CrushFTP Vulnerability Under Active Exploitation (CVE-2025-31161): What You Need to Know
[Update] April 8, 2025: CISA Flags Actively Exploited CrushFTP Vulnerability (CVE-2025-31161)
A newly discovered flaw in the CrushFTP file transfer platform is under active exploitation, with threat actors leveraging publicly released Proof-of-Concept (PoC) code to compromise vulnerable servers. The issue, an authentication bypass vulnerability, grants unauthorized access to systems running specific versions of the software.
CrushFTP initially informed its customers of the vulnerability through a private advisory on March 21, without naming a CVE. This blog outlines the vulnerability’s disclosure timeline, what it is about, and the confusion around its CVE assignment, as well as why immediate action is necessary to mitigate the growing threat.
Limited Initial Details, Followed by Widespread Technical Exposure
Following the initial disclosure, CrushFTP confirmed that the vulnerability had been reported responsibly and that, at the time, there was no evidence of active exploitation. However, the company opted not to share further technical details early on, likely as a precaution to prevent premature misuse.
In the days that followed, several security researchers and organizations independently analyzed the issue and published their findings. These technical reports included PoC exploit code, which soon became accessible to the broader public. The availability of these resources contributed to the vulnerability’s rapid weaponization, with attackers beginning to leverage the PoC code in observed exploitation attempts.
