Hackers don’t break in. They log in.
Don’t Wait to Be Breached. See what hackers can already access at your company.
Don’t Wait to Be Breached. See what hackers can already access at your company.
Advanced Dark Web Monitoring
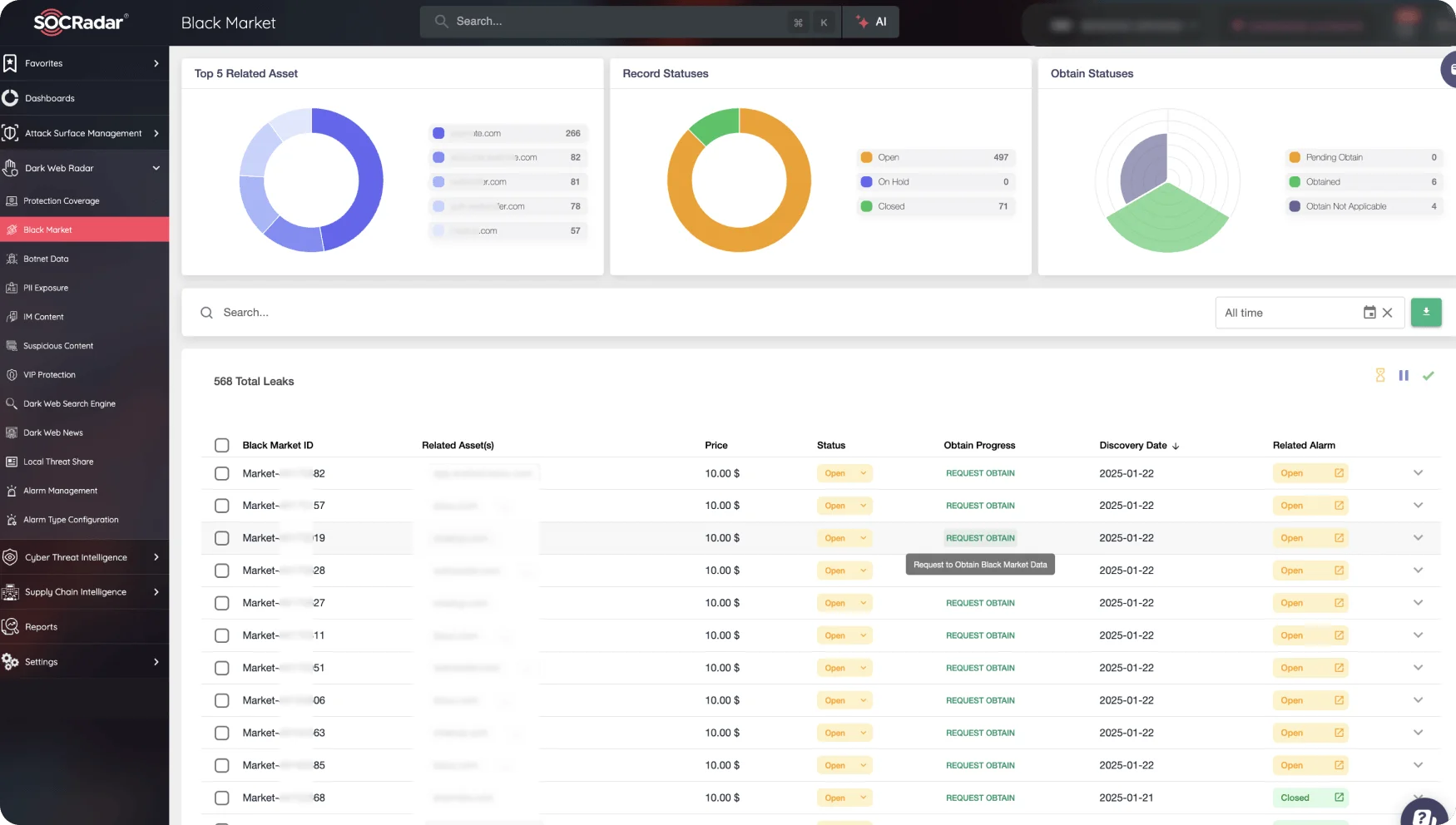
Protect your business from the dangers lurking in the hidden corners of the internet.
