
Yandex Code Repositories Leaked Allegedly by Former Employee
Yandex, a Russian technology company and popular search engine, has had its source code repositories leaked on a hacker forum. According to Yandex, the repositories were stolen by a former employee.
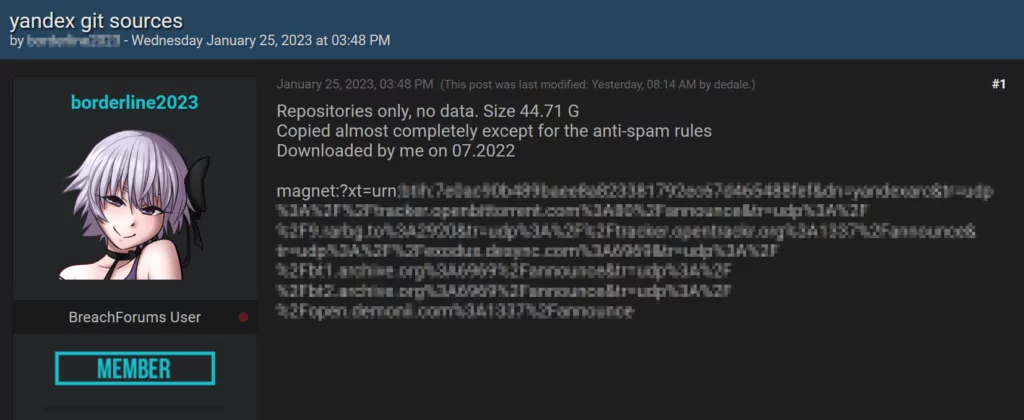
The hacker shared a magnet link with 44.7GB of data on the leak post, explaining that the data is only from the repositories and does not include anti-spam rules. In addition, the hacker claims to have obtained the data in July 2022.
Arseniy Shestakov, a software engineer, examined the data and discovered that all files date back to February 24, 2022, and contain mostly code, not git history.
Which Yandex Services Were Exposed?
The source code leak includes the following Yandex backend services:
- Yandex search engine and indexing bot
- Yandex Maps,
- AI assistant “Alice”
- Yandex Taxi, Yandex Travel
- Ads service “Yandex Direct” and analytics service Metrika
- Yandex 360: Virtual workspace including Mail, Disk, etc.
- Yandex Market, Yandex Pay
- Yandex Cloud
Shestakov notes that although some API keys were exposed, they are probably only used for testing deployment.
You can find a directory listing of the leaked files on GitHub.
How Could Threat Actors Utilize the Leaked Data?
Former Yandex employee Grigory Bakunov, who is familiar with the leaked code, explained that the data leak’s motivation is political and that the rogue Yandex employee responsible for it had not attempted to sell the code to rivals.
According to him, because it does not include any customer data, the leak does not directly harm the privacy or security of Yandex users or pose a threat to proprietary technology.
Only code leaked from the repository. The lack of essential components, such as model weights for neural networks, makes it practically useless.
However, there are a lot of intriguing files with names like “blacklist.txt” that might reveal functioning services.
However, Bakunov warned that the exposed code presents a chance for hackers to find security flaws and craft specialized exploits. It’s now just a matter of time, according to Bakunov.
He offered additional insight into Yandex’s response, stating that although the leaked code might not be 100% identical to the code currently used in the company’s operational services, it might be up to 90% similar.
As a result, a thorough analysis of the leaked code may reveal potential vulnerabilities at Yandex for threat actors.
Regularly Monitor the Dark Web for Data Leaks
SOCRadar can assist you in protecting your organization’s data by scanning the dark web regularly for instances of it being shared or sold, as well as monitoring your digital assets for any potential breaches.
Our platform also monitors thousands of public code repositories such as GitHub and GitLab for exposed sources. Quickly identify and respond to potential threats with SOCRadar and lower the risk of source code leakage.




