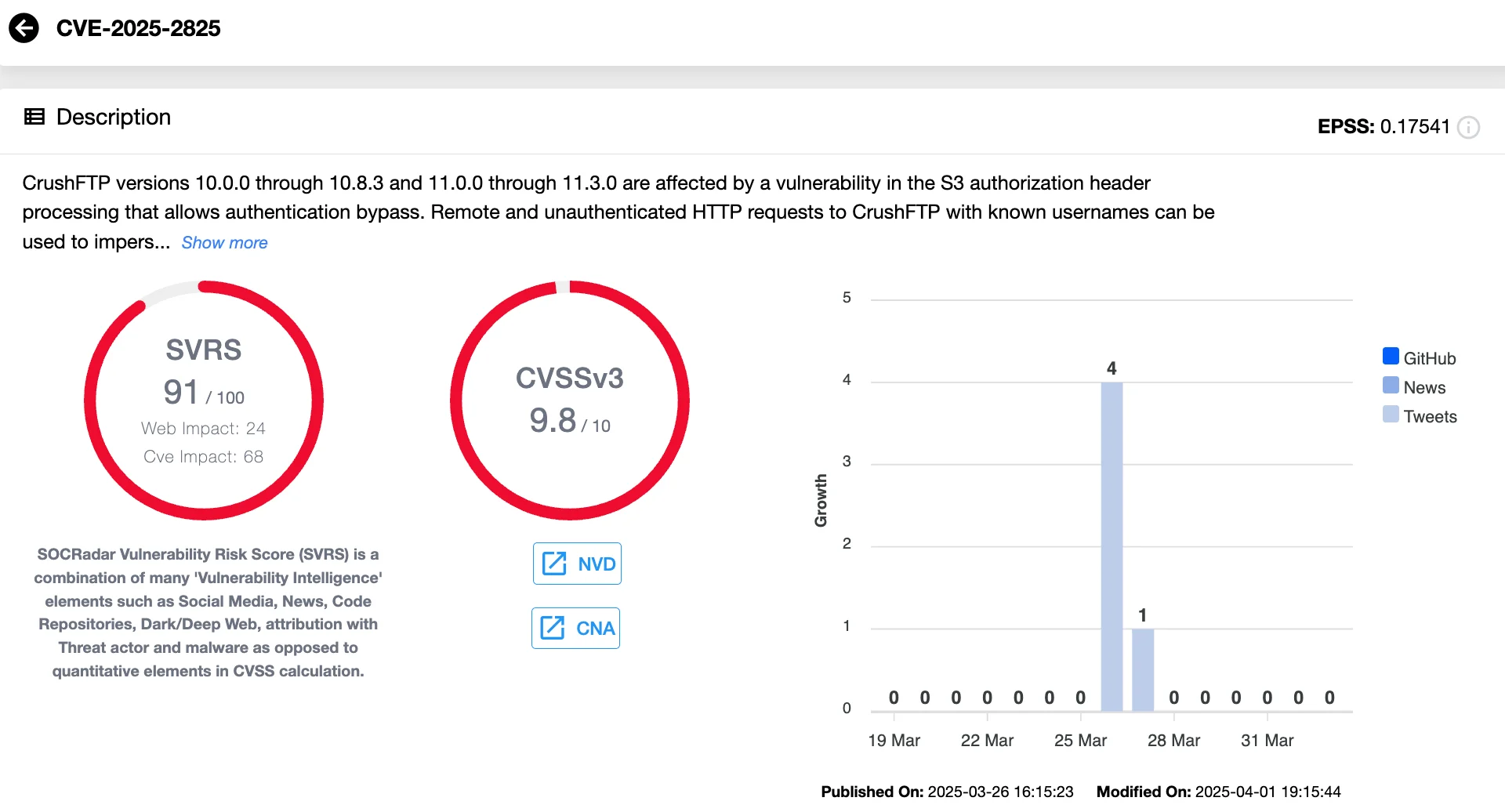
CVE Confusion: Which Identifier Is Official? CVE-2025-2825 or CVE-2025-31161
Initially, CrushFTP’s advisories for versions 10 and 11 did not include a CVE identifier for the authentication bypass vulnerability, even after patches had been issued. The changelog for the patched version, v11.3.1, still omits any mention of a CVE, adding to the uncertainty for users seeking official tracking information.
In the absence of an assigned identifier, VulnCheck, a recognized CVE Numbering Authority (CNA), stepped in to assign CVE-2025-2825. According to VulnCheck’s CTO, Jacob Baines, the decision was made after five days had passed without a CVE assignment from CrushFTP, and a courtesy notification was sent to the company. The move, however, prompted a response from the CEO, who stated that the “real” CVE was still pending.
CrushFTP later clarified that the official identifier for the vulnerability is CVE-2025-31161, attributed to research conducted by Outpost24. This CVE was reportedly assigned on March 26, but as of now, it has yet to appear in public databases such as the National Vulnerability Database. The lack of alignment between public disclosures and official records has left many in the security community seeking further clarity.
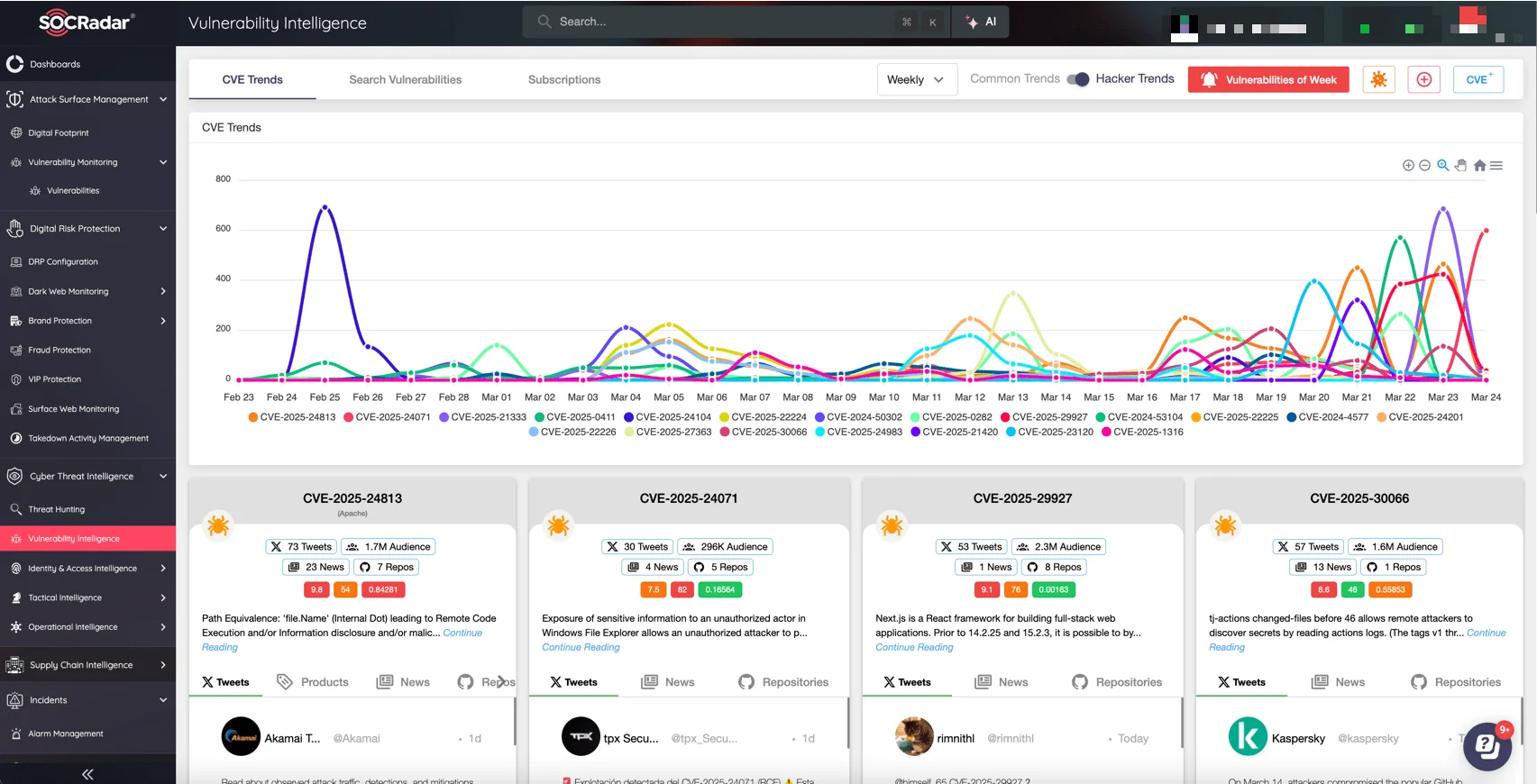