Explore Dark Web Monitoring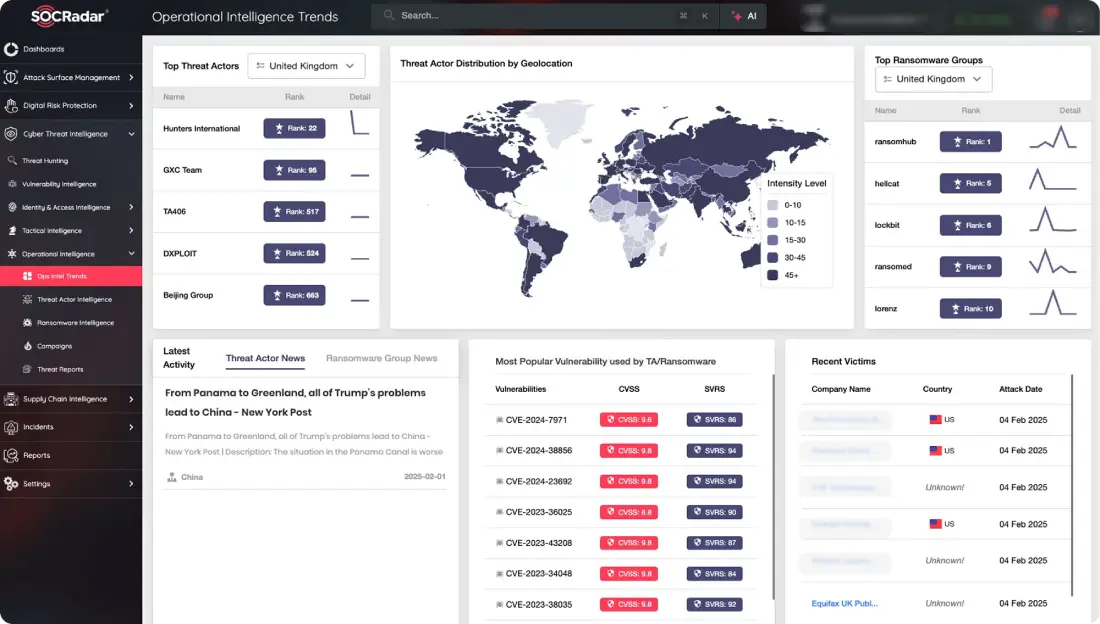
Effective threat hunting and threat actor tracking with behavioral analytics.
