APT28 Exploits Cisco Vulnerability to Deploy Malware in Espionage Campaign
Russian nation-state actors are using a patched remote code execution vulnerability in Cisco network appliances to conduct surveillance and deploy malware, according to UK and US cybersecurity and intelligence agencies.
The attacks are linked to the APT28 group (Fancy Bear and Sofacy) with ties to the Russian General Staff Main Intelligence Directorate (GRU).
In 2021, APT28 infiltrated several European organizations, US government institutions, and about 250 victims from Ukraine. The group used infrastructure to covertly gain access to Cisco routers around the world using the simple network management protocol (SNMP).
How Did APT28 Infect Routers?
APT28 exploited an old vulnerability tracked as CVE-2017-6742 (CVSS score: 8.8, High).CVE-2017-6742 is a remote code execution vulnerability in Cisco IOS and IOS XE software caused by a buffer overflow in the Simple Network Management Protocol (SNMP) subsystem.
Using the vulnerability, an attacker can write a shellcode in the router’s memory by attaching additional bytes to an object identifier (OID) called alpsRemPeerConnLocalPort.
The threat actor used the vulnerability to deploy a malware dubbed Jaguar Tooth on Cisco routers.
The CVE-2017-6742 vulnerability is one of several SNMP vulnerabilities patched by Cisco in late-June 2017. An attacker must first obtain the SNMP read-only credential and gain access to the vulnerable SNMP OID to exploit the vulnerability.
Since January 2018, the vulnerability has been publicly exploited. To avoid exploitation, applying available patches as soon as possible is critical.
Cisco recommends that users switch from SNMP to NETCONF or RESTCONF for network management.
The Jaguar Tooth Malware
The Jaguar Tooth malware was observed to be deployed in attacks by APT28. The malware is non-persistent, so it cannot survive reboots but can collect information and backdooring.
The malware installed on infected routers modifies the router’s authentication mechanism to accept any password for any local user, allowing unauthenticated backdoor access. It can collect device and network information by issuing IOS CLI commands.
Threat Actors Target Old Network Appliances
Researchers analyzed the APT28 campaign and similar attacks and found that attackers often have pre-existing access to networks, giving them access to credentials and a whitelisted position.
Cisco Talos also notes that the attackers target various vendors’ aging networking appliances and software as part of a broader campaign for espionage objectives or future destructive activity. The attackers install malicious software into infrastructure devices, attempt to surveil network traffic and target TACACS+/RADIUS servers to obtain credentials.
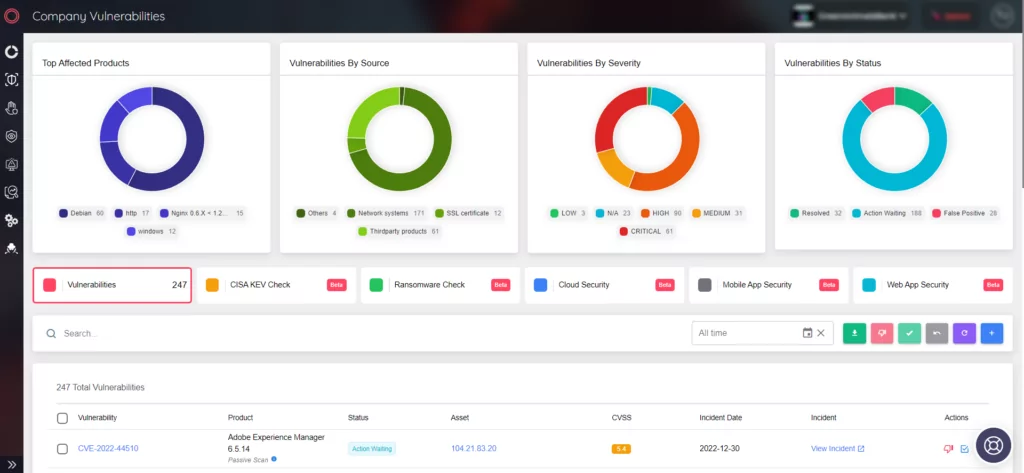
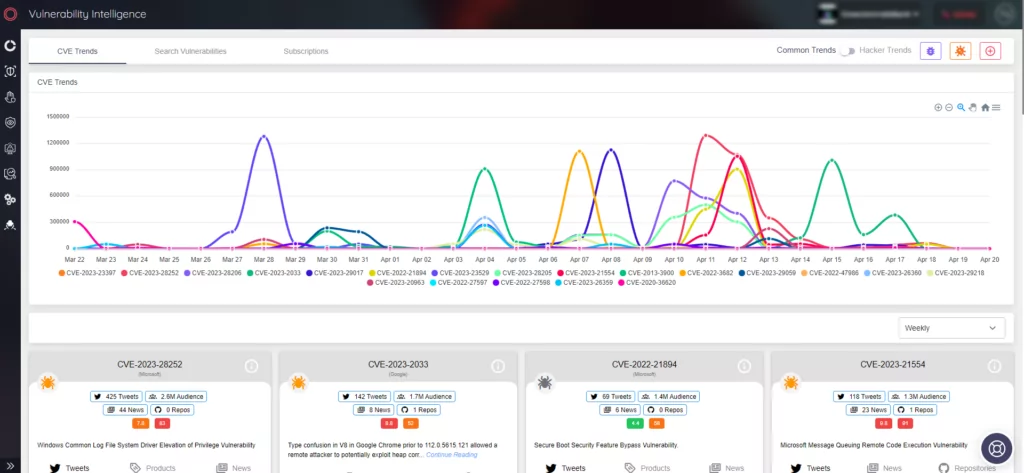
Prioritize Patches with SOCRadar
SOCRadar offers a Vulnerability Intelligence module to help you manage vulnerabilities and prioritize patches. You can access detailed information about vulnerabilities on the platform.
Additionally, Attack Surface Management (ASM) tool can discover your digital assets and alert you to any potential issues.