To effectively monitor and manage critical vulnerabilities like CVE-2025-31161, leverage SOCRadar’s Vulnerability Intelligence, part of the comprehensive Cyber Threat Intelligence module. SOCRadar provides early identification of actively exploited vulnerabilities, detailed insights on threat actor activities, and prioritized remediation recommendations based on real-world risks. Equip your team to swiftly move from vulnerability detection to protection, minimizing exposure and potential attacks.
Thousands of Servers Remain Exposed to CrushFTP Flaw
The vulnerability – initially identified as CVE-2025-2825 by VulnCheck and later recognized as CVE-2025-31161 – was reported by researchers at Outpost24. It enables remote, unauthenticated access to vulnerable CrushFTP servers through exposed HTTP(S) ports. In practical terms, attackers can bypass login protections entirely if the server hasn’t been patched.
On March 21, CrushFTP issued patches along with a direct advisory to customers urging immediate updates. The company stressed the severity of the issue, warning that any publicly accessible CrushFTP instance without proper safeguards could be compromised.
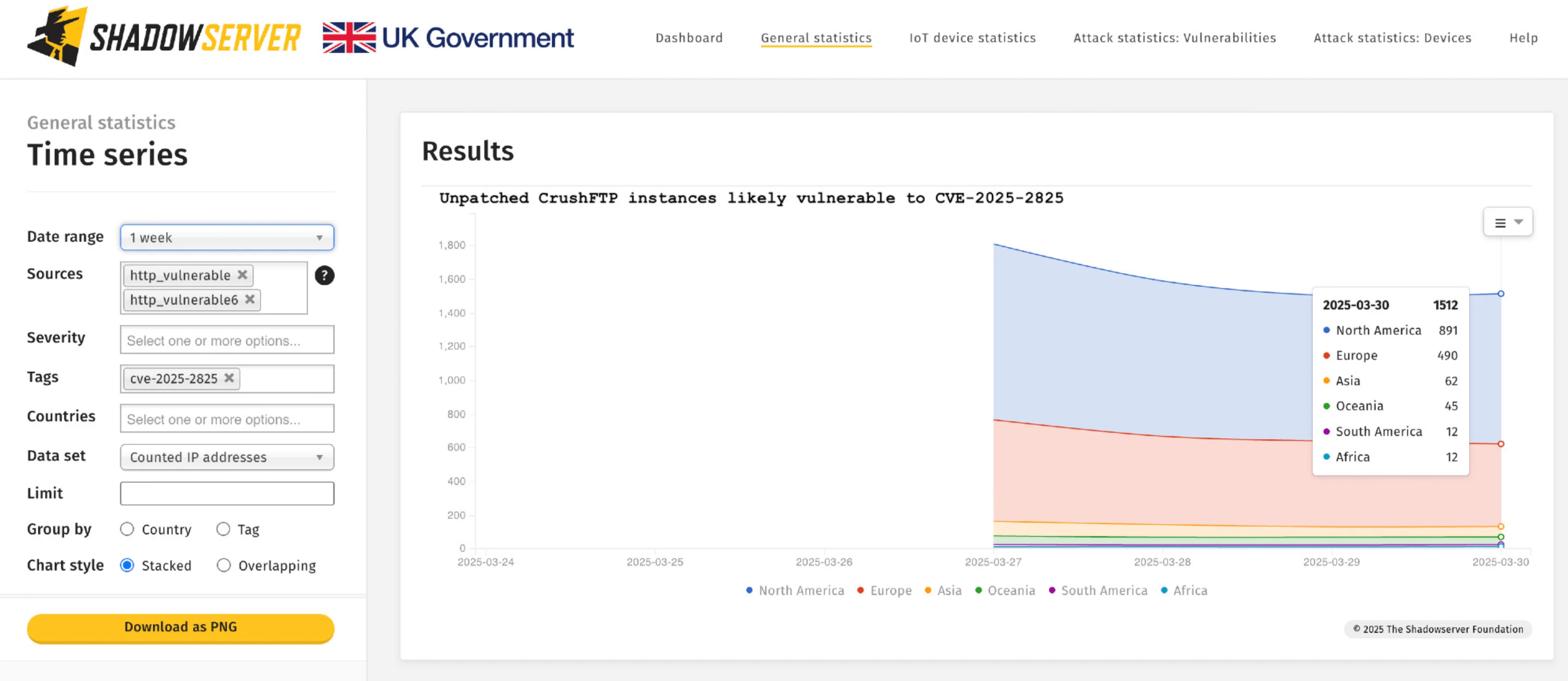
Despite the advisory, attacks began to surface rapidly. Within a week, Shadowserver Foundation reported active exploitation attempts detected through their honeypot network. Their findings revealed over 1,500 CrushFTP servers exposed online, with evidence that attackers were leveraging the publicly available PoC exploit shared by ProjectDiscovery.
Unpatched CrushFTP instances likely vulnerable to CVE-2025-2825 (Shadowserver)
