

CVE-2023-33733 Vulnerability in ReportLab Allows Bypassing Sandbox Restrictions
A proof-of-concept (PoC) exploit and a technical write-up for a ReportLab vulnerability are now available. The vulnerability tracked as CVE-2023-33733 could allow an attacker to perform remote code execution (RCE).
The ReportLab toolkit is a popular Python library for generating PDFs from HTML. The library has around 3.5 million monthly downloads on PyPI.
The availability of a proof-of-concept and a write-up increases the probability of CVE-2023-33733 being exploited in the wild.
What is the CVE-2023-33733 Vulnerability?
The vulnerability arises because it is possible to bypass sandbox restrictions on the ‘rl_safe_eval’ function. The function prevents malicious code execution; ReportLab introduced the rl_safe_eval function as a patch in 2019 to address another RCE issue.
Yesterday, a researcher published a proof-of-concept exploit for CVE-2023-33733 and a write-up for its technical details on GitHub.
In the proof-of-concept exploit, the researcher worked to bypass the rl_safe_eval function because bypassing this patch could allow an attacker to access Python built-in functions and achieve remote code execution.
How Can the CVE-2023-33733 Be Exploited?
The proof of concept (PoC) demonstrates a technique where the ‘type’ function is exploited to create a new class called ‘Word,’ inheriting from the ‘str’ class. This allows bypassing safety checks and gaining access to sensitive attributes such as ‘__code__.’
By invoking ‘type’ on itself, the attacker can bypass evaluation checks restricting the number of arguments. This enables the malicious use of the original built-in ‘type’ function to create new classes and objects.
Consequently, the attacker can construct a harmful function using the bytecode of a compiled one. When executed, this function can perform arbitrary actions.
For example, in the researcher’s demonstration, it executes an operating system command to create a file named ‘exploited’ in the “/tmp/” directory.
To exploit the vulnerability, the entire malicious code must be executed with eval in a single expression. The ‘list comprehension’ trick is used to structure the code in this manner.
Cure53 researcher Elyas Damej warns in his report that exploiting CVE-2023-33733 is straightforward. Attackers can simply inject malicious code into an HTML file that will later be converted to PDF using software that relies on the ReportLab library.
Fix Available
Damej notified the developers of ReportLab about the issue, and a fix was included in version 3.6.13, which was released on April 27, 2023. It is important to note that all previous versions of the library are affected by this vulnerability.
Considering the widespread usage of this library and the availability of a public exploit, many users are at risk. Software vendors utilizing the library can mitigate the associated supply chain risk by applying the provided security update.
SOCRadar Helps Organizations Identify and Remediate Vulnerabilities
SOCRadar’s Vulnerability Intelligence provides organizations with real-time visibility into known and emerging vulnerabilities, as well as the potential impact of those vulnerabilities on their environment.
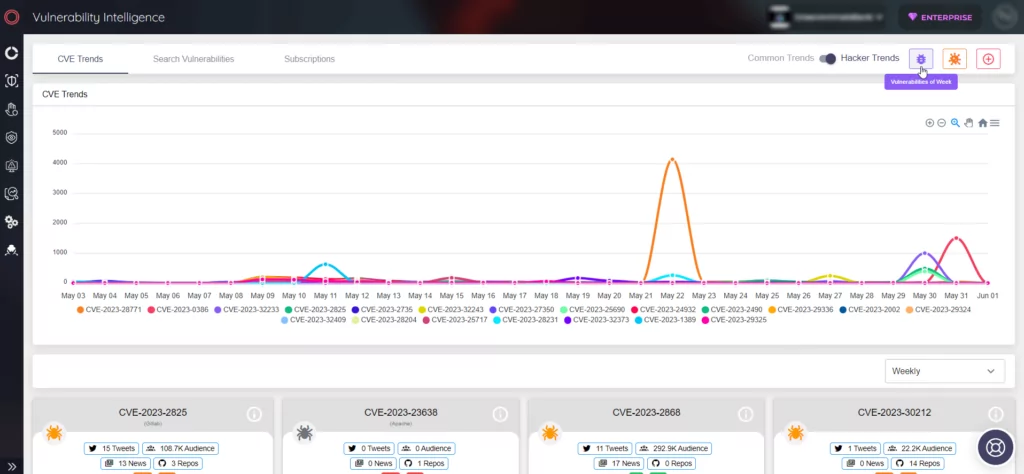
It includes a vulnerability scanner that continuously monitors assets for known vulnerabilities and a threat intelligence feed that provides information on how threat actors are exploiting vulnerabilities.
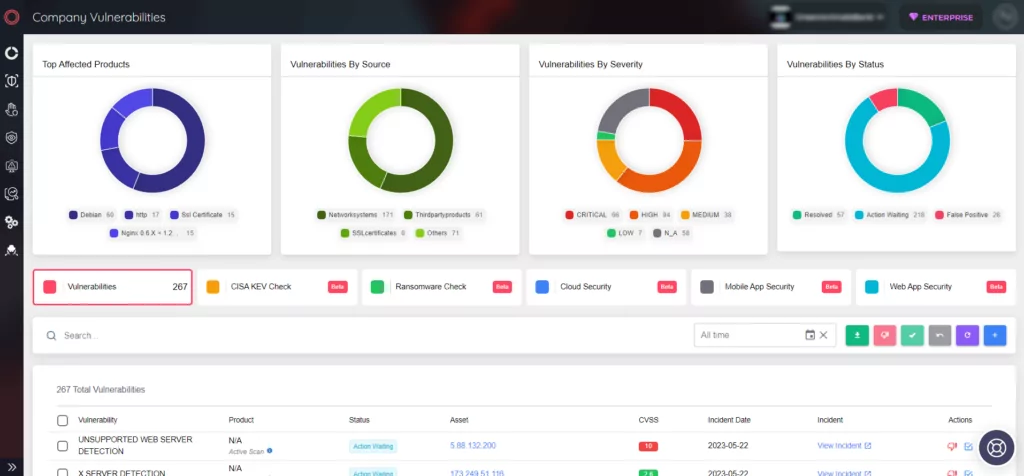
SOCRadar’s Vulnerability Intelligence can help organizations to:
- Identify and prioritize vulnerabilities
- Remediate vulnerabilities quickly and effectively
- Mitigate the risk of data breaches and other cyberattacks