Explore Cyber Threat Intelligence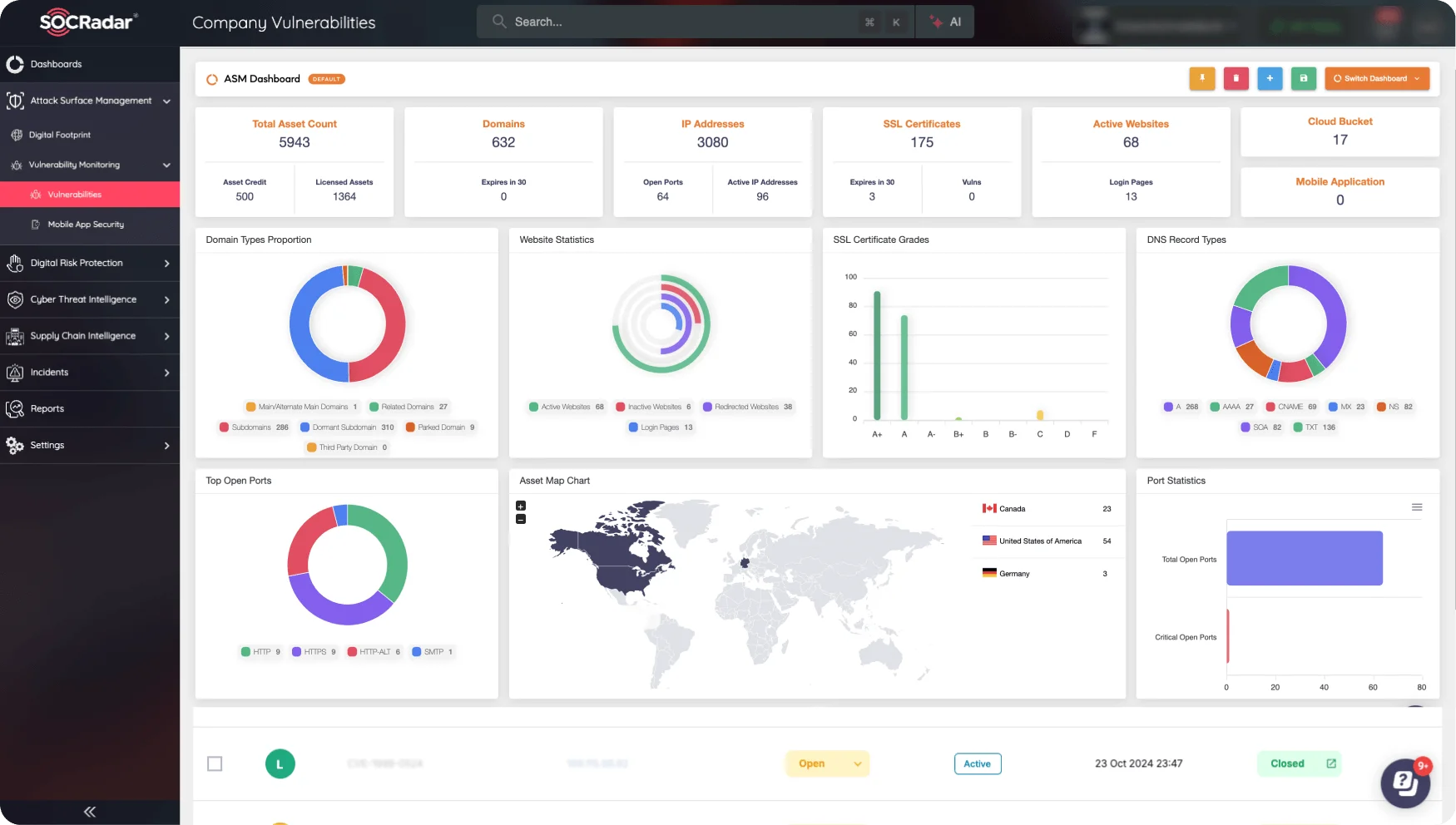
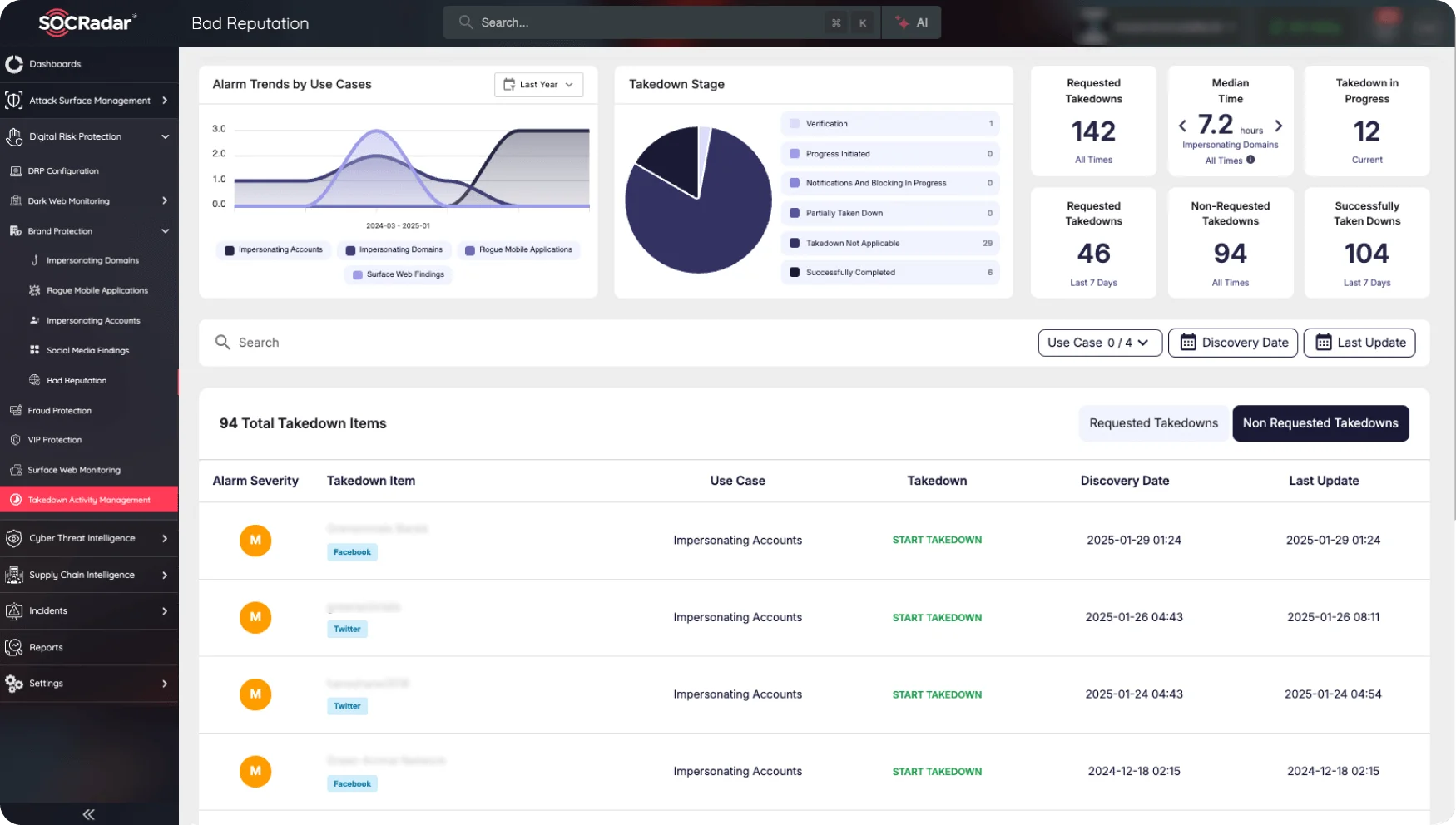
Stay ahead of threat actors with actionable