CISA Warned of Critical Fortinet Vulnerability (CVE-2023-44250) and Issued a New ICS Advisory
In a recent alert, the Cybersecurity and Infrastructure Security Agency (CISA) has urged users and administrators to visit a Fortinet advisory for mitigating a high-severity vulnerability, identified as CVE-2023-44250.
The agency underscores the potential for threat actors to exploit CVE-2023-44250, gaining control of affected systems. Consequently, organizations are strongly urged to take immediate action in response to this security concern.
Details of the Latest Fortinet Vulnerability: CVE-2023-44250
The CVE-2023-44250 vulnerability holds a CVSS score of 8.3, signaling its high severity. Fortinet’s advisory describes it as an improper privilege management vulnerability. Exploitation of this vulnerability may enable an authenticated attacker to perform elevated actions through crafted HTTP or HTTPS requests.
The affected Fortinet products and versions, along with the corresponding fixed versions, are as follows:
- FortiOS 7.4, 7.4.0 – 7.4.1 –> upgrade to 7.4.2 or above
- FortiOS 7.2, 7.2.5 –> upgrade to 7.2.6 or above
- FortiProxy 7.4, 7.4.0 – 7.4.1 –> upgrade to 7.4.2 or above
You can visit the advisory and access the Fortinet upgrade tool here.
Stay vigilant by reviewing the latest security vulnerabilities and ensuring your products and software are up-to-date. To assist you with vulnerability management, SOCRadar monitors digital assets and promptly issues alerts in the event of emerging vulnerabilities.
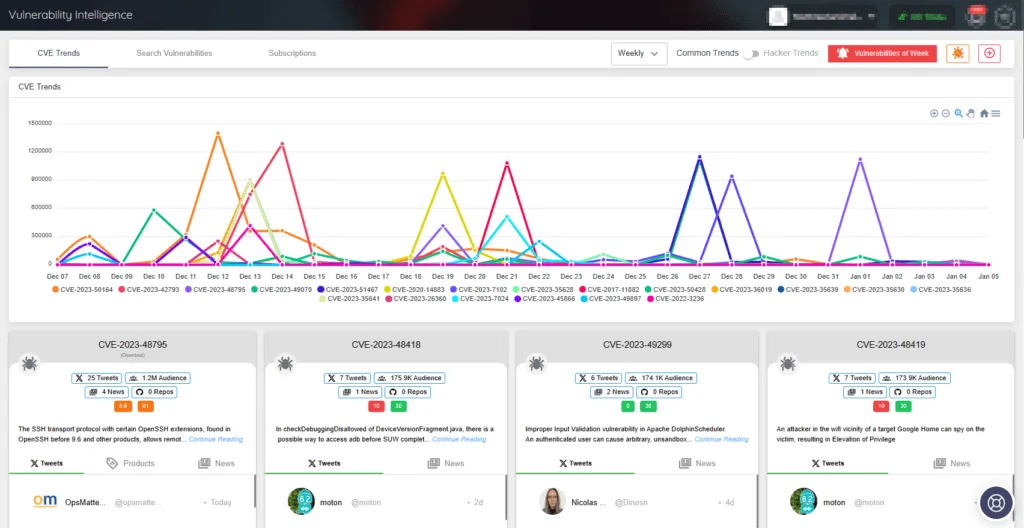
SOCRadar Vulnerability Intelligence
CISA Issued a New ICS Advisory for a Critical Vulnerability Affecting Cambium Networks (CVE-2023-6691)
In other news, CISA has issued a new Industrial Control Systems (ICS) advisory on January 9, 2024, aiming to alert about the current vulnerabilities within ICS environments.
The latest ICS advisory spotlights a high-severity vulnerability impacting Cambium Networks’ ePMP Force 300-25, a connectivity product designed for operation in high interference environments. The affected product version is identified as 4.7.0.1.
Tracked as CVE-2023-6691, the vulnerability carries a CVSS score of 7.8, with CISA drawing attention to its low attack complexity. It is identified as a code injection vulnerability, wherein successful exploitation could grant an attacker the ability to execute code and gain root privileges.
This specific vulnerability, affecting a globally utilized product in the communications sector, serves as a reminder to remain vigilant in tracking such vulnerabilities to stay ahead of threat actors.
SOCRadar’s Vulnerability Intelligence is an invaluable tool for efficiently managing security vulnerabilities and prioritizing patches. Users can easily search for vulnerabilities, access detailed information about them, and track the lifecycle of each vulnerability through the module.
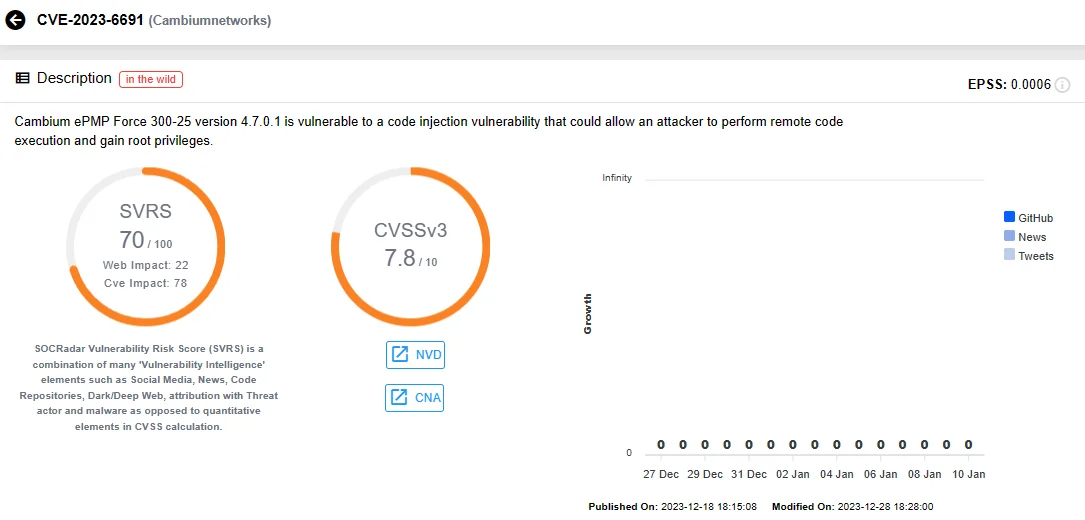
SOCRadar Vulnerability Intelligence: CVE-2023-6691
CISA has recently released three other ICS advisories, detailing vulnerabilities in Rockwell Automation, Mitsubishi Electric, and Unitronics; for an overview of these advisories, refer to our other blog post.