CISA’s Recent Summary: Critical Vulnerabilities Impacting Apple and Other Prominent Entities
CISA has recently published a Vulnerability Summary for the previous week. This summary encompasses several vulnerabilities that have impacted prominent entities such as Apple, Google, WordPress, Trendmicro, and Microsoft.
These vulnerabilities represent potential security risks that have been recently recorded, underscoring the importance of staying informed to ensure appropriate preventive measures can be taken. In the following section, we have provided explanations for some of these vulnerabilities.
Critical Vulnerabilities Affecting MacOS, Android and WordPress
CVE-2022-22630 (CVSS Score: 9.8, Critical): An issue known as “Use-After-Free” has been addressed through an improved memory management system. Use-After-Free is a security flaw caused by the improper use of dynamic memory while a program is running. If exploited by a remote user, it could lead to an unexpected termination of an application or the execution of arbitrary code. This problem has been fixed in macOS Big Sur 11.6.6, macOS Monterey 12.3, and Security Update 2022-004 Catalina.
CVE-2023-32412 (CVSS Score: 9.8, Critical): Improved memory management has resolved another use-after-free problem. The issue has been successfully addressed in macOS Ventura 13.4, macOS Big Sur 11.7.7, and macOS Monterey 12.6.6. Consequently, the risk of a remote attacker causing unexpected app termination or executing arbitrary code has been mitigated.
CVE-2023-32387(CVSS Score: 9.8, Critical): This is another use-after-free vulnerability resolved by improved memory management. The issue has been fixed in macOS Ventura 13.4, macOS Big Sur 11.7.7, and macOS Monterey 12.6.6. Following these updates, the possibility of a remote attacker causing unexpected app termination or executing arbitrary code has been eliminated.
CVE-2023-21066 (CVSS Score: 9.8, Critical): There is a potential heap buffer overflow in the cd_CodeMsg of cd_codec.c, which could result in an out-of-bounds write. This vulnerability affects Android versions using the Android kernel. If exploited, this vulnerability could result in remote code execution without requiring any extra execution privileges. It is important to note that user interaction is not necessary for the exploitation of this vulnerability.
CVE-2023-2982 (CVSS Score: 9.8, Critical): The WordPress Social Login and Register (Discord, Google, Twitter, LinkedIn) plugin for WordPress, up to and including version 7.6.4, has a vulnerability that allows authentication bypass. The issue arises from insufficient encryption of the user’s information during a login process that relies on the plugin. As a result, unauthenticated attackers have the potential to log in as any existing user on the website, including administrators, if they possess the corresponding email address. To address this vulnerability, a partial fix was implemented in version 7.6.4, and a complete fix was applied in version 7.6.5.
It is recommended that affected users promptly apply the available fixes and updates provided by the respective software vendors to eliminate these critical vulnerabilities.
Stay Ahead of Security Threats with SOCRadar
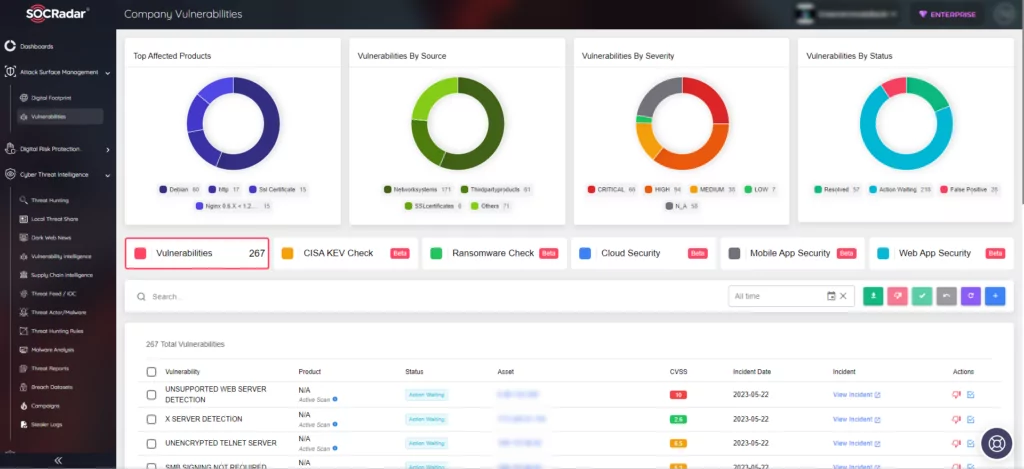
SOCRadar offers organizations a valuable solution for staying updated on the latest security threats and vulnerabilities. By collecting information on known vulnerabilities, it presents this data in a user-friendly format, making it easier to take action.
Through alerts, users can prioritize their response efforts and stay informed about potential risks to their organization.
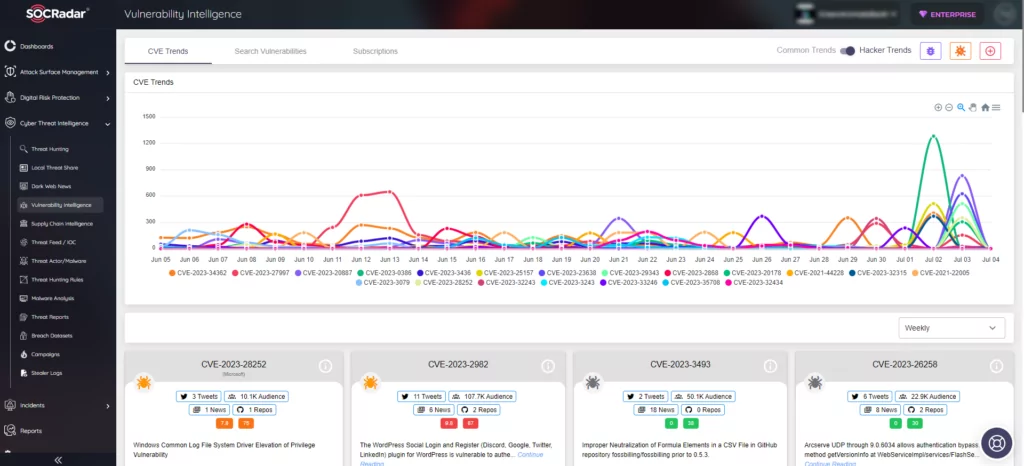
Utilizing SOCRadar’sVulnerability Intelligence module provides access to comprehensive details about vulnerabilities. This feature enables effective management of related issues and facilitates prioritization of necessary patches.
Furthermore, SOCRadar’s Attack Surface Management allows for real-time monitoring of vulnerabilities in products automatically identified within an organization’s digital footprint. This proactive approach empowers security teams to prioritize vulnerabilities based on contextual intelligence.