intelligence alerts.
Explore Brand Protection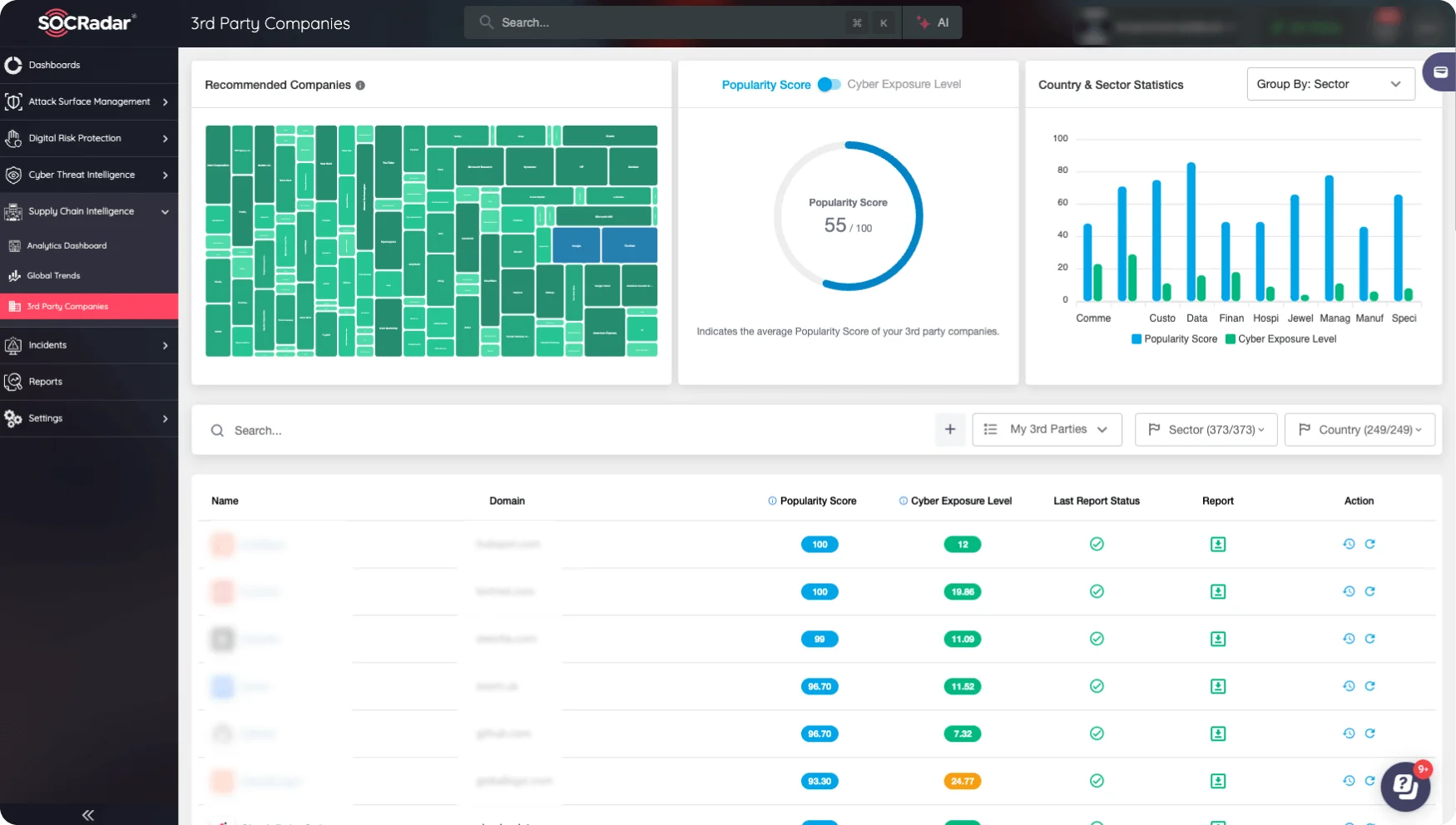
Evaluate the security posture of your entire supply network.
