IcedID Macro Attacks Deploy Nokoyawa Ransomware
Malicious actors frequently resort to alternative techniques to gain initial access, such as employing diverse file formats and payloads. It is important to highlight that they still actively use VBA macros embedded within Office documents to infiltrate target systems.
Microsoft has addressed the issue by blocking macros by default in documents downloaded from the internet; however, malicious actors can still exploit organizations that have not updated their Microsoft Office installations.
During Q4 of 2022, threat actors targeted Italian organizations using malicious Excel documents that deploy IcedID. After gaining access, the threat actors used Cobalt Strike and RDP (Remote Desktop Protocol) to pivot and eventually deployed Nokoyawa ransomware across the entire domain using PsExec.
Threat Actors Delivered IcedID Payload via Malicious Excel Documents
Researchers from the DFIR Report have observed attacks that commenced with a malicious Excel document, possibly delivered during a malicious email campaign in October 2022. The macros would be executed when a user clicks on an embedded image in the Excel document. The purpose of the macro code was to download an IcedID DLL payload on disk. The macro then executed the IcedID DLL using a renamed rundll32 binary.
Once establishing the connection to the command and control (C2) server, the IcedID malware initiated automated discovery procedures; remarkably, the malware employed the same Microsoft binaries researchers have previously reported for the IcedID family. Furthermore, the malware created a scheduled task on the compromised host to ensure persistence.
Conducting Reconnaissance With Cobalt Strike
After its initial execution, the IcedID malware loaded several Cobalt Strike beacons on the compromised host. The beacons enabled the threat actors to elevate their privileges to SYSTEM and extract the LSASS (Local Security Authority Subsystem Service) memory. The threat actors expanded their scope after this activity by conducting further reconnaissance and moving laterally to a Domain Controller, using a Cobalt Strike payload delivered via WMI (Windows Management Instrumentation).
Subsequent to establishing their presence on the compromised host, the threat actors initiated discovery tasks that included network scans targeting port 1433 (MSSQL) and exploring network shares, with a particular interest in obtaining password files. The threat actors selectively removed certain contents from these network shares; researchers state this was evidenced by canary files being accessed off the network shortly afterward. Threat actors kept a low profile after the activity for several days.
Threat Actor’s Progression: Discovery and Lateral Movement
The threat actors returned to gather information about domain computers and privileged user accounts on the Domain Controller. They also escalated privileges using named pipe impersonation.
Later, they resumed their activities by downloading a file from dropmefiles[.]com after launching the Edge browser on the infected host. They remained quiet for about eight hours but then started enumerating the Active Directory using adget and AdFind through the IcedID malware.
Next, the threat actors began spreading laterally through the network, utilizing a combination of Cobalt Strike beacon DLLs, batch scripts, and WMI (Windows Management Instrumentation) commands. They engaged in credential dumping, executed additional Windows discovery commands, and checked RDP access across the environment. A batch file was employed to conduct hostname enumeration via nslookup. Throughout the day, the threat actors continued to pivot and perform targeted discovery on various systems.
Final Phase: Nokoyawa Ransomware Deployment and Contact with Threat Actors
After approximately 23 hours of inactivity, the threat actors initiated the final phase of the intrusion. They connected to a compromised server via RDP, utilizing it as a staging ground for the ransomware deployment. The actors deployed the ransomware payload, Sysinternals PsExec, and a cluster of batch files (1.bat-6.bat and p.bat). By executing these batch files through PsExec and WMI, they distributed the ransomware payload to all domain joined hosts.
The time from the initial infection to the execution of ransomware (TTR) amounted to around 148 hours. Following the intrusion, contact was established with the threat actors through their support site, where they demanded a ransom of approximately $200,000 USD in Bitcoin. However, no ransom was paid as a result of this incident.
You can find more information about the incident and related indicators of compromise here.
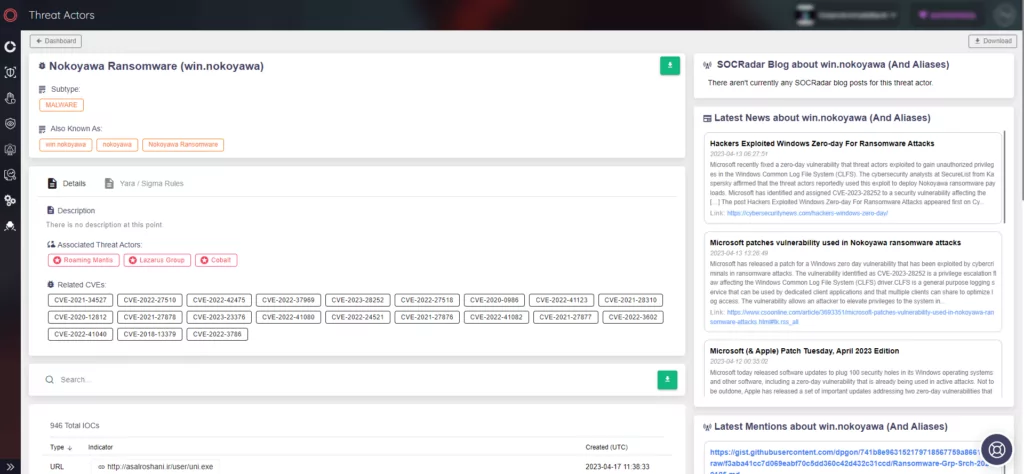
Protecting Your Organization Against Threat Actors and Malware with SOCRadar
SOCRadar actively monitors threat actors and malware to deliver crucial information for protecting your organization. The Threat Actor/Malware tab provides up-to-date details on threat activities and indicators of compromise.