
Atlassian Patched Critical Vulnerability That Affects Confluence Servers
Atlassian announced that it has released an update for a critical vulnerability affecting its Confluence Server and Data Center products. The vulnerability, which allows unauthenticated actors to gain remote access, is tracked with the code CVE-2022-26138 and is defined as a “hardcoded credentials vulnerability.”
The vulnerability is exposed to exploitation by installing the following versions of Questions for Confluence:
- 2.7.34
- 2.7.35
- 3.0.2
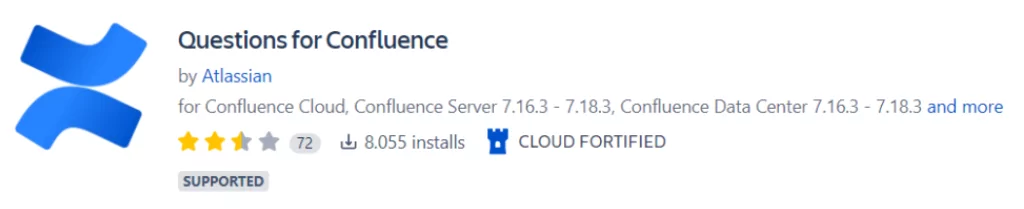
The Questions for Confluence app currently has nearly 8,000 downloads.
Atlassian states, “When Questions for Confluence is enabled on the Confluence Server, or Data Center, a Confluence user account with the username disablesystemuser is created. This account is intended to assist administrators migrating data from the app to Confluence Cloud.” regarding the vulnerability.
disablesystemuser has hardcoded credentials and is added by default to a group called confluence-users, which allows viewing and editing of pages accessible to the group.
Last month, an RCE vulnerability affecting Confluence servers also emerged.
How to Fix the Vulnerability?
The following credentials can be checked to see if Confluence Server or Data Center is affected by this vulnerability:
- User: disabledsystemuser
- Username: disabledsystemuser
- Email: dontdeletethisuser@email[.]com
If these credentials are active, it is recommended to disable them until the update is done. Deleting Questions for Confluence is not enough to fix the vulnerability. The guidance on Atlassian’s website can help identify if the vulnerability has been exploited.
An update to the latest version is required, which completely removes these credentials and stops regenerating. The versions where the vulnerability was fixed are:
- For 2.7.x, an update to 2.7.38 is recommended (Compatible with Confluence 6.13.18 – 7.16.2)
- For 3.0.x, an update to 3.0.5 is recommended (Compatible with Confluence 7.16.3 and later)
You can look at Atlassian’s security advice and FAQs for more detailed information on the subject.




































