
Major Cyber Attacks in Review: December 2023
In December 2023, the digital world witnessed a series of significant cyberattacks that echoed across multiple industries. These incidents, some of them spearheaded by well-known threat actors such as BlackCat (ALPHV) Ransomware, KillNet, Cyber Av3ngers, Cyber Toufan, and BidenCash, served as vivid examples of the importance of strengthening our digital defenses and protecting our data.
In this blog post, we will delve into the significant cyberattacks that unfolded in December 2023, examining their consequences to extract valuable lessons for enhancing future cybersecurity efforts.
Approximately 60 Credit Unions Affected by Ongoing Operations Ransomware Attack

A ransomware attack on cloud IT provider Ongoing Operations, owned by Trellance, has disrupted services for approximately 60 credit unions across the US, as confirmed by the National Credit Union Administration (NCUA).
The incident, believed to have exploited the Citrix Bleed vulnerability, has caused days of disruption for Ongoing Operations’ clients, with Mountain Valley Federal Credit Union among those experiencing system downtime.
Tipalti Targeted in ALPHV/BlackCat Ransomware Attack: Over 265 GB of Data Compromised

In early December 2023, the ALPHV/BlackCat ransomware group, known for sophisticated cyber attacks, targeted Tipalti, a prominent FinTech company specializing in automated payment processing services.
The breach, revealed on September 8th, compromised over 265GB of sensitive business data, affecting Tipalti and its high-profile clients, including Roblox and Twitch.
You can read more about this incident on our blog post: ALPHV/BlackCat Ransomware Attack on Tipalti, Threatening Tipalti’s Customers
Kyivstar Cyberattack Disrupted Services for Half of Ukraine’s Mobile Subscribers

Kyivstar Cyberattack Disrupted Services for Half of Ukraine’s Mobile Subscribers
Ukrainian telecom operator Kyivstar suffered a cyberattack, causing disruptions in internet access and mobile communications. The incident coincided with Ukrainian President Volodymyr Zelenskyy’s visit to Washington to seek additional military aid.
While Kyivstar assured that subscribers’ personal data remains uncompromised, market analysis firm Telegeography estimated that around half of Ukraine’s mobile subscriber base, served by Kyivstar, was affected. CEO Oleksandr Komarov did not directly attribute the attack to Russian state hackers but suggested it as a likely source.
The outage led to malfunctions in air raid sirens, affecting military alerts, and disrupted credit card payments and ATM access in retail shops nationwide. The Russian hacktivist group KillNet claimed responsibility, but cybersecurity experts cast doubt on the legitimacy of the assertion.
GUR Claimed Cyberattack on Russian Tax Service: Over 2,300 Regional Servers Potentially Affected

In December 2023, Ukraine’s defense intelligence directorate (GUR) claimed responsibility for a cyberattack on Russia’s state tax service, claiming to have infected thousands of servers, including a key well-protected central server and over 2,300 regional servers.
The operation allegedly led to the complete destruction of the agency’s infrastructure, including critical configuration files supporting Russia’s tax system. GUR alleged a month-long paralysis of the Federal Tax Service (FNS) and a halt in internet connections between the central office and regional branches.
While these claims are unverified and not acknowledged by Russia or FNS, the alleged impact remains significant.
Delta Dental’s MOVEit Data Breach Exposed Approximately 7M Patients

Delta Dental of California, a dental insurance provider, disclosed a data breach affecting 6,928,932 patients due to unauthorized access through the MOVEit file transfer software.
The incident ranks as the third-largest MOVEit breach by Cl0p Ransomware, after Maximus and Welltok breaches.
Delta Dental detected the compromise on June 1, 2023, confirming unauthorized access and data theft between May 27 and May 30, 2023. The breach exposed names, financial account numbers, and credit/debit card details, including security codes.
Mr. Cooper Cyberattack Exposed Nearly 15M Individuals’ Personal Information
Mr. Cooper, the largest nonbank mortgage servicer in the U.S., disclosed that an October 2023 cyber attack resulted in the exposure of personal information for 14,690,284 individuals. The company faced a technical outage in November, impacting customers attempting to make payments.
Following an investigation, Mr. Cooper revealed unauthorized access to its systems between October 30 and November 1, 2023. The compromised data included names, addresses, phone numbers, Social Security numbers, dates of birth, and bank account numbers.
While the company did not confirm if it was a ransomware attack, it took measures to contain the incident and safeguard customer information.
Xfinity Customer Data Compromised in Citrix Server Breach

