.
These are some possible utilization scenarios of the Cyber Kill Chain in cyber threat intelligence:
- To Improve CTI Vendor Strategy:
Cybersecurity vendors are an essential aspect of a cyber strategy for large organizations. Still, it can be challenging to integrate tactical vendor skills into a larger strategy. An informed CISO can better coordinate her defenses against the adversary by considering how each vendor fits with the cyber threat.
- For The Beginners of CTI:
The CTI vendor landscape might be intimidating for those new to the field. Using the method mentioned above, a sense of unity around the vendor landscape can be built, and it becomes clear very quickly which step of the kill chain the vendor was concentrated on when building their initial product strategy.
- For Those Who are Interested In Marketing to CTI Vendors:
CTI suppliers are progressively selling and developing relationships with other CTI vendors. Understanding this potential link within the context of the Cyber Kill Chain can help to bring coherence to the combined offering, with some steps, such as reconnaissance and weaponization, being more reasonable to merge than others.

Gartner is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.









