‘Fullz,’ ‘Dumps,’ and More: What do Hackers Sell on the Black Market?
It’s easy to appreciate the importance hackers place on stolen bank accounts, credit cards, and social security numbers. Each of those products is a component of the ordinary person’s financial life. Its easy conversion to profit and products like Fullz, or Dumps in the hands of online black market dealers should come as no surprise. What many people may find disconcerting is that these are far from the only kind of data that may be sold for profit.
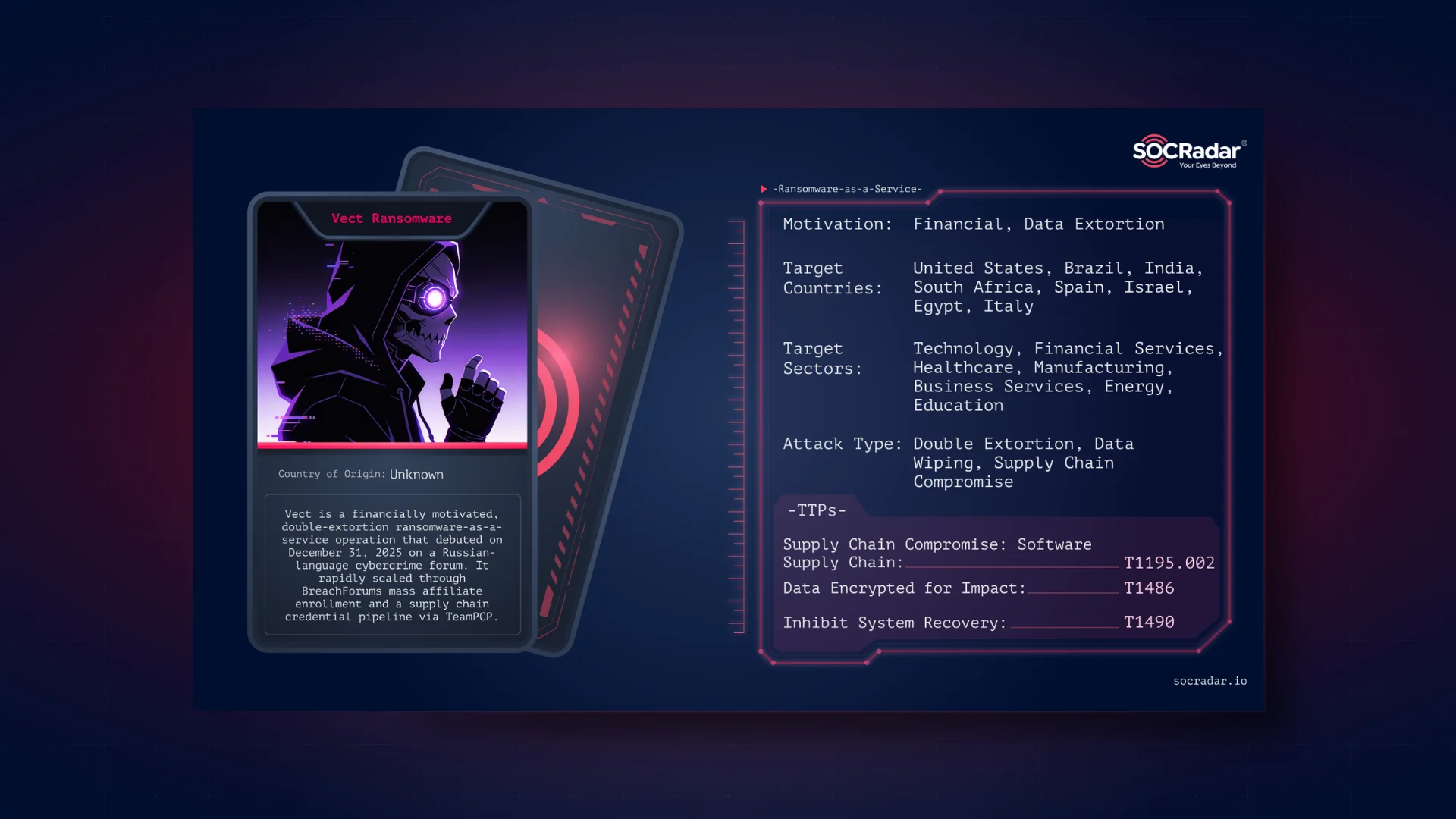
While some hackers are content with merely stealing personal information and wreaking havoc on individuals or organizations, the vast majority do it for financial gain.
Hackers work in an underground economy replete with forums, chat rooms, blogs, and other groups dedicated to facilitating, streamlining, and industrializing criminality. Examining what is sold and traded in these networks might provide us with a solid idea of what is most valuable to hackers — and what we should safeguard.
What is Fullz?

Fullz is fraudster slang meaning financial information that contains the victim’s complete identity, address, credit card information, social security number, and date of birth, among other things. As a general rule, the more information you know about your victim, the more money you may get off their credentials. While Fullz is often more expensive than basic credit card credentials, they typically cost less than $100 per record. Fullz may be paid out in various methods, including by executing bank transactions over the phone while holding the relevant authentication data.
Even Dead Fullz, which are Fullz credentials associated with expired credit cards, can be used for a variety of purposes, including tax refund scams, ordering credit cards on the victim’s behalf, or opening a mule account (a bank account that accepts fraudulent money transfers from a compromised account) without the victim’s knowledge. Due to their difficulty in cashing out, Dead Fullz often cost between $1 and $3 apiece.
Credit Cards
In the hacker economy, the credit card information is the most often traded commodity. This data is available in various formats, the most common of which being “CVVs” and “dumps.”
CVV, not to be confused with the three numbers on the back of a credit card, is fraudster jargon for credit card records that may contain the cardholder’s name and address, the card number, the expiration date, and CVV2 (the three digits on the back of a card). CVVs are exclusively valid for online businesses and are typically available for less than $10 on one of the underground markets (for U.S. cards).
What is Dumps?

Dumps is fraudster slang for the raw data on a credit card’s magnetic strip. It may be obtained in various ways, including physically skimming the card, collecting the data via malware-infected point-of-sale equipment, or hacking into a retailer’s internal network.
Dump data may be encoded onto a bogus credit card, which hackers can then use to make transactions at a brick-and-mortar business. While costs vary according to card type and expiration period, they are often more expensive than CVVs since the payout is greater. Hackers may use them to purchase products worth more than the CVV allows. Dump data for credit cards issued in the United States costs between $20 and $80.
What is Kitz?

Complete kit of forged identification and credential documents, or Kitz: Includes custom-made physical credentials and paperwork relating to the identity information obtained via Fullz. It develops into a comprehensive identity theft kit, replete with forged insurance cards, social security cards, driver’s licenses, and credit cards.
Healthcare Data
Numerous healthcare institutions do not encrypt data on their internal networks. Additionally, they do not encrypt data in transit or at rest. This is of interest to hackers due to the enormous attack surface area. Health insurance information can be used to acquire illegally resold pharmaceuticals or medical equipment or even obtain medical care. The latter can have far-reaching repercussions beyond the pecuniary.
Why are Hackers Putting Different Names on What They are Selling on the Darknet?
Hackers on the darknet demonstrate their digital marketing prowess by repeatedly putting the same products up for sale under different names and accounts. Therefore it is impossible not to see duplicate items with different names in darknet markets.