Explore Supply Chain Intelligence















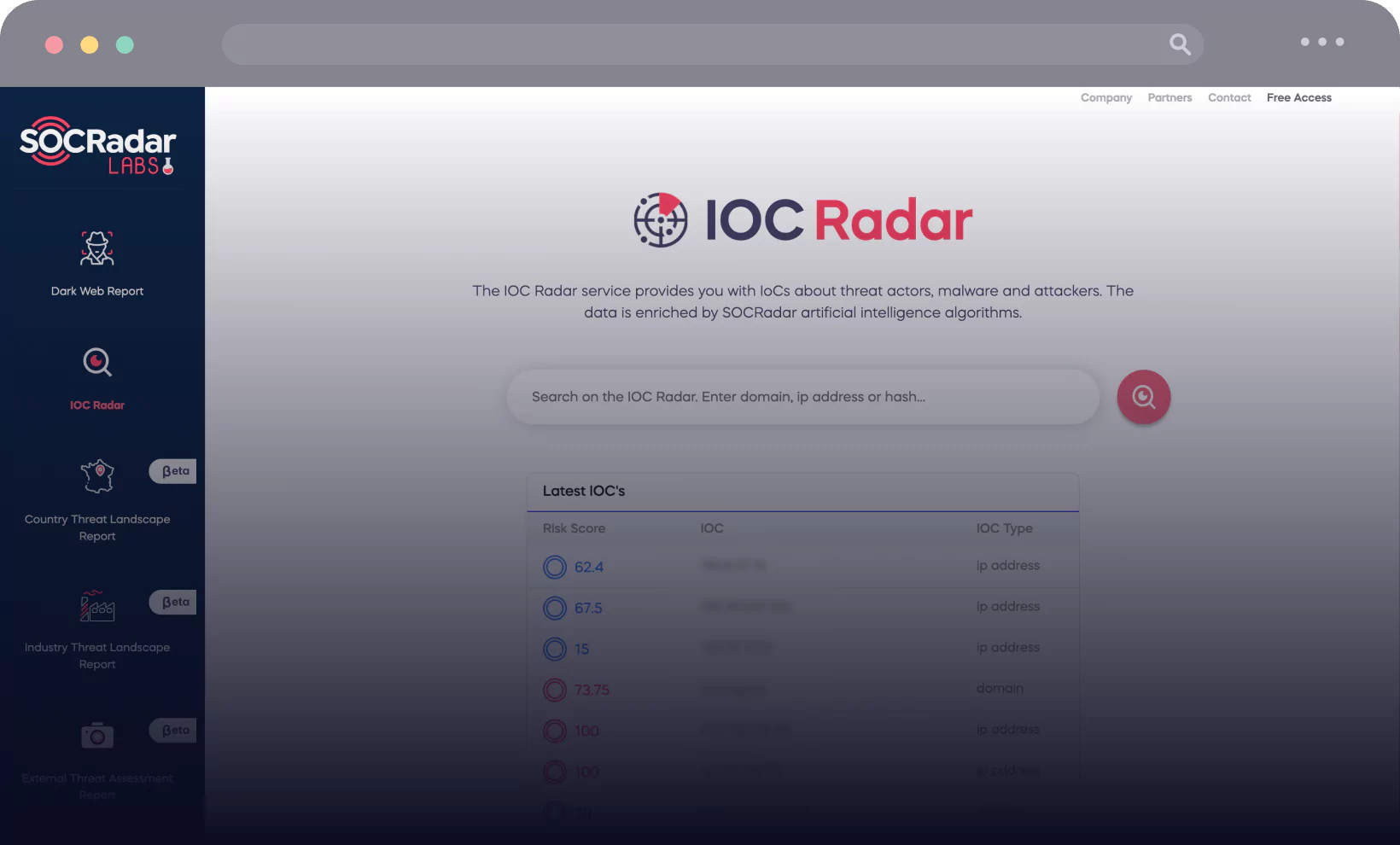
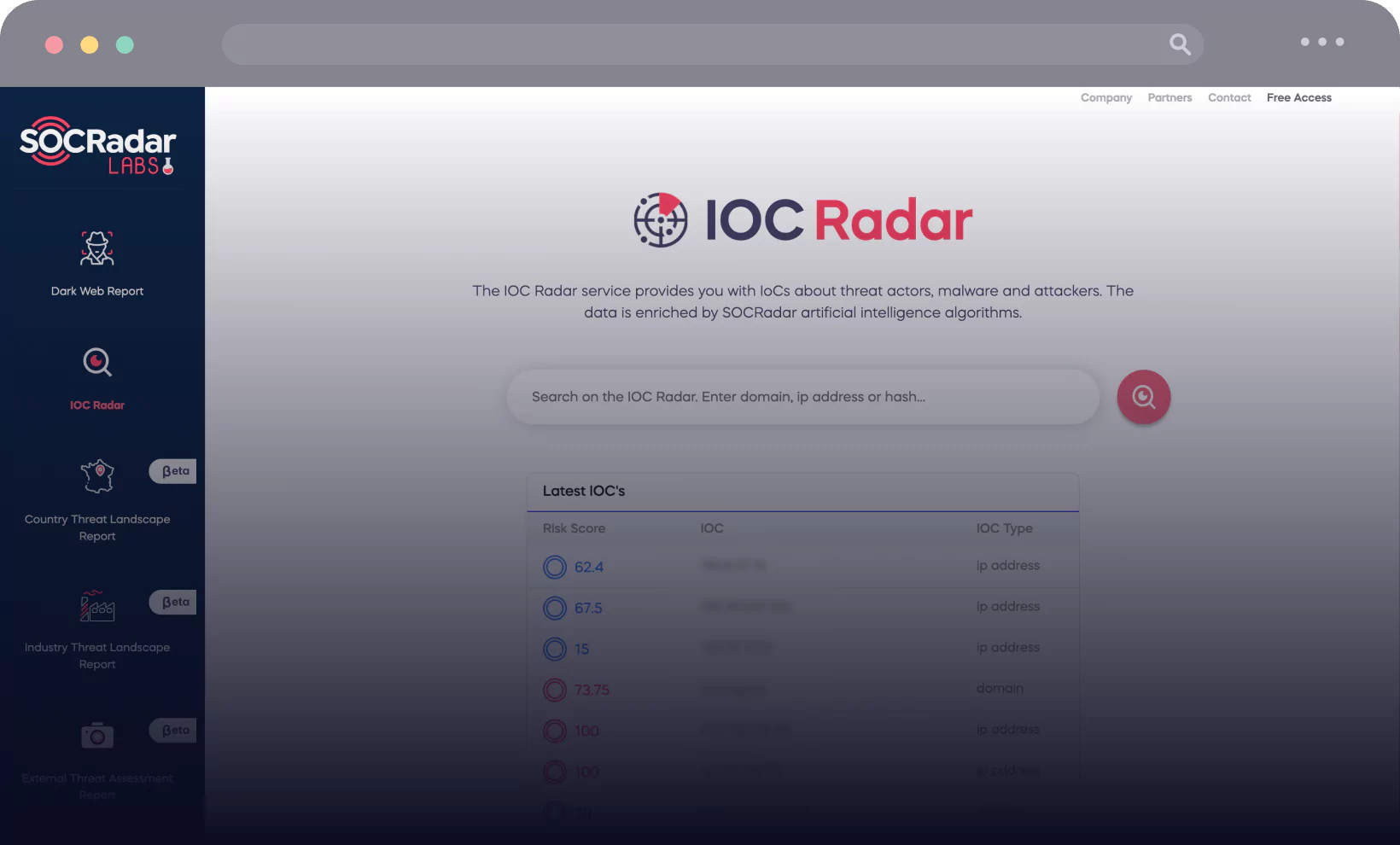
SOCRadar LABS is a new and developing platform which informs users about existing and possible cyber threats with the help of several cyber threat intelligence services.
