Extended Threat Intelligence
Broaden Your Cyber Threat Horizons with Actionable Insights
- Agentic Threat Intelligence Approach: Deliver more dynamic and efficient incident response with autonomous AI agents and intelligent workflows.
- Real-Time Threat Detection: Detect brand impersonations, phishing domains, and vulnerabilities before they impact your operations.
- Scalable SaaS Platform: Customize your intelligence experience with a SaaS-based, scalable platform that offers early warning alerts for maximum protection.
Get Free Extended Threat Intelligence
Discover Your Attack Surface with SOCRadar’s External Attack Surface Management
Organizations need to have better visibility into external facing assets and services and the related vulnerabilities they may present. It is clearly not sufficient to have only EASM solutions to eliminate cyber risks. Rather, EASM technologies are advised to be a component of a broader enterprise vulnerability management strategy.
Protect Your Digital Assets with SOCRadar’s Digital Risk Protection Services
Enterprises are seeking digital asset protection wherever exposure may occur. The traditional focus on social media and the dark web is insufficient as threat actors proliferate sources.
Monitoring capabilities across all environments (cloud buckets, dark web) are considered to equip the security team effectively. For a comprehensive Digital Risk Protection, services like site takedown and automated remediation should also be included. With a full-fledged DRPS , your organization will be more resilient against DDoS attacks.

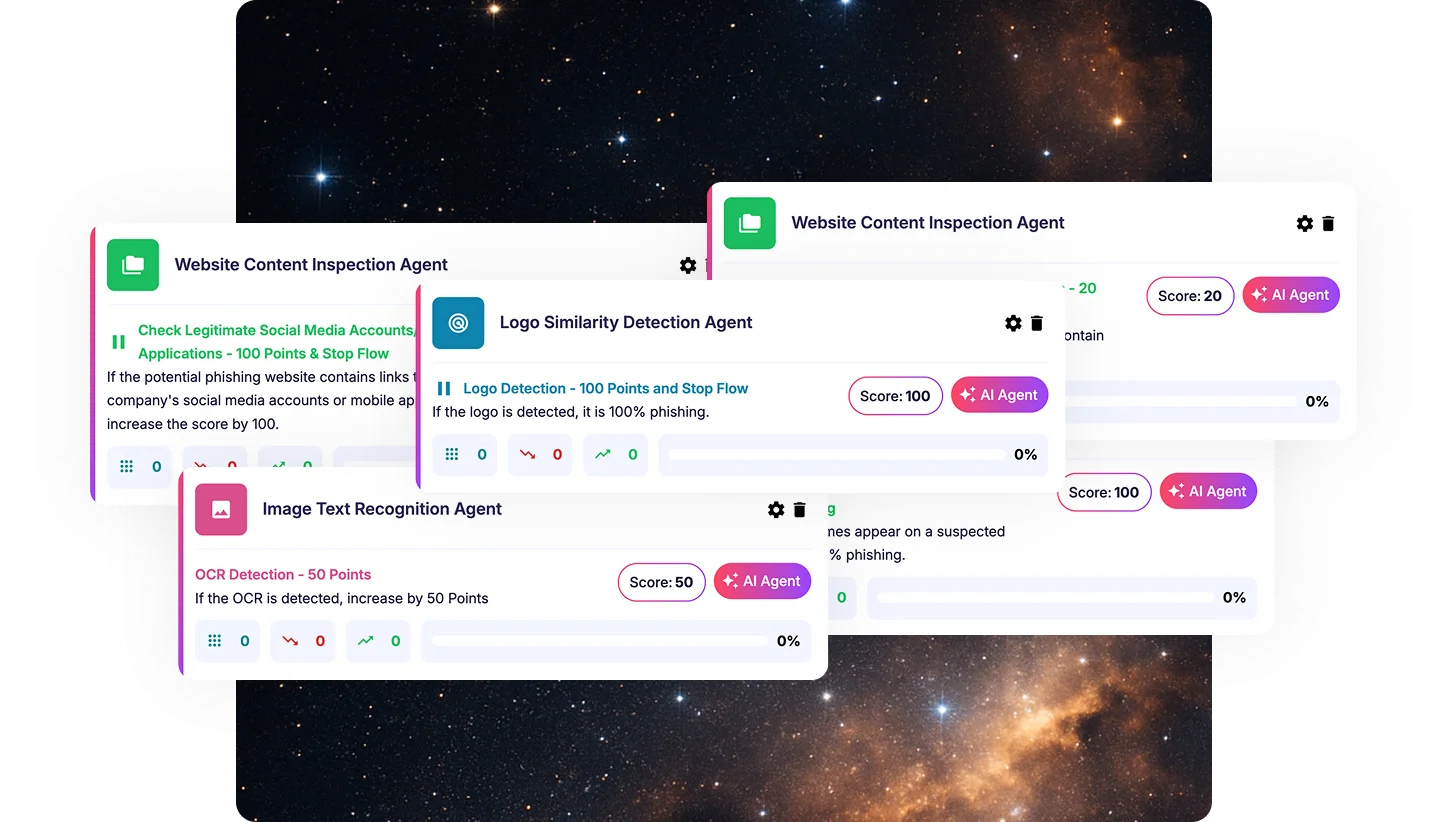
Redefining Cyber Defense with Agentic Threat Intelligence (ATI)
As the volume and sophistication of cyber threats escalate, analysts are reaching breaking point. Conventional CTI tools, while critical, are often difficult to operationalize at scale, placing further strain on already limited resources and expertise.
To solve this, SOCRadar introduces a new cybersecurity paradigm called Agentic Threat Intelligence (ATI). With ATI, organizations can shift away from passively investigating threat feeds and indicators and instead leverage AI-powered agents that track threats, assess context, and trigger the right response — all without human intervention.
SOCRadar XTI offers integrations with various product groups.
As a SaaS and cloud base product, SOCRadar XTI allows users to seamlessly scale their software usage up or down based on their ever-changing needs.
With the customizable dashboard the users can easily manage alarms.
Early warning system against cyber threats
SOCRadar XTI offers monitoring services for dark web and other sources for potential threats targeting organizations, detecting impersonating domains, tracking social media platforms for brand abuse alerting companies to potential threats before they could cause damage.
Only the intelligence
The platform’s deep insights into the evolving threat landscape, with intelligence such as new vulnerabilities, attack methods, sectoral or regional cyber attack campaigns, supply chain attacks and threat actor groups, enables organizations to make informed decisions about security infrastructure, prioritize investments in security technologies.