By March 30, Shadowserver confirmed that 1,512 internet-facing instances remained unpatched, underlining a persistent gap between disclosure and widespread remediation.
CISA Flags Actively Exploited CrushFTP Vulnerability (CVE-2025-31161)
The Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2025-31161 to its Known Exploited Vulnerabilities (KEV) Catalog, following confirmed evidence of active exploitation.
This type of vulnerability, which allows attackers to bypass authentication controls, is commonly leveraged in cyberattacks and poses a serious threat, especially to federal systems. Agencies and enterprises using CrushFTP are advised to apply necessary mitigations before the compliance deadline of April 28, 2025, to reduce risk exposure.
Mitigation Steps and Interim Protections for CrushFTP Users
CrushFTP joins a list of enterprise file transfer tools that have attracted attention from cybercriminals due to their role in handling sensitive data and frequent external accessibility.
The currently exploited vulnerability, tracked as CVE-2025-31161, affects CrushFTP versions 10.0.0 through 10.8.3 and 11.0.0 through 11.3.0. It enables unauthenticated access via exposed HTTP(S) ports, making patching a top priority.
CrushFTP recommends upgrading to versions 10.8.4 or 11.3.1 to fully resolve the issue. For administrators unable to update immediately, enabling the DMZ perimeter network configuration offers a temporary safeguard by restricting access routes. Additionally, Rapid7 has published Indicators of Compromise (IOCs) to help security teams identify potential intrusions related to this flaw.