SOCRadar’s Dark Web Report is a free service that scans the dark web for your domain across dark web forums, black markets, leak sites, or Telegram channels and reports the results.


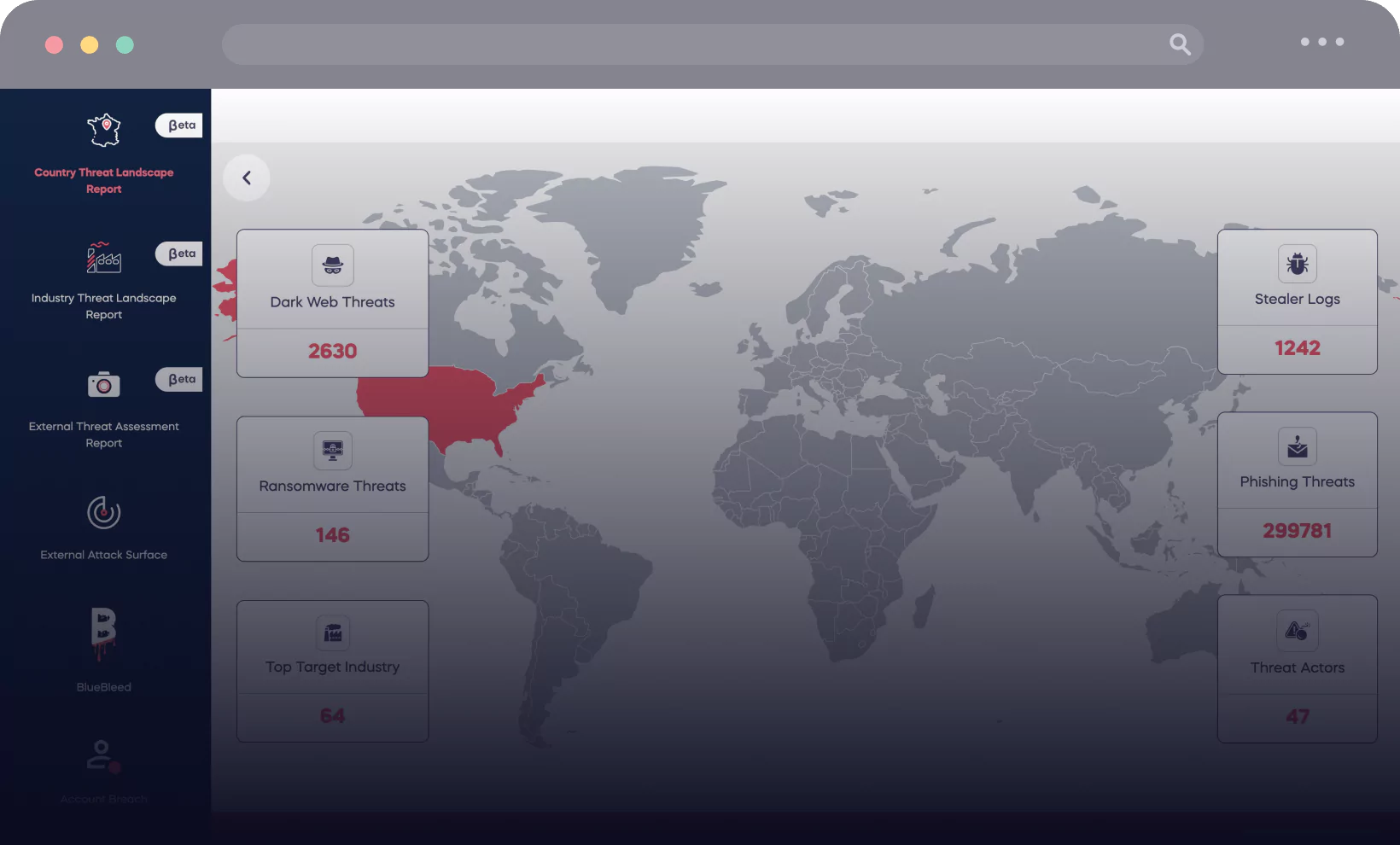
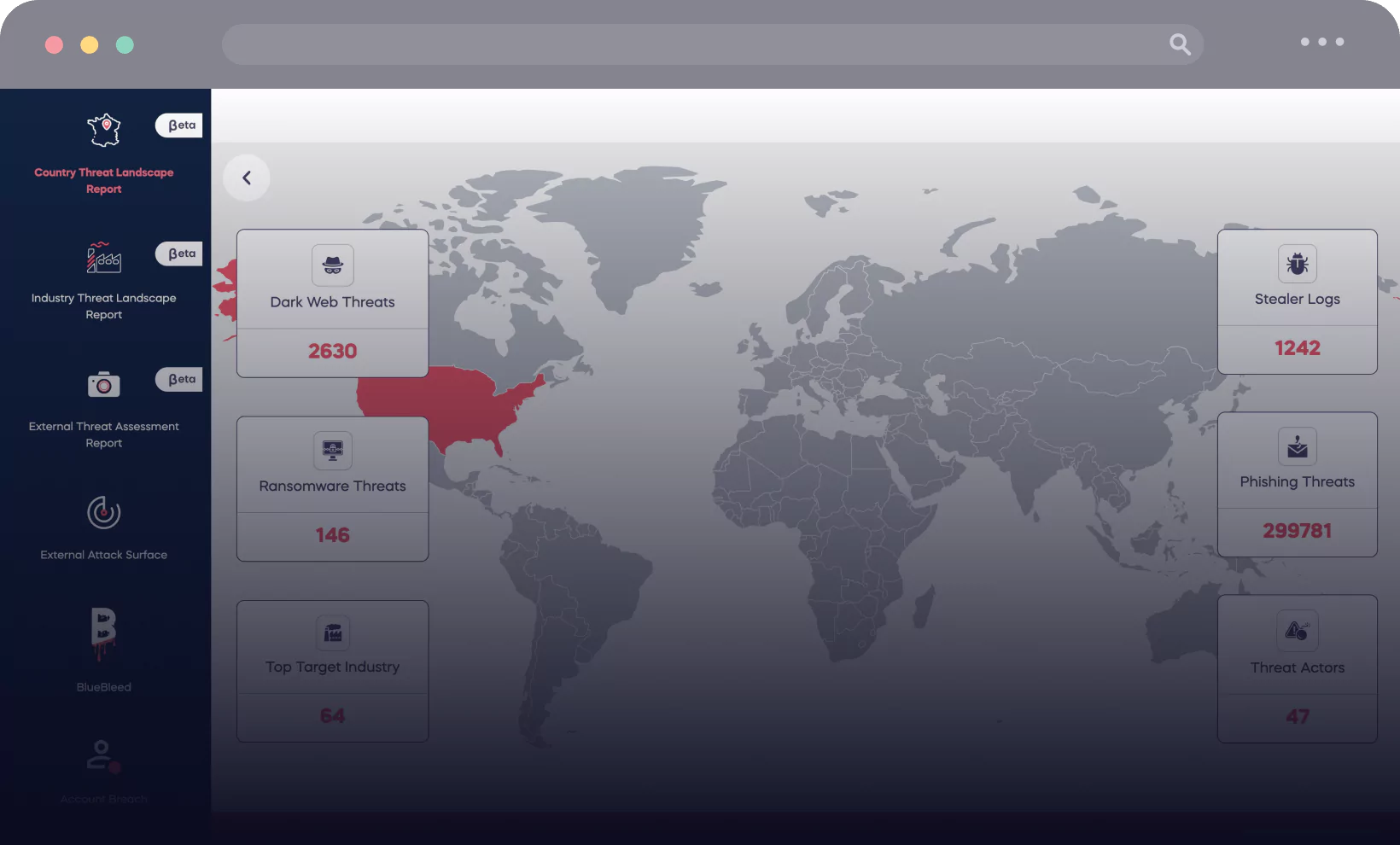
Illuminate your operational landscape with SOCRadar’s AI-powered Country Threat Report. In just a few seconds, unlock key insights into the digital dangers lurking in your company’s regions, from dark web threats to ransomware, phishing, rogue actors, stealer logs, and DDoS attacks.
Power your search with SOCRadar’s IOC Radar. Harness the prowess of our AI algorithms and gain insights on any domain, IP address, or hash. Dive into open-source and dark web findings, and access vital information like risk ratings, location, ASN name, and description.


Both Attack Surface Management and Digital Risk Protection capabilities are continuously being enhanced, SOCRadar keeps making all their modules more powerful and useful.