
Cloud Threat Actor Spotlight: GUI-vil’s Strategies in AWS Compromises
Researchers have been tracking a financially motivated threat group known as GUI-vil (aka p0-LUCR-1), based in Indonesia, which engages in unauthorized cryptocurrency mining. Researchers first observed this threat actor in November 2021, and recently in April 2023.
GUI-vil exploits Amazon Web Services (AWS) Elastic Compute Cloud (EC2) instances with compromised credentials to facilitate their illegal crypto mining operations. In many cases, the profits from cryptocurrency mining are only a fraction of what victim organizations must pay to run the EC2 instances.
The GUI-vil attackers prefer Graphical User Interface (GUI) tools and have been using an older version of S3 Browser (version 9.5.5) since November 2021; they complete initial access, reconnaissance, and persistence with the same GUI utility.
Unveiling the Tactics and Motives of GUI-vil
GUI-vil attackers start an attack by monitoring public sources for exposed AWS keys and scanning for vulnerable GitLab instances. The threat actor is observed to exploit known vulnerabilities or to use publicly exposed credentials for initial compromise.
After gaining access to AWS Management Console, the group carries out its activities directly via the web browser. Permiso researchers, who track the threat actor, highlight that GUI-vil attackers do not rely on automation unlike other cloud attackers, and are active at the keyboard. The attacker’s source IP addresses are associated with the following Indonesian Autonomous System Numbers (ASNs): PT Telekomunikasi Selula and PT Telekomunikasi Indonesia.
Instead of following conventional methods to establish a presence, GUI-vil impersonates legitimate users by their names, policies, keypairs, and other attributes. Alternatively, it takes control of existing user accounts by creating login profiles for users who previously did not have one. Researchers can identify this activity through “iam:GetLoginProfile” failures followed by successful “iam:CreateLoginProfile” actions.
By using IAM user profiles, the GUI-vil attackers blend in; however, they often make errors by not modifying the default settings of S3 Browsers. They frequently use the default bucket name (YOUR-BUCKET-NAME), as well as default policies and IAM user names. The GUI-vil attackers are also observed to resist when defenders detect them, determined to maintain access in an environment.
How Does GUI-vil Carry Out the Attacks?
GUI-vil does not target specific organizations but takes advantage of any organization with compromised credentials. They follow a series of steps in their attack process:
- Initial Recon:
- GUI-vil monitors public sources like GitHub and Pastebin for exposed AWS access keys.
- They scan software repositories such as GitLab for vulnerable versions.
- Initial Compromise & Establishing Foothold:
- They exploit CVE-2021-22205 to gain remote code execution (RCE) on vulnerable GitLab instances.
- Alternatively, they often find publicly exposed credentials directly.
- They use discovered access keys to gain a foothold in the AWS environment, validating their credentials using the S3 Browser utility.
- Escalate Privileges:
- GUI-vil rarely needs to elevate privileges due to over-privileged cloud credentials.
- In one case, they start with read-only permissions and then find credentials with full administrator privileges in Terraform tfstate files.
- Internal Recon:
- GUI-vil performs internal reconnaissance by reviewing accessible S3 buckets.
- They explore and identify services the victim organization uses through the AWS Management Console.
- They also monitor CloudTrail logs to adapt their persistence and bypass organizational restrictions.
- Maintain Presence (IAM):
- GUI-vil creates new Identity and Access Management (IAM) users to persist in the environment.
- They mimic the naming standards of existing IAM users and sometimes forget to change default names.
- Access keys and login profiles are created for the new identities to continue using S3 Browser and AWS Management Console, respectively.
- Inline policies are attached to grant the created IAM users full privileges.
- Maintain Presence (EC2):
- GUI-vil maintains persistence in the environmentby connecting to Elastic Compute Cloud (EC2) instances and assuming their credentials.
- They execute ec2:CreateKeyPair to enable SSH access and ensure it’s open to the internet on their created EC2 instances.
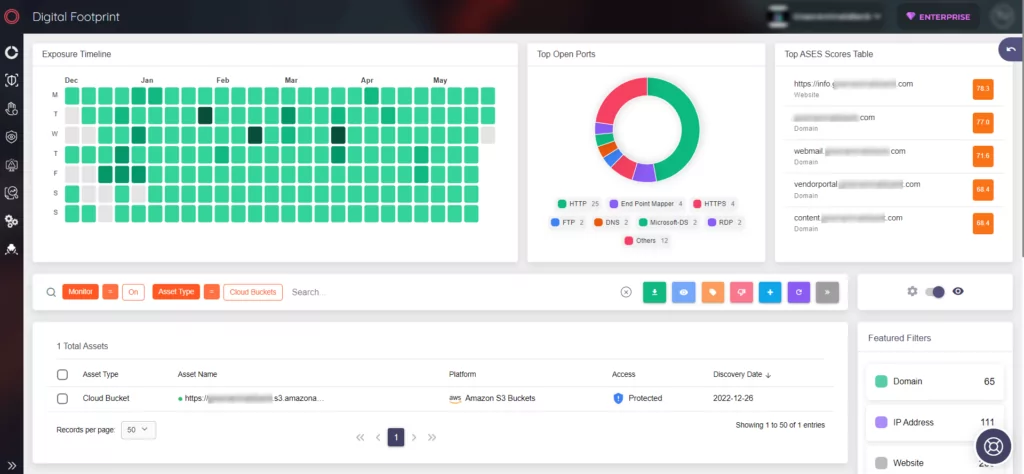
Ensure Cloud Bucket Security with SOCRadar CSM
With SOCRadar Cloud Security Module (CSM), you can stay informed about new cloud buckets connected to your organization and receive timely updates on their status, including leak notifications about repositories. The module provides proactive monitoring and alerts for cloud buckets associated with your organization.
It continuously monitors the status of your buckets and promptly notifies you through “Cloud Bucket Status Change” alerts if any concerning situations arise.
Additionally, if you’re interested in expanding your knowledge on cloud security, we recommend reading our blog post titled “Secure Your Cloud Environment: 5 Best Practices.”




































