

What’s the Difference Between Dark Web, Deep Web and Dark Net?
When people discuss the shady underbelly of the internet, stolen data, drugs, weapons, child pornography, rent killings, illegal items, and services can buy you on the darknet to dream of only. The black market beneath the surface of the explicit websites we visit with traditional web browsers and search engines every day lurks a black market full of stolen information, black hat hackers, and the traffickers in human beings and drugs. The dark web, deep web, or darknet is a term that refers to websites that hide their IP addresses and can only be accessed with encryption tools such as The Onion Router.
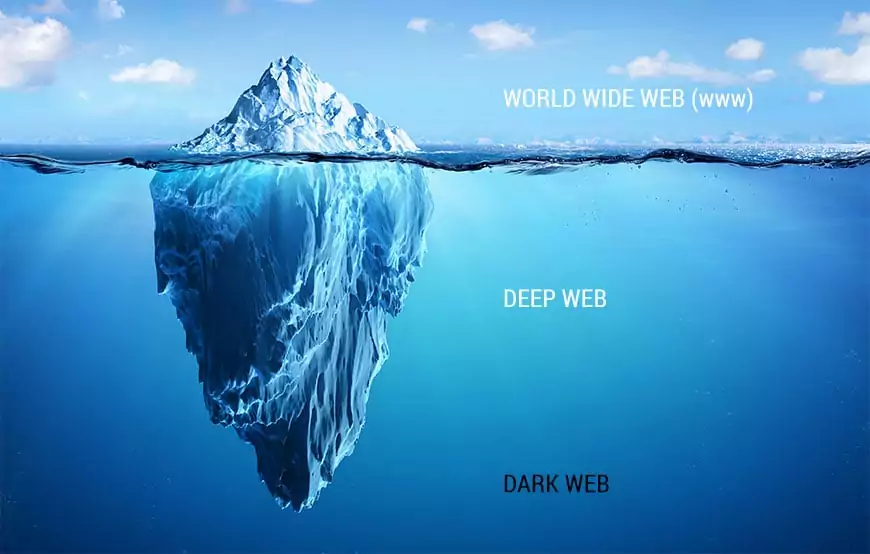
Surface Web: This is the internet as most people are familiar with it. This internet surface includes search engines like Google and Bing, where your IP address can be tracked.
Deep Web: This surface is relatively safe, and it is the part of the internet that is not visible to the naked eye. It contains web pages that search engines are unable to access. This section of the internet is frequently used for social privacy. Governments, banks, and other industries that rely on data security use the deep web to keep their sensitive information safe.
The Dark Web: This is a layer of the internet network in which users engage in largely untraceable online activities. It is heavily used by black markets and is typically used for more illicit purposes than the deep web.
By contrast, the term “dark web” refers to pages accessible only through specialized browsers such as Tor that hide the identity and location of users. Access to the Dark Web is via Tor, the Onion Router, I2P, and the Invisible Internet Project, which masked IP addresses to maintain the anonymity of users and site owners. Its focus on privacy has made it a popular channel for hackers, cybercriminals, and other threats who prefer anonymity regardless of whether the communication or transaction is illegal or not.
Whistleblowers, activists, and political dissidents have good reason to conceal their online locations and posts, but anonymity on the darknet is also a level of secrecy sought by criminals. The anonymity that it offers attracts people who need online privacy.
It allows users to visit websites without divulging information that could be used to track the people they surf the internet. Many legitimate websites, including the New York Times, have a dark web presence, and other reputable organizations try to create websites that offer users a cloak of invisibility.
From a security perspective, the darknet is where cybercriminals sell and trade stolen information such as personal bank details, social security numbers, digital access data, IP addresses, and other trade secrets. The darknet has been associated with nefarious activities such as selling drugs, weapons, and stolen identities, but researchers in the USA have traced its origins. Much of the criminal activity on the Deep and Dark Web relates to botnets, aspects of cybercrime, radar, and unique insights.
Deep and Dark Web users also have many threat actors involved in illegal businesses, such as financial fraudsters, black hat hackers, drug traffickers, and traffickers of illicit goods and services. Users of the dark web recognize that their activities are anonymous and can be associated with persons who engage in illegal activities with legal consequences. When researching dark web activity, organizations should use controllable mapping tools and best-in-class technology to protect their identities and reduce the risk of mission-threatening errors.
For example, law enforcement agencies and journalists use the darknet to keep in touch with whistleblowers, while others use it to protect their identities from government and private surveillance. Make sure you know what information you are looking for when you log onto the encrypted website. Fraudsters can acquire perfect identities, qualify personal details, and open accounts on the Dark Web, so organizations large and small need to ensure that they have robust identity verification and fraud solutions.
The Dark Web is an anonymous, encrypted network that sends traffic worldwide via nodes to disguise a user’s online footprint. The activities of dark web users are unknown because the encryption technology of the darknet directs user data through many intermediate servers to conceal the identity and location of the users.
According to the Journal of Electronic Publishing, the Deep Web contains 400 to 550 times more public information than the Surface Web. Search engines such as Bing and Google account for only 0.4% of the indexed Surface Web. Dark Web is a hidden universe within the Deep Web, a hideaway of the internet from conventional search engines.
