December 2023 Android Security Bulletin: Critical and Potentially Exploited Vulnerabilities, Google Pixel Update
Google has released the December 2023 Android Security Bulletin. Despite the bulletin being released, the awaited Google Pixel December update is yet to be made available.
In this Android security bulletin, dated December 5, 2023, Google is addressing a total of 85 vulnerabilities. The update includes three critical vulnerabilties, and numerous high severity issues, affecting components such as System, Arm, Imagination Technologies, MediaTek, Misc OEM, Unisoc, and Qualcomm.
It is worth noting that the security patch level assigned to the latest release, marked as 2023-12-05, also encompasses all the vulnerabilities addressed in the previous security patch level of 2023-12-01.
Critical Vulnerabilities of the December 2023 Android Security Bulletin
- CVE-2023-40088: This vulnerability affects the framework and allows attackers to perform Remote Code Execution (RCE) without requiring any user interaction, or any additional execution privileges.
- CVE-2023-45866: Another critical vulnerability, CVE-2023-45866, affects the System component. It has the potential to result in remote Escalation of Privilege, and it does not necessitate any additional execution privileges. User interaction is also not a prerequisite for exploitation.
Updated AOSP versions for these vulnerabilities are as follows: 11, 12, 12L, 13, and 14.
- CVE-2022-40507: CVE-2022-40507, categorized as a critical issue, resides in a Qualcomm component. Described as a memory corruption vulnerability, it stems from a double-free occurrence in Core while mapping HLOS address to the list. Initially disclosed in Qualcomm’s June 2023 security bulletin with a CVSS score of 8.4, it is now listed as a critical issue in the December 2023 Android Security Bulletin.
December 2023 Android Security Bulletin Alerts for Potentially Exploited Vulnerabilities
The December 2023 Android Security Bulletin issues an alert regarding potentially exploited vulnerabilities, stating that there are indications that vulnerabilities in Qualcomm’s subcomponents may be under limited, targeted exploitation. Furthermore, CISA has incorporated these vulnerabilities into the Known Exploited Vulnerabilities (KEV) Catalog upon evidence of exploitation.
The highlighted vulnerabilities involve memory corruption, and are tracked as CVE-2023-33107, CVE-2023-33106 (both in the Display subcomponent), and CVE-2023-33063 (in Kernel), all marked as high severity issues.
- CVE-2023-33107: This vulnerability involves memory corruption in Graphics Linux during the assignment of a shared virtual memory region in an IOCTL call.
- CVE-2023-33106: CVE-2023-33106 also points to a memory corruption, occurring when submitting a large list of sync points in an AUX command to the IOCTL_KGSL_GPU_AUX_COMMAND.
- CVE-2023-33063: In the case of CVE-2023-33063, the memory corruption occurs in DSP Services during a remote call from HLOS to DSP.
For more information about the remaining vulnerabilities in the update, visit the advisory here.
About the Delayed December 2023 Google Pixel Update
As is customary, every month sees the Android security bulletin accompanied by a Google Pixel update, delivering important patches and improvements. However, this time, there’s a notable deviation from the routine.
Google has declared that the forthcoming update for its Pixel devices will be a Pixel Feature Drop. Unfortunately, as of now, the company has not released a security bulletin outlining this month’s updates for Pixel devices, as it will be included in the Pixel Feature Drop.
The anticipated release for the Pixel Feature Drop is in this week.
Strengthening Vulnerability Management with SOCRadar
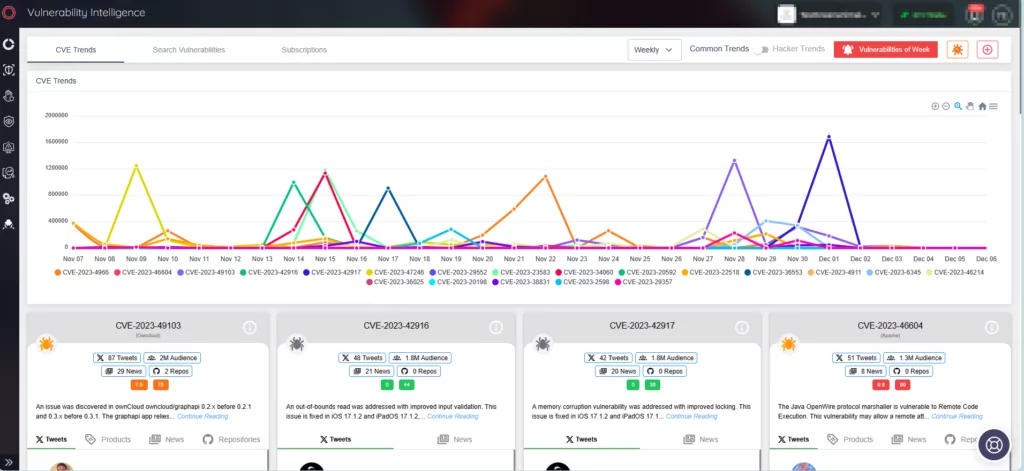
Utilize SOCRadar XTI to instantly receive alerts for critical vulnerabilities or exploits aimed at specific product components and technologies present in your digital landscape.
Moreover, SOCRadar’s Vulnerability Intelligence is a rich resource for vulnerability information, ensuring you stay updated on vulnerabilities targeted by threat actors. This tool provides practical insights and context, streamlining the vulnerability assessment procedures to strengthen your cybersecurity defenses.