134M Exploit Attempts: Realtek RCE Vulnerability Targeted in Large-Scale Attacks
Threat actors stepped up their efforts to exploit a remote code execution vulnerability in the Realtek Jungle SDK between August and October 2022, according to researchers. A report from Palo Alto Networks noted that the attacks targeting the vulnerability accounted for more than 40% of all attacks during that period.
The vulnerability, identified as CVE-2021-35394 (CVSS score: 9.8), has seen 134 million exploitation attempts as of December 2022.
Researchers discovered that the attacks involved attempts to infiltrate vulnerable IoT devices and spread malware, indicating that threat actors intend to launch widespread, large-scale attacks with the Realtek vulnerability.
CVE-2021-35394 affects nearly 190 different devices from 66 manufacturers. Attackers specifically target the vulnerability because it can disrupt supply chains, making it challenging for the average user to identify affected products.
Approximately half of the attempts to exploit the vulnerability came from the US, with Vietnam and Russia coming in second and third place in attack sources.
Most of the malware samples discovered in the attacks are from well-known families like Mirai, Gafgyt, and Mozi malware. Researchers also found a new distributed denial-of-service (DDoS) botnet in attacks named RedGoBot.
Three Different Payloads for Exploitation
Researchers discovered three types of payloads in the wild that were used to exploit CVE-2021-35394:
- Type 1: A script that runs a shell command on the targeted server, connects to a malicious IP address, and downloads malware. The Mirai malware family was responsible for the majority of type 1 threats.
- Type 2: An injected command that writes a binary payload to a file and executes it.
- Type 3: Another injected command that can directly reboot the targeted server, resulting in a denial-of-service status (DoS).
Another vulnerability was fixed in a security advisory released by QNAP.
Critical Flaw in QNAP that Lets Malicious Code Injection is Fixed

Customers of QNAP are being advised to update their QTS and QuTS firmware to fix a severe security flaw that enables remote attackers to inject malicious code into QNAP NAS devices.
The company has rated the vulnerability as critical and has tracked it as CVE-2022-27596 with a CVSS score of 9.8.
The flaw affects the operating system’s QTS 5.0.1 and QuTS hero h5.0.1 versions. The vulnerability has not been flagged as being actively exploited in the wild by QNAP’s advisory.
The NIST portal refers to the vulnerability as a SQL injection flaw, though the vendor hasn’t provided much information about it.
A JSON file describing the severity of the vulnerability was also made available by QNAP. This file shows that remote attackers can easily exploit it in low-complexity attacks without the user’s interaction or privileges on the target device.
Update to the Latest Versions
Users are advised to apply security updates as soon as possible due to the flaw’s seriousness, as threat actors actively target QNAP vulnerabilities. The company fixed the vulnerability in the following operating system versions:
- QTS 5.0.1.2234 build 20221201 and later
- QuTS hero h5.0.1.2248 build 20221215 and later
Users must first log in as administrators on their devices before going to Control Panel > System > Firmware Update to apply the update. After selecting “Check for Update” in the “Live Update” section, wait for the download and installation to be finished.
The update is also available for download from the QNAP website. Follow the instructions for a manual update for your device under Support > Download Center.
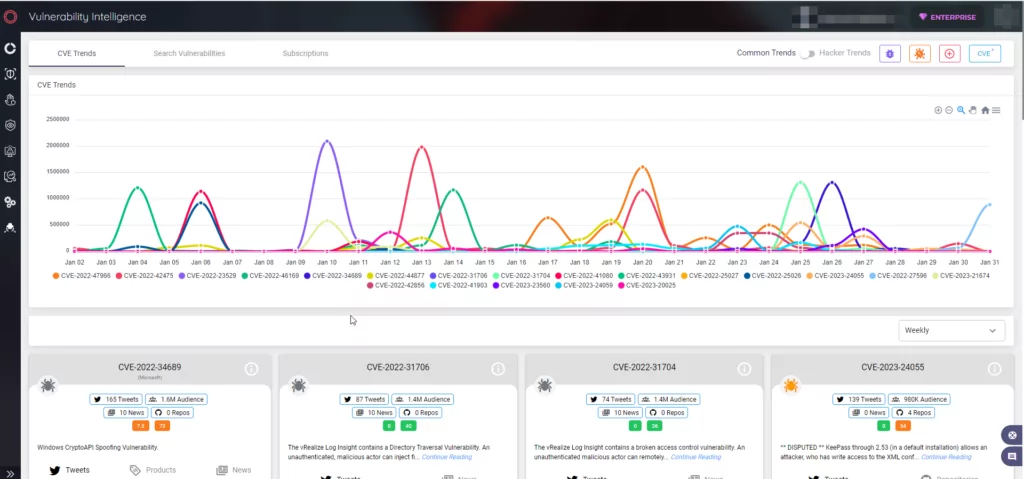
Stay Safe with SOCRadar’s Vulnerability Intelligence Module
SOCRadar is a helpful threat intelligence platform for keeping up with the most recent risks and vulnerabilities. SOCRadar constantly scans your perimeter from the attackers’ point of view to identify critical internet-facing vulnerabilities that threat actors can exploit.
You can search for and view in-depth information about vulnerabilities on SOCRadar’s Vulnerability Intelligence module, which can help you manage vulnerability issues and prioritize patches.