Comcast Cable Communications (Xfinity) has revealed that sensitive customer information was compromised in the wake of a Citrix server breach in October.
Suspicious activities within Xfinity’s network were identified from October 16 to 19, leading to the discovery that attackers had exfiltrated certain customer data. Following an investigation, Xfinity confirmed on December 6, 2023, that the exfiltrated customer data included usernames and hashed passwords, potentially encompassing names, contact details, the last four digits of Social Security numbers (SSNs), birthdates, and security questions.
Xfinity promptly addressed the vulnerability tracked as CitrixBleed, urging customers to reset passwords as a precautionary measure.
Read more about the CitrixBleed vulnerability (CVE-2023-4966) on SOCRadar: Zero-Day Vulnerabilities in Citrix NetScaler and WinRAR Are Under Active Exploitation (CVE-2023-4966, CVE-2023-38831)
Ransomware Attack on ESO Solutions Led to Supply-Chain Compromise: 2.7M Patients Affected

ESO Solutions, a healthcare software provider, suffered a ransomware attack on September 28, compromising data of 2.7 million patients, and leading to a supply-chain issue.
The hackers exfiltrated data before encrypting company systems, affecting patients associated with U.S. hospitals and clinics that are customers of ESO. The breached information includes full names, dates of birth, phone numbers, medical records, diagnosis and treatment details, and Social Security Numbers (SSNs).
The affected customers were notified in December, and impacted hospitals, such as Mississippi Baptist Medical Center and Providence St Joseph Health, initiated breach notices to patients.
BidenCash Leaked 1.9M Credit Card Details
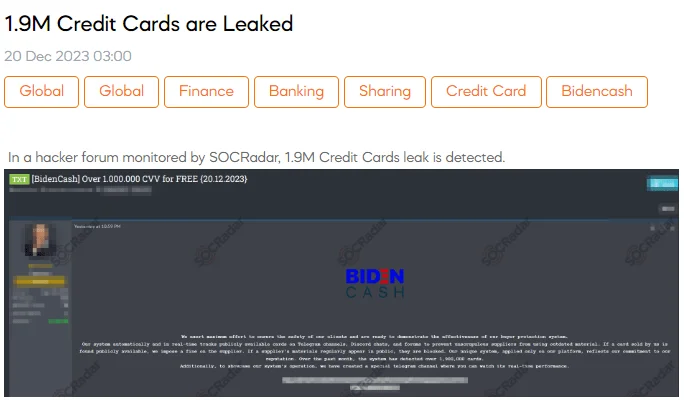
The SOCRadar Dark Web Team has identified a significant data breach on a hacker forum, uncovering the exposure of 1.9 million credit card details by BidenCash, a carding market established in June 2022.
BidenCash revealed the 1.9 million credit card numbers in December 2023, on a hacker forum, also asserting the implementation of a buyer protection system. The system, as mentioned in the threat actor’s post, aims to ensure data freshness and penalize suppliers for outdated materials through real-time tracking – an indication of an evolution in the underground market.
Such leaks pose a serious threat, potentially leading to unauthorized transactions, financial losses, and an increased risk of identity theft for affected individuals.
Discover the details of the latest BidenCash data leak in the following SOCRadar blog post: Massive Data Leak by BidenCash: 1.9M Credit Card Details Exposed on Hacker Forum
LoanCare Data Breach: Over 1.3 Million Individuals Affected Amid Real Estate Transaction Disruptions
In late December 2023, LoanCare, a subsidiary of Fidelity National Financial, reported a data breach to regulators following a cyberattack in November, which was claimed by the ALPHV/Blackcat ransomware gang.
The breach affected 1,316,938 individuals, and caused significant disruptions to real estate transactions for several days, with unauthorized access to certain systems within Fidelity National Financial’s network. Information including names, addresses, Social Security numbers, and loan numbers was obtained by the threat actors.
It is also important to note that, shortly after this incident, ALPHV’s data leak site was seized by a law enforcement operation. For details, visit our blog post titled “ALPHV Seized, Unseized, Decrypted; Pandora’s Box May Be Reopened.”
Cyber Av3ngers Allegedly Breached Israel’s Electricity Infrastructure Data

In December 2023, the Cyber Av3ngers hacker group claimed to be selling 1TB of data from Israel’s electricity infrastructures. The asking price for the dataset is set at 5 BTC, and the announcement was made on the platform “DAILY PARK WEB.”
The group provided proof files on Twitter containing information about Combined Cycle Gas Turbine (CCGT), aerial maps of power plants, blueprints of power supply, and other critical details. However, the authenticity of their claims has not been verified.
You can find detailed information about the operations and Tactics, Techniques, and Procedures (TTPs) of Cyber Av3ngers on our Dark Web Profile post.
Cyber Toufan Claimed to Have Breached 60+ Victims, Including SpaceX, Toyota, IKEA
Amid the ongoing conflict in Gaza, a pro-Palestinian hacking group named Cyber Toufan claims to have executed dozens of data breaches against Israeli entities.
The group initiated the operation in late November, and by the end of December, the group asserted that it had successfully breached and disclosed data from 60 sites. The targets span organizations from various industries, including cybersecurity firms, government agencies, and more, including Israeli and foreign companies like SpaceX, Toyota, and IKEA.
Detailed information about Cyber Toufan’s operations and Tactics, Techniques, and Procedures (TTPs) can be found in our Dark Web Profile post.




