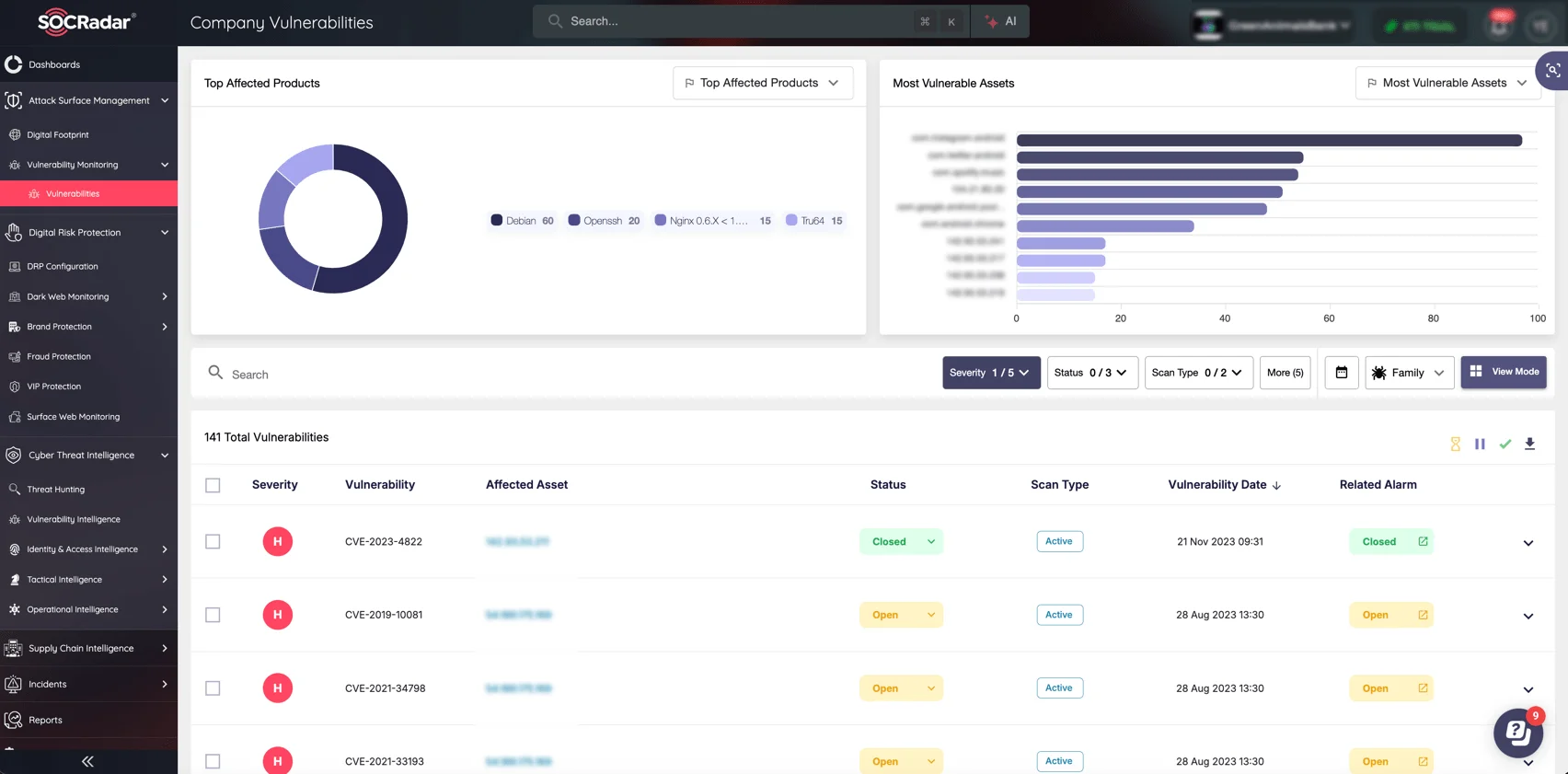
With vulnerabilities like the actively exploited CrushFTP flaw, knowing your exposure points is essential. SOCRadar’s Attack Surface Management (ASM) continuously maps your external-facing infrastructure, identifies vulnerable services like CrushFTP, and detects misconfigurations before attackers do. ASM gives your organization comprehensive visibility and real-time risk assessments, ensuring you can quickly pinpoint and secure critical assets against emerging threats.