Not only is the amount of information on the deep and dark web related to cybercrime, but there is also enough information to reflect the criminal intent to employ cybersecurity experts around the clock. The information people access on the Surface Web is nothing compared to the information available on the Dark Web.
The dark web is a part of the internet where users can access unindexed web content using various encryption methods. The Dark Web has become a community where malicious actors thrive and build empires by stealing and selling IP and PII-based attack methods, including information that affects consumers, the public, large corporations, and governments.
While the FBI refuses to release the source code used to break into the Tor network, law enforcement agencies worldwide monitor and operate the Deep Web. Access to the Dark Web requires the Tor browser, which has built-in privacy features, and the encryption that hides the browser’s location. Tor estimates that about 4% of traffic on its network consists of hidden services and dark web content, while the rest consists of people accessing regular websites with greater anonymity.
How to Access Dark Web
Before you continue, you must understand that many things on the Dark Web are highly illegal. It is improbable that you will be able to remain anonymous, no matter what precautions you take. Enter entirely at your own risk!
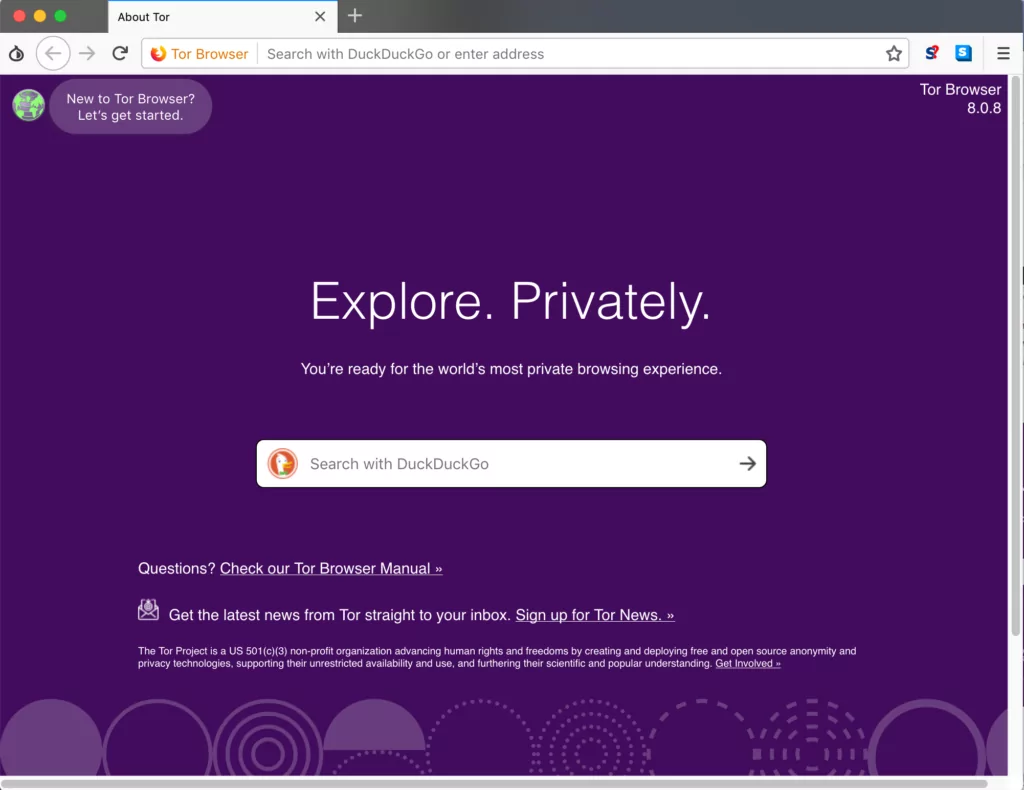
- Download and install the TOR browser
TOR is a modified version of the popular Firefox web browser that allows users to browse the web anonymously. The browser is designed to prevent or warn users against doing things that might reveal their identity, such as resizing the browser window’s dimensions. To install TOR, click (https://www.torproject.org/download/)
- Use VPN
Virtual Private Networks (VPNs) are services that provide secure servers that enable private web access. These servers disguise your location and may impersonate sites from all over the world. Data passing through VPN tunnels are encrypted as well.
- Prefer DuckDuckGo as a Browser
DuckDuckGo is a privacy-focused search engine that doesn’t track everything you do or the websites you visit.
- Sign up for a Secure E-mail Address
Here are a few ideas to get you started:
- ProtonMail – https://protonirockerxow.onion/login
- TORbox – http://torbox3uiot6wchz.onion/
- Elude – http://eludemailxhnqzfmxehy3bk5guyhlxbunfyhkcksv4gvx6d3wcf6smad.onion/
- RiseUp – http://eludemailxhnqzfmxehy3bk5guyhlxbunfyhkcksv4gvx6d3wcf6smad.onion/
- Dark Web Access Points
Here are a couple of relatively harmless “.onion” addresses that you can try out:
- Hidden Wiki (http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion/ )
- Dark Web Facebook (https://www.facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion/ )
- Duck Duck Go (https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/)
- Ahmia (http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/)
- Deep Search (http://search7tdrcvri22rieiwgi5g46qnwsesvnubqav2xakhezv4hjzkkad.onion/ )
References
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free









